mirror of
https://github.com/openappsec/openappsec.git
synced 2025-11-15 17:02:15 +03:00
Compare commits
109 Commits
0.8.0-rc
...
Dec-24-202
| Author | SHA1 | Date | |
|---|---|---|---|
|
|
6a7c2402a5 | ||
|
|
c4d7ab54a6 | ||
|
|
1eee88cba5 | ||
|
|
d91a1c4ca5 | ||
|
|
596033391b | ||
|
|
eb1bc9227b | ||
|
|
3084641737 | ||
|
|
3282774432 | ||
|
|
de31400712 | ||
|
|
8d0a44acac | ||
|
|
d526a070a4 | ||
|
|
b71d772e7a | ||
|
|
62e75b8739 | ||
|
|
16ad370409 | ||
|
|
7bf05192b3 | ||
|
|
287cef8c36 | ||
|
|
2649b84207 | ||
|
|
a3014ab381 | ||
|
|
9d848264f3 | ||
|
|
cfcf7b883e | ||
|
|
2da3dc4052 | ||
|
|
4084cb4f6d | ||
|
|
3eb17167cb | ||
|
|
b2781d63d4 | ||
|
|
7f712b21e4 | ||
|
|
331c24acb0 | ||
|
|
bc3359a1c1 | ||
|
|
cec0276df1 | ||
|
|
3061342b45 | ||
|
|
0869b8f24d | ||
|
|
1a4ab5f0d7 | ||
|
|
4a2d25ab65 | ||
|
|
f2ca7301b9 | ||
|
|
3d11ead170 | ||
|
|
39b8c5a5ff | ||
|
|
de6f1033bd | ||
|
|
58958b2436 | ||
|
|
59e7f00b3e | ||
|
|
e102b25b7d | ||
|
|
0386431eee | ||
|
|
fd1a77628e | ||
|
|
da911582a5 | ||
|
|
798dd2a7d1 | ||
|
|
6bda60ae84 | ||
|
|
5b9769e94e | ||
|
|
6693176131 | ||
|
|
c2ced075eb | ||
|
|
0b4bdd3677 | ||
|
|
d6599cc7bc | ||
|
|
4db7a54c27 | ||
|
|
f3ede0c60e | ||
|
|
79bac9f501 | ||
|
|
89263f6f34 | ||
|
|
5feb12f7e4 | ||
|
|
a2ee6ca839 | ||
|
|
1c10a12f6f | ||
|
|
e9f6ebd02b | ||
|
|
433c7c2d91 | ||
|
|
582791e37a | ||
|
|
a4d1fb6f7f | ||
|
|
dfbfdca1a9 | ||
|
|
36f511f449 | ||
|
|
f91f283b77 | ||
|
|
7c762e97a3 | ||
|
|
aaa1fbe8ed | ||
|
|
67e68c84c3 | ||
|
|
149a7305b7 | ||
|
|
ea20a51689 | ||
|
|
19f2383ae2 | ||
|
|
4038c18bda | ||
|
|
a9b6d2e715 | ||
|
|
81c75495cc | ||
|
|
5505022f47 | ||
|
|
b25fd8def5 | ||
|
|
702c1184ea | ||
|
|
b3cfd7e9d8 | ||
|
|
e36b990161 | ||
|
|
09868e6d7c | ||
|
|
e25f517c19 | ||
|
|
42a31e37b1 | ||
|
|
abe275c828 | ||
|
|
71d198f41a | ||
|
|
3ed569fe35 | ||
|
|
c7cb494e2b | ||
|
|
edd357f297 | ||
|
|
08583fdb4c | ||
|
|
e5ef6c5ad4 | ||
|
|
3c24666643 | ||
|
|
19e8906704 | ||
|
|
01b6544ca5 | ||
|
|
ebc2b2be0d | ||
|
|
fc6355a3b2 | ||
|
|
c89001b6e0 | ||
|
|
a59f079ef7 | ||
|
|
22f1a984aa | ||
|
|
7c98ba9834 | ||
|
|
5192380549 | ||
|
|
a270456278 | ||
|
|
795d07bd41 | ||
|
|
45e51ddbf7 | ||
|
|
36f65b9b1f | ||
|
|
dfcc71c8c2 | ||
|
|
1e8540f166 | ||
|
|
a754082405 | ||
|
|
3aa0885f74 | ||
|
|
3b49cfec54 | ||
|
|
d7494b1bbc | ||
|
|
29bd82d125 | ||
|
|
c49debe5d9 |
2
.gitattributes
vendored
Normal file
2
.gitattributes
vendored
Normal file
@@ -0,0 +1,2 @@
|
||||
build_system/docker/install-cp-agent-intelligence-service.sh binary
|
||||
build_system/docker/install-cp-crowdsec-aux.sh binary
|
||||
@@ -1,7 +1,12 @@
|
||||
cmake_minimum_required (VERSION 2.8.4)
|
||||
project (ngen)
|
||||
|
||||
set(CMAKE_CXX_FLAGS "${CMAKE_CXX_FLAGS} -fPIC -Wall -Wno-terminate -Dalpine")
|
||||
set(CMAKE_CXX_FLAGS "${CMAKE_CXX_FLAGS} -fPIC -Wall -Wno-terminate")
|
||||
|
||||
execute_process(COMMAND grep -c "Alpine Linux" /etc/os-release OUTPUT_VARIABLE IS_ALPINE)
|
||||
if(NOT IS_ALPINE EQUAL "0")
|
||||
set(CMAKE_CXX_FLAGS "${CMAKE_CXX_FLAGS} -Dalpine")
|
||||
endif()
|
||||
|
||||
find_package(Boost REQUIRED)
|
||||
find_package(ZLIB REQUIRED)
|
||||
@@ -28,6 +33,7 @@ include_directories(core/include/services_sdk/interfaces)
|
||||
include_directories(core/include/services_sdk/resources)
|
||||
include_directories(core/include/services_sdk/utilities)
|
||||
include_directories(core/include/attachments)
|
||||
include_directories(events/include)
|
||||
include_directories(components/include)
|
||||
|
||||
add_subdirectory(build_system)
|
||||
|
||||
@@ -1,37 +1,64 @@
|
||||
# open-appsec Contributing Guide
|
||||
Thank you for your interest in open-appsec. We welcome everyone that wishes to share their knowledge and expertise to enhance and expand the project.
|
||||
# open-appsec Contributing Guide🌴
|
||||
|
||||
Read our [Code of Conduct](./CODE_OF_CONDUCT.md) to keep our community approachable and respectable.
|
||||
Thank you for your interest in open-appsec. We welcome contributions of all kinds, there is no need to do code to be helpful! All of the following tasks are noble and worthy contributions that you can make without coding:
|
||||
|
||||
In this guide we will provide an overview of the various contribution options' guidelines - from reporting or fixing a bug, to suggesting an enhancement.
|
||||
- Reporting security vulnerabilities
|
||||
- Reporting a bug
|
||||
- Helping a member of the community
|
||||
- Notes about our documentation
|
||||
- Providing feedback and feature requests
|
||||
|
||||
Before making any kind of contribution, read our [Code of Conduct](./CODE_OF_CONDUCT.md) to keep our community approachable and respectable.
|
||||
|
||||
This guide will provide an overview of the various contribution options' guidelines - from reporting or fixing a bug to suggesting an enhancement.
|
||||
|
||||
## Reporting security vulnerabilities
|
||||
|
||||
If you've found a vulnerability or a potential vulnerability in open-appsec please let us know at [security-alert@openappsec.io](mailto:security-alert@openappsec.io). We'll send a confirmation email to acknowledge your report within 24 hours, and we'll send an additional email when we've identified the issue positively or negatively.
|
||||
If you've found a vulnerability or a potential vulnerability in open-appsec please let us know at [security-alert@openappsec.io](mailto:security-alert@openappsec.io). We'll send a confirmation email to acknowledge your report within 24 hours and send an additional email when we've identified the issue positively or negatively.
|
||||
|
||||
An internal process will be activated upon determining the validity of a reported security vulnerability, which will end with releasing a fix and deciding on the applicable disclosure actions. The reporter of the issue will receive updates of this process' progress.
|
||||
An internal process will be activated upon determining the validity of a reported security vulnerability, which will end with releasing a fix and deciding on the appropriate disclosure actions. The reporter of the issue will receive updates on this process' progress.
|
||||
|
||||
## Reporting a bug
|
||||
|
||||
**Important - If the bug you wish to report regards a suspicion of a security vulnerability, please refer to the "Reporting security vulnerability" section**
|
||||
**Important - If the bug you wish to report regards a suspicion of a security vulnerability, please refer to the [Reporting security vulnerability](#Reporting-security-vulnerabilities) section**
|
||||
|
||||
To report a bug, you can either open a new issue using a relevant [issue form](https://github.com/github/docs/issues/new/choose), or, alternatively, [contact us via our open-appsec open source distribution list](mailto:opensource@openappsec.io).
|
||||
To report a bug, you can either open a new issue using a relevant [issue form](https://github.com/github/docs/issues/new/choose) or, [contact us via our open-appsec open source distribution list](mailto:opensource@openappsec.io).
|
||||
|
||||
Be sure to include a **title and clear description**, as much relevant information as possible, and a **code sample** or an **executable test case** demonstrating the expected behavior that is not occurring.
|
||||
|
||||
## Contributing a fix to a bug
|
||||
|
||||
Please [contact us via our open-appsec open source distribution list](mailto:opensource@openappsec.io) before writing your code. We will want to make sure we understand the boundaries of the proposed fix, that the relevant coding style is clear for the proposed fix's location in the code, and that the proposed contribution is relevant and eligible.
|
||||
Please [contact us via our open-appsec open source distribution list](mailto:opensource@openappsec.io) before writing your code. We will want to make sure we understand the boundaries of the proposed fix, that the relevant coding style is clear for the proposed fix's location in the code, and that the suggested contribution is relevant and eligible.
|
||||
|
||||
Once you've received our confirmation follow the next steps:
|
||||
|
||||
1. Fork the repository to your GitHub account.
|
||||
2. Clone your forked repository to your local machine.
|
||||
3. Add your contributions to relevant locations in the local copy of the codebase.
|
||||
4. Push your changes back to your forked repository.
|
||||
5. Open a pull request (PR) against the main branch of the original repository.
|
||||
|
||||
## Contributing code-independent enhancements
|
||||
|
||||
For any code-independent enhancements (such as docker-compose files, or instructions on how to compile on different OSs) please follow the next steps:
|
||||
1. [suggest your change via our open-appsec open-source distribution list](mailto:opensource@openappsec.io) to inform us about your possible contribution and wait for our confirmation.
|
||||
2. Fork the repository to your GitHub account.
|
||||
3. Clone your forked repository to your local machine.
|
||||
4. Add your contributions to the "contrib" Folder in the local copy of the codebase.
|
||||
5. Push your changes back to your forked repository.
|
||||
6. Open a pull request (PR) against the main branch of the original repository.
|
||||
|
||||
Please note that during the PR review we might adjust the location of the contributions.
|
||||
|
||||
## Proposing an enhancement
|
||||
|
||||
Please [suggest your change via our open-appsec open source distribution list](mailto:opensource@openappsec.io) before writing your code. We will contact you to make sure we understand the boundaries of the proposed fix, that the relevant coding style is clear for the proposed fix's location in the code, and that the proposed contribution is relevant and eligible. There may be additional considerations that we would like to discuss with you before implementing the enhancement.
|
||||
Please [suggest your change via our open-appsec open-source distribution list](mailto:opensource@openappsec.io) before writing your code. We will contact you to make sure we understand the boundaries of the proposed fix, that the relevant coding style is clear for the proposed fix's location in the code, and that the suggested contribution is relevant and eligible. There may be additional considerations that we would like to discuss with you before implementing the enhancement.
|
||||
|
||||
## Open Source documentation issues
|
||||
|
||||
For reporting or suggesting a change, of any issue detected in the documentation files of our open source repositories, please use the same guidelines as bug reports/fixes.
|
||||
to propose changes to our [documentation](https://docs.openappsec.io/?utm_medium=web&utm_source=wix&utm_content=top_menu) you can either open a new issue using a relevant [issue form](https://github.com/github/docs/issues/new/choose) or, [contact us via our open-appsec open source distribution list](mailto:opensource@openappsec.io).
|
||||
|
||||
# Final Thanks
|
||||
We value all efforts to read, suggest changes and/or contribute to our open source files. Thank you for your time and efforts.
|
||||
# Final thanks
|
||||
We value all efforts to read, suggest changes, and/or contribute to our open-source files. Thank you for your time and efforts.
|
||||
|
||||
The open-appsec Team
|
||||
|
||||
44
README.md
44
README.md
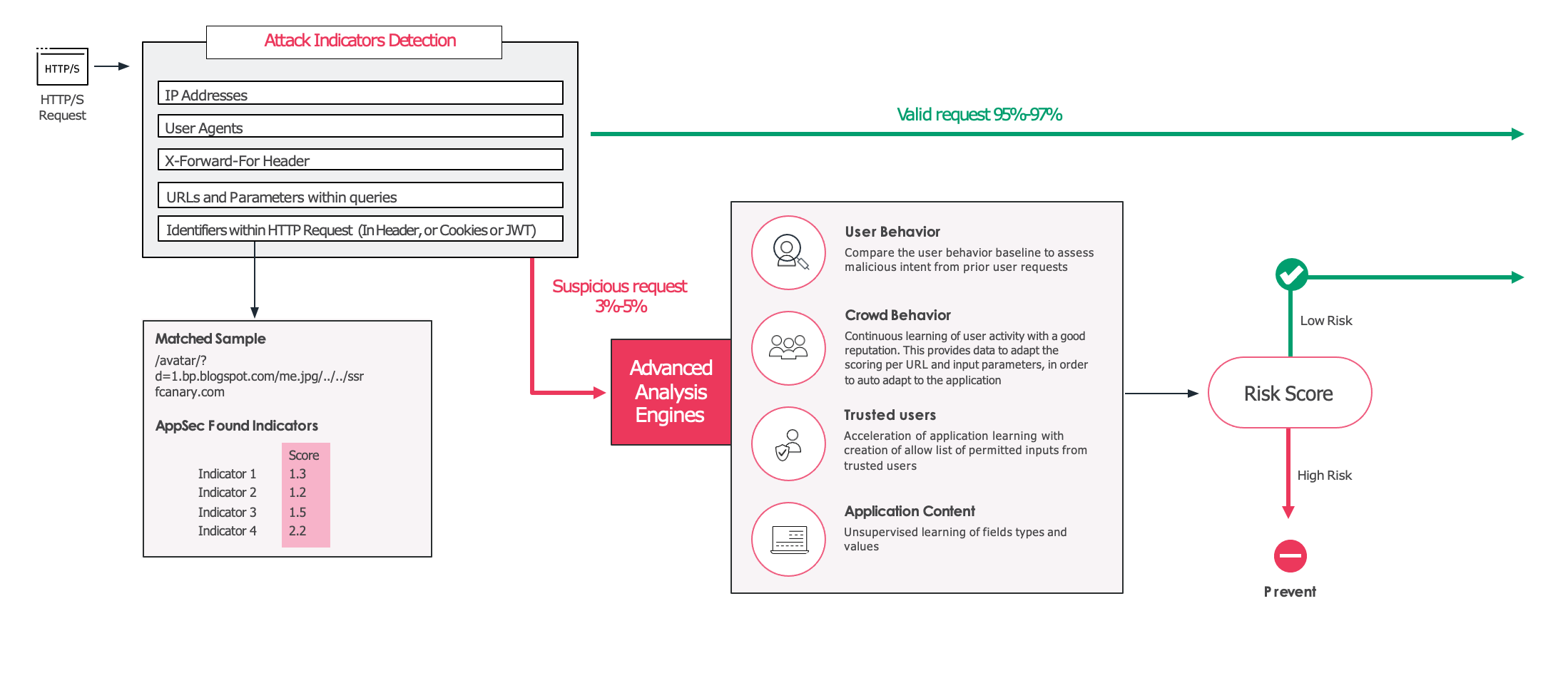
@@ -18,27 +18,41 @@ Every request to the application goes through two phases:
|
||||
|
||||
2. If the request is identified as a valid and legitimate request the request is allowed, and forwarded to your application. If, however, the request is considered suspicious or high risk, it then gets evaluated by the unsupervised model, which was trained in your specific environment. This model uses information such as the URL and the users involved to create a final confidence score that determines whether the request should be allowed or blocked.
|
||||
|
||||
The project is currently in Beta and feedback is most welcomed!
|
||||
|
||||
|
||||
## Machine Learning models
|
||||
|
||||
open-appsec uses two models:
|
||||
open-appsec uses two machine learning models:
|
||||
|
||||
1. A supervised model that was trained offline based on millions of requests, both malicious and benign.
|
||||
|
||||
* A basic model is provided as part of this repository. It is recommended for use in Monitor-Only and Test environments.
|
||||
* An advanced model which is more accurate and recommended for Production use can be downloaded from the [open-appsec portal](https://my.openappsec.io)->User Menu->Download advanced ML model. This model updates from time to time and you will get an email when these updates happen.
|
||||
* A **basic model** is provided as part of this repository. It is recommended for use in Monitor-Only and Test environments.
|
||||
* An **advanced model** which is more accurate and **recommended for Production** use can be downloaded from the [open-appsec portal](https://my.openappsec.io)->User Menu->Download advanced ML model. This model updates from time to time and you will get an email when these updates happen.
|
||||
|
||||
2. An unsupervised model that is being built in real time in the protected environment. This model uses traffic patterns specific to the environment.
|
||||
|
||||
|
||||
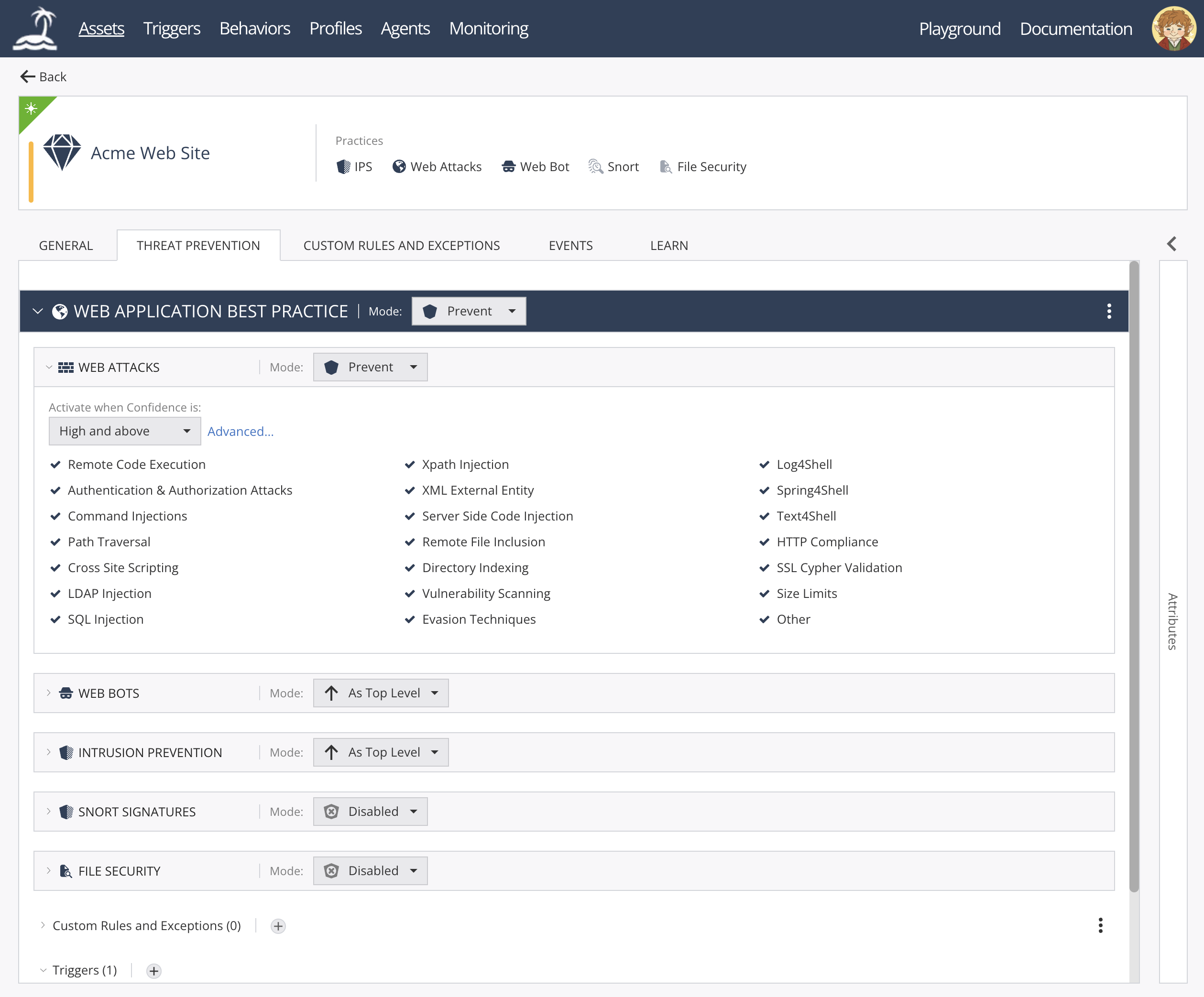
# Management
|
||||
|
||||
open-appsec can be managed using multiple methods:
|
||||
* [Declarative configuration files](https://docs.openappsec.io/getting-started/getting-started)
|
||||
* [Kubernetes Helm Charts and annotations](https://docs.openappsec.io/getting-started/getting-started)
|
||||
* [Using SaaS Web Management](https://docs.openappsec.io/getting-started/using-the-web-ui-saas)
|
||||
|
||||
open-appsec Web UI:
|
||||
|
||||
|
||||
|
||||
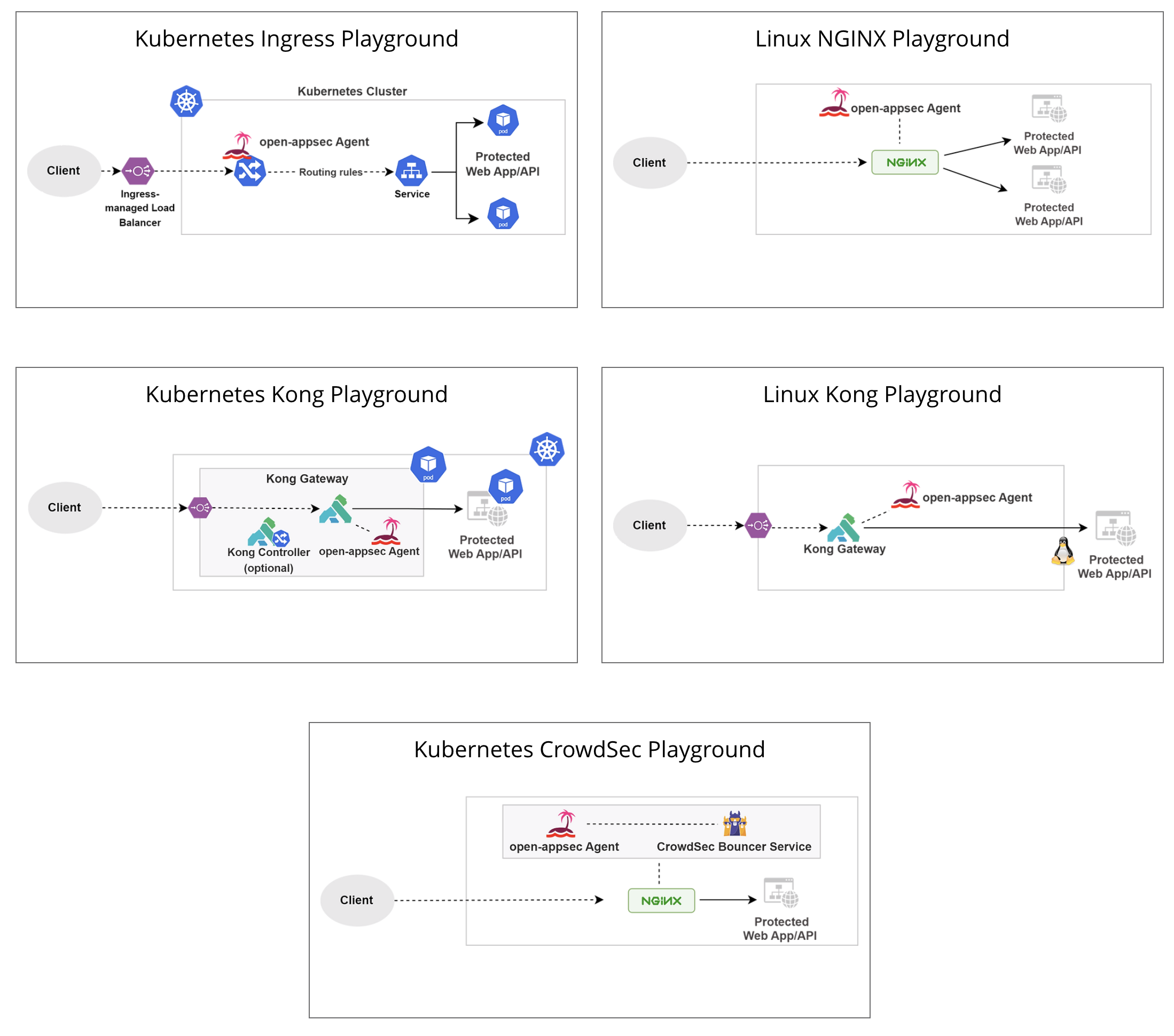
## Deployment Playgrounds (Virtual labs)
|
||||
You can experiment with open-appsec using [Playgrounds](https://www.openappsec.io/playground)
|
||||
|
||||
|
||||
|
||||
# Resources
|
||||
* [Project Website](https://openappsec.io)
|
||||
* [Offical Documentation](https://docs.openappsec.io/)
|
||||
* [Video Tutorials](https://www.openappsec.io/tutorials)
|
||||
* [Live Playgrounds](https://www.openappsec.io/playground)
|
||||
|
||||
|
||||
# open-appsec Installation
|
||||
# Installation
|
||||
|
||||
For Kubernetes (NGINX Ingress) using the installer:
|
||||
|
||||
@@ -49,11 +63,11 @@ $ ./open-appsec-k8s-install
|
||||
|
||||
For Kubernetes (NGINX or Kong) using Helm: follow [documentation](https://docs.openappsec.io/getting-started/start-with-kubernetes/install-using-helm-ingress-nginx-and-kong) – use this method if you’ve built your own containers.
|
||||
|
||||
For Linux (NGINX or Kong) using the installer (list of supported/pre-compiled NGINX attachments is available [here](https://downloads.openappsec.io/supported-nginx.txt)):
|
||||
For Linux (NGINX or Kong) using the installer (list of supported/pre-compiled NGINX attachments is available [here](https://downloads.openappsec.io/packages/supported-nginx.txt)):
|
||||
|
||||
```bash
|
||||
$ wget https://downloads.openappsec.io/open-appsec-install && chmod +x open-appsec-install
|
||||
$ ./open-appsec-install –auto
|
||||
$ ./open-appsec-install --auto
|
||||
```
|
||||
|
||||
For Linux, if you’ve built your own package use the following commands:
|
||||
@@ -90,12 +104,14 @@ Before compiling the services, you'll need to ensure the latest development vers
|
||||
* GTest
|
||||
* GMock
|
||||
* cURL
|
||||
* Redis
|
||||
* Hiredis
|
||||
|
||||
An example of installing the packages on Alpine:
|
||||
|
||||
```bash
|
||||
$ apk update
|
||||
$ apk add boost-dev openssl-dev pcre2-dev libxml2-dev gtest-dev curl-dev
|
||||
$ apk add boost-dev openssl-dev pcre2-dev libxml2-dev gtest-dev curl-dev hiredis-dev redis
|
||||
```
|
||||
|
||||
## Compiling and packaging the agent code
|
||||
@@ -130,17 +146,17 @@ To run a Nano-Agent as a container the following steps are required:
|
||||
2. If you are planning to manage the agent using the open-appsec UI, then make sure to obtain an agent token from the Management Portal and Enforce.
|
||||
3. Run the agent with the following command (where -e https_proxy parameter is optional):
|
||||
|
||||
`docker run -d --name=agent-container --ipc=host -v=<path to persistent location for agent config>:/etc/cp/conf -v=<path to persistent location for agent data files>:/etc/cp/data -v=<path to persistent location for agent debugs and logs>:/var/log/nano_agent -e https_proxy=<user:password@Proxy address:port> -it <agent-image> /cp-nano-agent [--token <token> | --hybrid-mode]`
|
||||
`docker run -d --name=agent-container --ipc=host -v=<path to persistent location for agent config>:/etc/cp/conf -v=<path to persistent location for agent data files>:/etc/cp/data -v=<path to persistent location for agent debugs and logs>:/var/log/nano_agent -e https_proxy=<user:password@Proxy address:port> -it <agent-image> /cp-nano-agent [--token <token> | --standalone]`
|
||||
|
||||
Example:
|
||||
```bash
|
||||
$ docker run -d --name=agent-container --ipc=host -v=/home/admin/agent/conf:/etc/cp/conf -v=/home/admin/agent/data:/etc/cp/data -v=/home/admin/agent/logs:/var/log/nano_agent –e https_proxy=user:password@1.2.3.4:8080 -it agent-docker /cp-nano-agent --hybrid-mode
|
||||
$ docker run -d --name=agent-container --ipc=host -v=/home/admin/agent/conf:/etc/cp/conf -v=/home/admin/agent/data:/etc/cp/data -v=/home/admin/agent/logs:/var/log/nano_agent –e https_proxy=user:password@1.2.3.4:8080 -it agent-docker /cp-nano-agent --standalone
|
||||
$ docker ps
|
||||
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
|
||||
1e67f2abbfd4 agent-docker "/cp-nano-agent --hybrid-mode" 1 minute ago Up 1 minute agent-container
|
||||
```
|
||||
|
||||
Note that you are not required to use a token from the Management Portal if you are managing your security policy locally. However, you are required to use the --hybrid-mode flag in such cases. In addition, the volumes in the command are mandatory only if you wish to have persistency upon restart/upgrade/crash of the agent and its re-execution.
|
||||
Note that you are not required to use a token from the Management Portal if you are managing your security policy locally. However, you are required to use the --standalone flag in such cases. In addition, the volumes in the command are mandatory only if you wish to have persistency upon restart/upgrade/crash of the agent and its re-execution.
|
||||
Lastly, --ipc=host argument is mandatory in order for the agent to have access to shared memory with a protected attachment (NGINX server).
|
||||
|
||||
4. Create or replace the NGINX container using the [Attachment Repository](https://github.com/openappsec/attachment).
|
||||
|
||||
@@ -31,5 +31,7 @@ DEFINE_KDEBUG_FLAG(statefulValidation)
|
||||
DEFINE_KDEBUG_FLAG(statelessValidation)
|
||||
DEFINE_KDEBUG_FLAG(kernelMetric)
|
||||
DEFINE_KDEBUG_FLAG(tproxy)
|
||||
DEFINE_KDEBUG_FLAG(tenantStats)
|
||||
DEFINE_KDEBUG_FLAG(uuidTranslation)
|
||||
|
||||
#endif // DEFINE_KDEBUG_FLAG
|
||||
|
||||
@@ -2,39 +2,124 @@
|
||||
|
||||
This file documents all notable changes to [ingress-nginx](https://github.com/kubernetes/ingress-nginx) Helm Chart. The release numbering uses [semantic versioning](http://semver.org).
|
||||
|
||||
### 4.4.0
|
||||
|
||||
* Adding support for disabling liveness and readiness probes to the Helm chart by @njegosrailic in https://github.com/kubernetes/ingress-nginx/pull/9238
|
||||
* add:(admission-webhooks) ability to set securityContext by @ybelMekk in https://github.com/kubernetes/ingress-nginx/pull/9186
|
||||
* #7652 - Updated Helm chart to use the fullname for the electionID if not specified. by @FutureMatt in https://github.com/kubernetes/ingress-nginx/pull/9133
|
||||
* Rename controller-wehbooks-networkpolicy.yaml. by @Gacko in https://github.com/kubernetes/ingress-nginx/pull/9123
|
||||
|
||||
### 4.3.0
|
||||
- Support for Kubernetes v.1.25.0 was added and support for endpoint slices
|
||||
- Support for Kubernetes v1.20.0 and v1.21.0 was removed
|
||||
- [8890](https://github.com/kubernetes/ingress-nginx/pull/8890) migrate to endpointslices
|
||||
- [9059](https://github.com/kubernetes/ingress-nginx/pull/9059) kubewebhookcertgen sha change after go1191
|
||||
- [9046](https://github.com/kubernetes/ingress-nginx/pull/9046) Parameterize metrics port name
|
||||
- [9104](https://github.com/kubernetes/ingress-nginx/pull/9104) Fix yaml formatting error with multiple annotations
|
||||
|
||||
### 4.2.1
|
||||
|
||||
- The sha of kube-webhook-certgen image & the opentelemetry image, in values file, was changed to new images built on alpine-v3.16.1
|
||||
- "[8896](https://github.com/kubernetes/ingress-nginx/pull/8896) updated to new images built today"
|
||||
|
||||
### 4.2.0
|
||||
|
||||
- Support for Kubernetes v1.19.0 was removed
|
||||
- "[8810](https://github.com/kubernetes/ingress-nginx/pull/8810) Prepare for v1.3.0"
|
||||
- "[8808](https://github.com/kubernetes/ingress-nginx/pull/8808) revert arch var name"
|
||||
- "[8805](https://github.com/kubernetes/ingress-nginx/pull/8805) Bump k8s.io/klog/v2 from 2.60.1 to 2.70.1"
|
||||
- "[8803](https://github.com/kubernetes/ingress-nginx/pull/8803) Update to nginx base with alpine v3.16"
|
||||
- "[8802](https://github.com/kubernetes/ingress-nginx/pull/8802) chore: start v1.3.0 release process"
|
||||
- "[8798](https://github.com/kubernetes/ingress-nginx/pull/8798) Add v1.24.0 to test matrix"
|
||||
- "[8796](https://github.com/kubernetes/ingress-nginx/pull/8796) fix: add MAC_OS variable for static-check"
|
||||
- "[8793](https://github.com/kubernetes/ingress-nginx/pull/8793) changed to alpine-v3.16"
|
||||
- "[8781](https://github.com/kubernetes/ingress-nginx/pull/8781) Bump github.com/stretchr/testify from 1.7.5 to 1.8.0"
|
||||
- "[8778](https://github.com/kubernetes/ingress-nginx/pull/8778) chore: remove stable.txt from release process"
|
||||
- "[8775](https://github.com/kubernetes/ingress-nginx/pull/8775) Remove stable"
|
||||
- "[8773](https://github.com/kubernetes/ingress-nginx/pull/8773) Bump github/codeql-action from 2.1.14 to 2.1.15"
|
||||
- "[8772](https://github.com/kubernetes/ingress-nginx/pull/8772) Bump ossf/scorecard-action from 1.1.1 to 1.1.2"
|
||||
- "[8771](https://github.com/kubernetes/ingress-nginx/pull/8771) fix bullet md format"
|
||||
- "[8770](https://github.com/kubernetes/ingress-nginx/pull/8770) Add condition for monitoring.coreos.com/v1 API"
|
||||
- "[8769](https://github.com/kubernetes/ingress-nginx/pull/8769) Fix typos and add links to developer guide"
|
||||
- "[8767](https://github.com/kubernetes/ingress-nginx/pull/8767) change v1.2.0 to v1.2.1 in deploy doc URLs"
|
||||
- "[8765](https://github.com/kubernetes/ingress-nginx/pull/8765) Bump github/codeql-action from 1.0.26 to 2.1.14"
|
||||
- "[8752](https://github.com/kubernetes/ingress-nginx/pull/8752) Bump github.com/spf13/cobra from 1.4.0 to 1.5.0"
|
||||
- "[8751](https://github.com/kubernetes/ingress-nginx/pull/8751) Bump github.com/stretchr/testify from 1.7.2 to 1.7.5"
|
||||
- "[8750](https://github.com/kubernetes/ingress-nginx/pull/8750) added announcement"
|
||||
- "[8740](https://github.com/kubernetes/ingress-nginx/pull/8740) change sha e2etestrunner and echoserver"
|
||||
- "[8738](https://github.com/kubernetes/ingress-nginx/pull/8738) Update docs to make it easier for noobs to follow step by step"
|
||||
- "[8737](https://github.com/kubernetes/ingress-nginx/pull/8737) updated baseimage sha"
|
||||
- "[8736](https://github.com/kubernetes/ingress-nginx/pull/8736) set ld-musl-path"
|
||||
- "[8733](https://github.com/kubernetes/ingress-nginx/pull/8733) feat: migrate leaderelection lock to leases"
|
||||
- "[8726](https://github.com/kubernetes/ingress-nginx/pull/8726) prometheus metric: upstream_latency_seconds"
|
||||
- "[8720](https://github.com/kubernetes/ingress-nginx/pull/8720) Ci pin deps"
|
||||
- "[8719](https://github.com/kubernetes/ingress-nginx/pull/8719) Working OpenTelemetry sidecar (base nginx image)"
|
||||
- "[8714](https://github.com/kubernetes/ingress-nginx/pull/8714) Create Openssf scorecard"
|
||||
- "[8708](https://github.com/kubernetes/ingress-nginx/pull/8708) Bump github.com/prometheus/common from 0.34.0 to 0.35.0"
|
||||
- "[8703](https://github.com/kubernetes/ingress-nginx/pull/8703) Bump actions/dependency-review-action from 1 to 2"
|
||||
- "[8701](https://github.com/kubernetes/ingress-nginx/pull/8701) Fix several typos"
|
||||
- "[8699](https://github.com/kubernetes/ingress-nginx/pull/8699) fix the gosec test and a make target for it"
|
||||
- "[8698](https://github.com/kubernetes/ingress-nginx/pull/8698) Bump actions/upload-artifact from 2.3.1 to 3.1.0"
|
||||
- "[8697](https://github.com/kubernetes/ingress-nginx/pull/8697) Bump actions/setup-go from 2.2.0 to 3.2.0"
|
||||
- "[8695](https://github.com/kubernetes/ingress-nginx/pull/8695) Bump actions/download-artifact from 2 to 3"
|
||||
- "[8694](https://github.com/kubernetes/ingress-nginx/pull/8694) Bump crazy-max/ghaction-docker-buildx from 1.6.2 to 3.3.1"
|
||||
|
||||
### 4.1.2
|
||||
|
||||
- "[8587](https://github.com/kubernetes/ingress-nginx/pull/8587) Add CAP_SYS_CHROOT to DS/PSP when needed"
|
||||
- "[8458](https://github.com/kubernetes/ingress-nginx/pull/8458) Add portNamePreffix Helm chart parameter"
|
||||
- "[8522](https://github.com/kubernetes/ingress-nginx/pull/8522) Add documentation for controller.service.loadBalancerIP in Helm chart"
|
||||
|
||||
### 4.1.0
|
||||
|
||||
- "[8481](https://github.com/kubernetes/ingress-nginx/pull/8481) Fix log creation in chroot script"
|
||||
- "[8479](https://github.com/kubernetes/ingress-nginx/pull/8479) changed nginx base img tag to img built with alpine3.14.6"
|
||||
- "[8478](https://github.com/kubernetes/ingress-nginx/pull/8478) update base images and protobuf gomod"
|
||||
- "[8468](https://github.com/kubernetes/ingress-nginx/pull/8468) Fallback to ngx.var.scheme for redirectScheme with use-forward-headers when X-Forwarded-Proto is empty"
|
||||
- "[8456](https://github.com/kubernetes/ingress-nginx/pull/8456) Implement object deep inspector"
|
||||
- "[8455](https://github.com/kubernetes/ingress-nginx/pull/8455) Update dependencies"
|
||||
- "[8454](https://github.com/kubernetes/ingress-nginx/pull/8454) Update index.md"
|
||||
- "[8447](https://github.com/kubernetes/ingress-nginx/pull/8447) typo fixing"
|
||||
- "[8446](https://github.com/kubernetes/ingress-nginx/pull/8446) Fix suggested annotation-value-word-blocklist"
|
||||
- "[8444](https://github.com/kubernetes/ingress-nginx/pull/8444) replace deprecated topology key in example with current one"
|
||||
- "[8443](https://github.com/kubernetes/ingress-nginx/pull/8443) Add dependency review enforcement"
|
||||
- "[8434](https://github.com/kubernetes/ingress-nginx/pull/8434) added new auth-tls-match-cn annotation"
|
||||
- "[8426](https://github.com/kubernetes/ingress-nginx/pull/8426) Bump github.com/prometheus/common from 0.32.1 to 0.33.0"
|
||||
|
||||
### 4.0.18
|
||||
"[8291](https://github.com/kubernetes/ingress-nginx/pull/8291) remove git tag env from cloud build"
|
||||
"[8286](https://github.com/kubernetes/ingress-nginx/pull/8286) Fix OpenTelemetry sidecar image build"
|
||||
"[8277](https://github.com/kubernetes/ingress-nginx/pull/8277) Add OpenSSF Best practices badge"
|
||||
"[8273](https://github.com/kubernetes/ingress-nginx/pull/8273) Issue#8241"
|
||||
"[8267](https://github.com/kubernetes/ingress-nginx/pull/8267) Add fsGroup value to admission-webhooks/job-patch charts"
|
||||
"[8262](https://github.com/kubernetes/ingress-nginx/pull/8262) Updated confusing error"
|
||||
"[8256](https://github.com/kubernetes/ingress-nginx/pull/8256) fix: deny locations with invalid auth-url annotation"
|
||||
"[8253](https://github.com/kubernetes/ingress-nginx/pull/8253) Add a certificate info metric"
|
||||
"[8236](https://github.com/kubernetes/ingress-nginx/pull/8236) webhook: remove useless code."
|
||||
"[8227](https://github.com/kubernetes/ingress-nginx/pull/8227) Update libraries in webhook image"
|
||||
"[8225](https://github.com/kubernetes/ingress-nginx/pull/8225) fix inconsistent-label-cardinality for prometheus metrics: nginx_ingress_controller_requests"
|
||||
"[8221](https://github.com/kubernetes/ingress-nginx/pull/8221) Do not validate ingresses with unknown ingress class in admission webhook endpoint"
|
||||
"[8210](https://github.com/kubernetes/ingress-nginx/pull/8210) Bump github.com/prometheus/client_golang from 1.11.0 to 1.12.1"
|
||||
"[8209](https://github.com/kubernetes/ingress-nginx/pull/8209) Bump google.golang.org/grpc from 1.43.0 to 1.44.0"
|
||||
"[8204](https://github.com/kubernetes/ingress-nginx/pull/8204) Add Artifact Hub lint"
|
||||
"[8203](https://github.com/kubernetes/ingress-nginx/pull/8203) Fix Indentation of example and link to cert-manager tutorial"
|
||||
"[8201](https://github.com/kubernetes/ingress-nginx/pull/8201) feat(metrics): add path and method labels to requests countera"
|
||||
"[8199](https://github.com/kubernetes/ingress-nginx/pull/8199) use functional options to reduce number of methods creating an EchoDeployment"
|
||||
"[8196](https://github.com/kubernetes/ingress-nginx/pull/8196) docs: fix inconsistent controller annotation"
|
||||
"[8191](https://github.com/kubernetes/ingress-nginx/pull/8191) Using Go install for misspell"
|
||||
"[8186](https://github.com/kubernetes/ingress-nginx/pull/8186) prometheus+grafana using servicemonitor"
|
||||
"[8185](https://github.com/kubernetes/ingress-nginx/pull/8185) Append elements on match, instead of removing for cors-annotations"
|
||||
"[8179](https://github.com/kubernetes/ingress-nginx/pull/8179) Bump github.com/opencontainers/runc from 1.0.3 to 1.1.0"
|
||||
"[8173](https://github.com/kubernetes/ingress-nginx/pull/8173) Adding annotations to the controller service account"
|
||||
"[8163](https://github.com/kubernetes/ingress-nginx/pull/8163) Update the $req_id placeholder description"
|
||||
"[8162](https://github.com/kubernetes/ingress-nginx/pull/8162) Versioned static manifests"
|
||||
"[8159](https://github.com/kubernetes/ingress-nginx/pull/8159) Adding some geoip variables and default values"
|
||||
"[8155](https://github.com/kubernetes/ingress-nginx/pull/8155) #7271 feat: avoid-pdb-creation-when-default-backend-disabled-and-replicas-gt-1"
|
||||
"[8151](https://github.com/kubernetes/ingress-nginx/pull/8151) Automatically generate helm docs"
|
||||
"[8143](https://github.com/kubernetes/ingress-nginx/pull/8143) Allow to configure delay before controller exits"
|
||||
"[8136](https://github.com/kubernetes/ingress-nginx/pull/8136) add ingressClass option to helm chart - back compatibility with ingress.class annotations"
|
||||
"[8126](https://github.com/kubernetes/ingress-nginx/pull/8126) Example for JWT"
|
||||
|
||||
- "[8291](https://github.com/kubernetes/ingress-nginx/pull/8291) remove git tag env from cloud build"
|
||||
- "[8286](https://github.com/kubernetes/ingress-nginx/pull/8286) Fix OpenTelemetry sidecar image build"
|
||||
- "[8277](https://github.com/kubernetes/ingress-nginx/pull/8277) Add OpenSSF Best practices badge"
|
||||
- "[8273](https://github.com/kubernetes/ingress-nginx/pull/8273) Issue#8241"
|
||||
- "[8267](https://github.com/kubernetes/ingress-nginx/pull/8267) Add fsGroup value to admission-webhooks/job-patch charts"
|
||||
- "[8262](https://github.com/kubernetes/ingress-nginx/pull/8262) Updated confusing error"
|
||||
- "[8256](https://github.com/kubernetes/ingress-nginx/pull/8256) fix: deny locations with invalid auth-url annotation"
|
||||
- "[8253](https://github.com/kubernetes/ingress-nginx/pull/8253) Add a certificate info metric"
|
||||
- "[8236](https://github.com/kubernetes/ingress-nginx/pull/8236) webhook: remove useless code."
|
||||
- "[8227](https://github.com/kubernetes/ingress-nginx/pull/8227) Update libraries in webhook image"
|
||||
- "[8225](https://github.com/kubernetes/ingress-nginx/pull/8225) fix inconsistent-label-cardinality for prometheus metrics: nginx_ingress_controller_requests"
|
||||
- "[8221](https://github.com/kubernetes/ingress-nginx/pull/8221) Do not validate ingresses with unknown ingress class in admission webhook endpoint"
|
||||
- "[8210](https://github.com/kubernetes/ingress-nginx/pull/8210) Bump github.com/prometheus/client_golang from 1.11.0 to 1.12.1"
|
||||
- "[8209](https://github.com/kubernetes/ingress-nginx/pull/8209) Bump google.golang.org/grpc from 1.43.0 to 1.44.0"
|
||||
- "[8204](https://github.com/kubernetes/ingress-nginx/pull/8204) Add Artifact Hub lint"
|
||||
- "[8203](https://github.com/kubernetes/ingress-nginx/pull/8203) Fix Indentation of example and link to cert-manager tutorial"
|
||||
- "[8201](https://github.com/kubernetes/ingress-nginx/pull/8201) feat(metrics): add path and method labels to requests countera"
|
||||
- "[8199](https://github.com/kubernetes/ingress-nginx/pull/8199) use functional options to reduce number of methods creating an EchoDeployment"
|
||||
- "[8196](https://github.com/kubernetes/ingress-nginx/pull/8196) docs: fix inconsistent controller annotation"
|
||||
- "[8191](https://github.com/kubernetes/ingress-nginx/pull/8191) Using Go install for misspell"
|
||||
- "[8186](https://github.com/kubernetes/ingress-nginx/pull/8186) prometheus+grafana using servicemonitor"
|
||||
- "[8185](https://github.com/kubernetes/ingress-nginx/pull/8185) Append elements on match, instead of removing for cors-annotations"
|
||||
- "[8179](https://github.com/kubernetes/ingress-nginx/pull/8179) Bump github.com/opencontainers/runc from 1.0.3 to 1.1.0"
|
||||
- "[8173](https://github.com/kubernetes/ingress-nginx/pull/8173) Adding annotations to the controller service account"
|
||||
- "[8163](https://github.com/kubernetes/ingress-nginx/pull/8163) Update the $req_id placeholder description"
|
||||
- "[8162](https://github.com/kubernetes/ingress-nginx/pull/8162) Versioned static manifests"
|
||||
- "[8159](https://github.com/kubernetes/ingress-nginx/pull/8159) Adding some geoip variables and default values"
|
||||
- "[8155](https://github.com/kubernetes/ingress-nginx/pull/8155) #7271 feat: avoid-pdb-creation-when-default-backend-disabled-and-replicas-gt-1"
|
||||
- "[8151](https://github.com/kubernetes/ingress-nginx/pull/8151) Automatically generate helm docs"
|
||||
- "[8143](https://github.com/kubernetes/ingress-nginx/pull/8143) Allow to configure delay before controller exits"
|
||||
- "[8136](https://github.com/kubernetes/ingress-nginx/pull/8136) add ingressClass option to helm chart - back compatibility with ingress.class annotations"
|
||||
- "[8126](https://github.com/kubernetes/ingress-nginx/pull/8126) Example for JWT"
|
||||
|
||||
|
||||
### 4.0.15
|
||||
@@ -44,7 +129,7 @@ This file documents all notable changes to [ingress-nginx](https://github.com/ku
|
||||
- [8118] https://github.com/kubernetes/ingress-nginx/pull/8118 Remove deprecated libraries, update other libs
|
||||
- [8117] https://github.com/kubernetes/ingress-nginx/pull/8117 Fix codegen errors
|
||||
- [8115] https://github.com/kubernetes/ingress-nginx/pull/8115 chart/ghaction: set the correct permission to have access to push a release
|
||||
- [8098] https://github.com/kubernetes/ingress-nginx/pull/8098 generating SHA for CA only certs in backend_ssl.go + comparision of P…
|
||||
- [8098] https://github.com/kubernetes/ingress-nginx/pull/8098 generating SHA for CA only certs in backend_ssl.go + comparison of P…
|
||||
- [8088] https://github.com/kubernetes/ingress-nginx/pull/8088 Fix Edit this page link to use main branch
|
||||
- [8072] https://github.com/kubernetes/ingress-nginx/pull/8072 Expose GeoIP2 Continent code as variable
|
||||
- [8061] https://github.com/kubernetes/ingress-nginx/pull/8061 docs(charts): using helm-docs for chart
|
||||
@@ -54,7 +139,7 @@ This file documents all notable changes to [ingress-nginx](https://github.com/ku
|
||||
- [8046] https://github.com/kubernetes/ingress-nginx/pull/8046 Report expired certificates (#8045)
|
||||
- [8044] https://github.com/kubernetes/ingress-nginx/pull/8044 remove G109 check till gosec resolves issues
|
||||
- [8042] https://github.com/kubernetes/ingress-nginx/pull/8042 docs_multiple_instances_one_cluster_ticket_7543
|
||||
- [8041] https://github.com/kubernetes/ingress-nginx/pull/8041 docs: fix typo'd executible name
|
||||
- [8041] https://github.com/kubernetes/ingress-nginx/pull/8041 docs: fix typo'd executable name
|
||||
- [8035] https://github.com/kubernetes/ingress-nginx/pull/8035 Comment busy owners
|
||||
- [8029] https://github.com/kubernetes/ingress-nginx/pull/8029 Add stream-snippet as a ConfigMap and Annotation option
|
||||
- [8023] https://github.com/kubernetes/ingress-nginx/pull/8023 fix nginx compilation flags
|
||||
@@ -71,7 +156,7 @@ This file documents all notable changes to [ingress-nginx](https://github.com/ku
|
||||
- [7996] https://github.com/kubernetes/ingress-nginx/pull/7996 doc: improvement
|
||||
- [7983] https://github.com/kubernetes/ingress-nginx/pull/7983 Fix a couple of misspellings in the annotations documentation.
|
||||
- [7979] https://github.com/kubernetes/ingress-nginx/pull/7979 allow set annotations for admission Jobs
|
||||
- [7977] https://github.com/kubernetes/ingress-nginx/pull/7977 Add ssl_reject_handshake to defaul server
|
||||
- [7977] https://github.com/kubernetes/ingress-nginx/pull/7977 Add ssl_reject_handshake to default server
|
||||
- [7975] https://github.com/kubernetes/ingress-nginx/pull/7975 add legacy version update v0.50.0 to main changelog
|
||||
- [7972] https://github.com/kubernetes/ingress-nginx/pull/7972 updated service upstream definition
|
||||
|
||||
@@ -119,11 +204,11 @@ This file documents all notable changes to [ingress-nginx](https://github.com/ku
|
||||
|
||||
- [7707] https://github.com/kubernetes/ingress-nginx/pull/7707 Release v1.0.2 of ingress-nginx
|
||||
|
||||
### 4.0.2
|
||||
### 4.0.2
|
||||
|
||||
- [7681] https://github.com/kubernetes/ingress-nginx/pull/7681 Release v1.0.1 of ingress-nginx
|
||||
|
||||
### 4.0.1
|
||||
### 4.0.1
|
||||
|
||||
- [7535] https://github.com/kubernetes/ingress-nginx/pull/7535 Release v1.0.0 ingress-nginx
|
||||
|
||||
|
||||
@@ -1,22 +1,13 @@
|
||||
annotations:
|
||||
artifacthub.io/changes: |
|
||||
- "[8459](https://github.com/kubernetes/ingress-nginx/pull/8459) Update default allowed CORS headers"
|
||||
- "[8202](https://github.com/kubernetes/ingress-nginx/pull/8202) disable modsecurity on error page"
|
||||
- "[8178](https://github.com/kubernetes/ingress-nginx/pull/8178) Add header Host into mirror annotations"
|
||||
- "[8213](https://github.com/kubernetes/ingress-nginx/pull/8213) feat: always set auth cookie"
|
||||
- "[8548](https://github.com/kubernetes/ingress-nginx/pull/8548) Implement reporting status classes in metrics"
|
||||
- "[8612](https://github.com/kubernetes/ingress-nginx/pull/8612) move so files under /etc/nginx/modules"
|
||||
- "[8624](https://github.com/kubernetes/ingress-nginx/pull/8624) Add patch to remove root and alias directives"
|
||||
- "[8623](https://github.com/kubernetes/ingress-nginx/pull/8623) Improve path rule"
|
||||
artifacthub.io/changes: '- "Update Ingress-Nginx version controller-v1.9.4"'
|
||||
artifacthub.io/prerelease: "false"
|
||||
apiVersion: v2
|
||||
appVersion: 1.2.1
|
||||
appVersion: latest
|
||||
keywords:
|
||||
- ingress
|
||||
- nginx
|
||||
kubeVersion: '>=1.19.0-0'
|
||||
kubeVersion: '>=1.20.0-0'
|
||||
name: open-appsec-k8s-nginx-ingress
|
||||
sources:
|
||||
- https://github.com/kubernetes/ingress-nginx
|
||||
type: application
|
||||
version: 4.1.4
|
||||
version: 4.8.3
|
||||
|
||||
@@ -2,16 +2,15 @@
|
||||
|
||||
[ingress-nginx](https://github.com/kubernetes/ingress-nginx) Ingress controller for Kubernetes using NGINX as a reverse proxy and load balancer
|
||||
|
||||
  
|
||||
 
|
||||
|
||||
To use, add `ingressClassName: nginx` spec field or the `kubernetes.io/ingress.class: nginx` annotation to your Ingress resources.
|
||||
|
||||
This chart bootstraps an ingress-nginx deployment on a [Kubernetes](http://kubernetes.io) cluster using the [Helm](https://helm.sh) package manager.
|
||||
|
||||
## Prerequisites
|
||||
## Requirements
|
||||
|
||||
- Chart version 3.x.x: Kubernetes v1.16+
|
||||
- Chart version 4.x.x and above: Kubernetes v1.19+
|
||||
Kubernetes: `>=1.20.0-0`
|
||||
|
||||
## Get Repo Info
|
||||
|
||||
@@ -52,10 +51,6 @@ helm upgrade [RELEASE_NAME] [CHART] --install
|
||||
|
||||
_See [helm upgrade](https://helm.sh/docs/helm/helm_upgrade/) for command documentation._
|
||||
|
||||
### Upgrading With Zero Downtime in Production
|
||||
|
||||
By default the ingress-nginx controller has service interruptions whenever it's pods are restarted or redeployed. In order to fix that, see the excellent blog post by Lindsay Landry from Codecademy: [Kubernetes: Nginx and Zero Downtime in Production](https://medium.com/codecademy-engineering/kubernetes-nginx-and-zero-downtime-in-production-2c910c6a5ed8).
|
||||
|
||||
### Migrating from stable/nginx-ingress
|
||||
|
||||
There are two main ways to migrate a release from `stable/nginx-ingress` to `ingress-nginx/ingress-nginx` chart:
|
||||
@@ -66,7 +61,6 @@ There are two main ways to migrate a release from `stable/nginx-ingress` to `ing
|
||||
1. Redirect your DNS traffic from the old controller to the new controller
|
||||
1. Log traffic from both controllers during this changeover
|
||||
1. [Uninstall](#uninstall-chart) the old controller once traffic has fully drained from it
|
||||
1. For details on all of these steps see [Upgrading With Zero Downtime in Production](#upgrading-with-zero-downtime-in-production)
|
||||
|
||||
Note that there are some different and upgraded configurations between the two charts, described by Rimas Mocevicius from JFrog in the "Upgrading to ingress-nginx Helm chart" section of [Migrating from Helm chart nginx-ingress to ingress-nginx](https://rimusz.net/migrating-to-ingress-nginx). As the `ingress-nginx/ingress-nginx` chart continues to update, you will want to check current differences by running [helm configuration](#configuration) commands on both charts.
|
||||
|
||||
@@ -85,14 +79,14 @@ else it would make it impossible to evacuate a node. See [gh issue #7127](https:
|
||||
|
||||
### Prometheus Metrics
|
||||
|
||||
The Nginx ingress controller can export Prometheus metrics, by setting `controller.metrics.enabled` to `true`.
|
||||
The Ingress-Nginx Controller can export Prometheus metrics, by setting `controller.metrics.enabled` to `true`.
|
||||
|
||||
You can add Prometheus annotations to the metrics service using `controller.metrics.service.annotations`.
|
||||
Alternatively, if you use the Prometheus Operator, you can enable ServiceMonitor creation using `controller.metrics.serviceMonitor.enabled`. And set `controller.metrics.serviceMonitor.additionalLabels.release="prometheus"`. "release=prometheus" should match the label configured in the prometheus servicemonitor ( see `kubectl get servicemonitor prometheus-kube-prom-prometheus -oyaml -n prometheus`)
|
||||
|
||||
### ingress-nginx nginx\_status page/stats server
|
||||
|
||||
Previous versions of this chart had a `controller.stats.*` configuration block, which is now obsolete due to the following changes in nginx ingress controller:
|
||||
Previous versions of this chart had a `controller.stats.*` configuration block, which is now obsolete due to the following changes in Ingress-Nginx Controller:
|
||||
|
||||
- In [0.16.1](https://github.com/kubernetes/ingress-nginx/blob/main/Changelog.md#0161), the vts (virtual host traffic status) dashboard was removed
|
||||
- In [0.23.0](https://github.com/kubernetes/ingress-nginx/blob/main/Changelog.md#0230), the status page at port 18080 is now a unix socket webserver only available at localhost.
|
||||
@@ -100,7 +94,7 @@ Previous versions of this chart had a `controller.stats.*` configuration block,
|
||||
|
||||
### ExternalDNS Service Configuration
|
||||
|
||||
Add an [ExternalDNS](https://github.com/kubernetes-incubator/external-dns) annotation to the LoadBalancer service:
|
||||
Add an [ExternalDNS](https://github.com/kubernetes-sigs/external-dns) annotation to the LoadBalancer service:
|
||||
|
||||
```yaml
|
||||
controller:
|
||||
@@ -111,7 +105,7 @@ controller:
|
||||
|
||||
### AWS L7 ELB with SSL Termination
|
||||
|
||||
Annotate the controller as shown in the [nginx-ingress l7 patch](https://github.com/kubernetes/ingress-nginx/blob/main/deploy/aws/l7/service-l7.yaml):
|
||||
Annotate the controller as shown in the [nginx-ingress l7 patch](https://github.com/kubernetes/ingress-nginx/blob/ab3a789caae65eec4ad6e3b46b19750b481b6bce/deploy/aws/l7/service-l7.yaml):
|
||||
|
||||
```yaml
|
||||
controller:
|
||||
@@ -126,19 +120,6 @@ controller:
|
||||
service.beta.kubernetes.io/aws-load-balancer-connection-idle-timeout: '3600'
|
||||
```
|
||||
|
||||
### AWS route53-mapper
|
||||
|
||||
To configure the LoadBalancer service with the [route53-mapper addon](https://github.com/kubernetes/kops/tree/master/addons/route53-mapper), add the `domainName` annotation and `dns` label:
|
||||
|
||||
```yaml
|
||||
controller:
|
||||
service:
|
||||
labels:
|
||||
dns: "route53"
|
||||
annotations:
|
||||
domainName: "kubernetes-example.com"
|
||||
```
|
||||
|
||||
### Additional Internal Load Balancer
|
||||
|
||||
This setup is useful when you need both external and internal load balancers but don't want to have multiple ingress controllers and multiple ingress objects per application.
|
||||
@@ -162,8 +143,10 @@ controller:
|
||||
internal:
|
||||
enabled: true
|
||||
annotations:
|
||||
# Create internal ELB
|
||||
service.beta.kubernetes.io/aws-load-balancer-internal: "true"
|
||||
# Create internal NLB
|
||||
service.beta.kubernetes.io/aws-load-balancer-scheme: "internal"
|
||||
# Create internal ELB(Deprecated)
|
||||
# service.beta.kubernetes.io/aws-load-balancer-internal: "true"
|
||||
# Any other annotation can be declared here.
|
||||
```
|
||||
|
||||
@@ -175,7 +158,7 @@ controller:
|
||||
internal:
|
||||
enabled: true
|
||||
annotations:
|
||||
# Create internal LB. More informations: https://cloud.google.com/kubernetes-engine/docs/how-to/internal-load-balancing
|
||||
# Create internal LB. More information: https://cloud.google.com/kubernetes-engine/docs/how-to/internal-load-balancing
|
||||
# For GKE versions 1.17 and later
|
||||
networking.gke.io/load-balancer-type: "Internal"
|
||||
# For earlier versions
|
||||
@@ -206,17 +189,34 @@ controller:
|
||||
# Any other annotation can be declared here.
|
||||
```
|
||||
|
||||
The load balancer annotations of more cloud service providers can be found: [Internal load balancer](https://kubernetes.io/docs/concepts/services-networking/service/#internal-load-balancer).
|
||||
|
||||
An use case for this scenario is having a split-view DNS setup where the public zone CNAME records point to the external balancer URL while the private zone CNAME records point to the internal balancer URL. This way, you only need one ingress kubernetes object.
|
||||
|
||||
Optionally you can set `controller.service.loadBalancerIP` if you need a static IP for the resulting `LoadBalancer`.
|
||||
|
||||
### Ingress Admission Webhooks
|
||||
|
||||
With nginx-ingress-controller version 0.25+, the nginx ingress controller pod exposes an endpoint that will integrate with the `validatingwebhookconfiguration` Kubernetes feature to prevent bad ingress from being added to the cluster.
|
||||
With nginx-ingress-controller version 0.25+, the Ingress-Nginx Controller pod exposes an endpoint that will integrate with the `validatingwebhookconfiguration` Kubernetes feature to prevent bad ingress from being added to the cluster.
|
||||
**This feature is enabled by default since 0.31.0.**
|
||||
|
||||
With nginx-ingress-controller in 0.25.* work only with kubernetes 1.14+, 0.26 fix [this issue](https://github.com/kubernetes/ingress-nginx/pull/4521)
|
||||
|
||||
#### How the Chart Configures the Hooks
|
||||
A validating and configuration requires the endpoint to which the request is sent to use TLS. It is possible to set up custom certificates to do this, but in most cases, a self-signed certificate is enough. The setup of this component requires some more complex orchestration when using helm. The steps are created to be idempotent and to allow turning the feature on and off without running into helm quirks.
|
||||
|
||||
1. A pre-install hook provisions a certificate into the same namespace using a format compatible with provisioning using end user certificates. If the certificate already exists, the hook exits.
|
||||
2. The Ingress-Nginx Controller pod is configured to use a TLS proxy container, which will load that certificate.
|
||||
3. Validating and Mutating webhook configurations are created in the cluster.
|
||||
4. A post-install hook reads the CA from the secret created by step 1 and patches the Validating and Mutating webhook configurations. This process will allow a custom CA provisioned by some other process to also be patched into the webhook configurations. The chosen failure policy is also patched into the webhook configurations
|
||||
|
||||
#### Alternatives
|
||||
It should be possible to use [cert-manager/cert-manager](https://github.com/cert-manager/cert-manager) if a more complete solution is required.
|
||||
|
||||
You can enable automatic self-signed TLS certificate provisioning via cert-manager by setting the `controller.admissionWebhooks.certManager.enabled` value to true.
|
||||
|
||||
Please ensure that cert-manager is correctly installed and configured.
|
||||
|
||||
### Helm Error When Upgrading: spec.clusterIP: Invalid value: ""
|
||||
|
||||
If you are upgrading this chart from a version between 0.31.0 and 1.2.2 then you may get an error like this:
|
||||
@@ -229,10 +229,6 @@ Detail of how and why are in [this issue](https://github.com/helm/charts/pull/13
|
||||
|
||||
As of version `1.26.0` of this chart, by simply not providing any clusterIP value, `invalid: spec.clusterIP: Invalid value: "": field is immutable` will no longer occur since `clusterIP: ""` will not be rendered.
|
||||
|
||||
## Requirements
|
||||
|
||||
Kubernetes: `>=1.19.0-0`
|
||||
|
||||
## Values
|
||||
|
||||
| Key | Type | Default | Description |
|
||||
@@ -240,38 +236,46 @@ Kubernetes: `>=1.19.0-0`
|
||||
| commonLabels | object | `{}` | |
|
||||
| controller.addHeaders | object | `{}` | Will add custom headers before sending response traffic to the client according to: https://kubernetes.github.io/ingress-nginx/user-guide/nginx-configuration/configmap/#add-headers |
|
||||
| controller.admissionWebhooks.annotations | object | `{}` | |
|
||||
| controller.admissionWebhooks.certManager.admissionCert.duration | string | `""` | |
|
||||
| controller.admissionWebhooks.certManager.enabled | bool | `false` | |
|
||||
| controller.admissionWebhooks.certManager.rootCert.duration | string | `""` | |
|
||||
| controller.admissionWebhooks.certificate | string | `"/usr/local/certificates/cert"` | |
|
||||
| controller.admissionWebhooks.createSecretJob.resources | object | `{}` | |
|
||||
| controller.admissionWebhooks.createSecretJob.securityContext.allowPrivilegeEscalation | bool | `false` | |
|
||||
| controller.admissionWebhooks.enabled | bool | `true` | |
|
||||
| controller.admissionWebhooks.existingPsp | string | `""` | Use an existing PSP instead of creating one |
|
||||
| controller.admissionWebhooks.failurePolicy | string | `"Fail"` | |
|
||||
| controller.admissionWebhooks.extraEnvs | list | `[]` | Additional environment variables to set |
|
||||
| controller.admissionWebhooks.failurePolicy | string | `"Fail"` | Admission Webhook failure policy to use |
|
||||
| controller.admissionWebhooks.key | string | `"/usr/local/certificates/key"` | |
|
||||
| controller.admissionWebhooks.labels | object | `{}` | Labels to be added to admission webhooks |
|
||||
| controller.admissionWebhooks.namespaceSelector | object | `{}` | |
|
||||
| controller.admissionWebhooks.objectSelector | object | `{}` | |
|
||||
| controller.admissionWebhooks.patch.enabled | bool | `true` | |
|
||||
| controller.admissionWebhooks.patch.fsGroup | int | `2000` | |
|
||||
| controller.admissionWebhooks.patch.image.digest | string | `"sha256:64d8c73dca984af206adf9d6d7e46aa550362b1d7a01f3a0a91b20cc67868660"` | |
|
||||
| controller.admissionWebhooks.patch.image.digest | string | `"sha256:a7943503b45d552785aa3b5e457f169a5661fb94d82b8a3373bcd9ebaf9aac80"` | |
|
||||
| controller.admissionWebhooks.patch.image.image | string | `"ingress-nginx/kube-webhook-certgen"` | |
|
||||
| controller.admissionWebhooks.patch.image.pullPolicy | string | `"IfNotPresent"` | |
|
||||
| controller.admissionWebhooks.patch.image.registry | string | `"k8s.gcr.io"` | |
|
||||
| controller.admissionWebhooks.patch.image.tag | string | `"v1.1.1"` | |
|
||||
| controller.admissionWebhooks.patch.image.registry | string | `"registry.k8s.io"` | |
|
||||
| controller.admissionWebhooks.patch.image.tag | string | `"v20231011-8b53cabe0"` | |
|
||||
| controller.admissionWebhooks.patch.labels | object | `{}` | Labels to be added to patch job resources |
|
||||
| controller.admissionWebhooks.patch.nodeSelector."kubernetes.io/os" | string | `"linux"` | |
|
||||
| controller.admissionWebhooks.patch.podAnnotations | object | `{}` | |
|
||||
| controller.admissionWebhooks.patch.priorityClassName | string | `""` | Provide a priority class name to the webhook patching job |
|
||||
| controller.admissionWebhooks.patch.runAsUser | int | `2000` | |
|
||||
| controller.admissionWebhooks.patch.priorityClassName | string | `""` | Provide a priority class name to the webhook patching job # |
|
||||
| controller.admissionWebhooks.patch.securityContext.fsGroup | int | `2000` | |
|
||||
| controller.admissionWebhooks.patch.securityContext.runAsNonRoot | bool | `true` | |
|
||||
| controller.admissionWebhooks.patch.securityContext.runAsUser | int | `2000` | |
|
||||
| controller.admissionWebhooks.patch.tolerations | list | `[]` | |
|
||||
| controller.admissionWebhooks.patchWebhookJob.resources | object | `{}` | |
|
||||
| controller.admissionWebhooks.patchWebhookJob.securityContext.allowPrivilegeEscalation | bool | `false` | |
|
||||
| controller.admissionWebhooks.port | int | `8443` | |
|
||||
| controller.admissionWebhooks.service.annotations | object | `{}` | |
|
||||
| controller.admissionWebhooks.service.externalIPs | list | `[]` | |
|
||||
| controller.admissionWebhooks.service.loadBalancerSourceRanges | list | `[]` | |
|
||||
| controller.admissionWebhooks.service.servicePort | int | `443` | |
|
||||
| controller.admissionWebhooks.service.type | string | `"ClusterIP"` | |
|
||||
| controller.affinity | object | `{}` | Affinity and anti-affinity rules for server scheduling to nodes |
|
||||
| controller.allowSnippetAnnotations | bool | `true` | This configuration defines if Ingress Controller should allow users to set their own *-snippet annotations, otherwise this is forbidden / dropped when users add those annotations. Global snippets in ConfigMap are still respected |
|
||||
| controller.annotations | object | `{}` | Annotations to be added to the controller Deployment or DaemonSet |
|
||||
| controller.affinity | object | `{}` | Affinity and anti-affinity rules for server scheduling to nodes # Ref: https://kubernetes.io/docs/concepts/configuration/assign-pod-node/#affinity-and-anti-affinity # |
|
||||
| controller.allowSnippetAnnotations | bool | `false` | This configuration defines if Ingress Controller should allow users to set their own *-snippet annotations, otherwise this is forbidden / dropped when users add those annotations. Global snippets in ConfigMap are still respected |
|
||||
| controller.annotations | object | `{}` | Annotations to be added to the controller Deployment or DaemonSet # |
|
||||
| controller.autoscaling.annotations | object | `{}` | |
|
||||
| controller.autoscaling.behavior | object | `{}` | |
|
||||
| controller.autoscaling.enabled | bool | `false` | |
|
||||
| controller.autoscaling.maxReplicas | int | `11` | |
|
||||
@@ -288,30 +292,35 @@ Kubernetes: `>=1.19.0-0`
|
||||
| controller.customTemplate.configMapName | string | `""` | |
|
||||
| controller.dnsConfig | object | `{}` | Optionally customize the pod dnsConfig. |
|
||||
| controller.dnsPolicy | string | `"ClusterFirst"` | Optionally change this to ClusterFirstWithHostNet in case you have 'hostNetwork: true'. By default, while using host network, name resolution uses the host's DNS. If you wish nginx-controller to keep resolving names inside the k8s network, use ClusterFirstWithHostNet. |
|
||||
| controller.electionID | string | `"ingress-controller-leader"` | Election ID to use for status update |
|
||||
| controller.enableMimalloc | bool | `true` | Enable mimalloc as a drop-in replacement for malloc. |
|
||||
| controller.electionID | string | `""` | Election ID to use for status update, by default it uses the controller name combined with a suffix of 'leader' |
|
||||
| controller.enableAnnotationValidations | bool | `false` | |
|
||||
| controller.enableMimalloc | bool | `true` | Enable mimalloc as a drop-in replacement for malloc. # ref: https://github.com/microsoft/mimalloc # |
|
||||
| controller.enableTopologyAwareRouting | bool | `false` | This configuration enables Topology Aware Routing feature, used together with service annotation service.kubernetes.io/topology-mode="auto" Defaults to false |
|
||||
| controller.existingPsp | string | `""` | Use an existing PSP instead of creating one |
|
||||
| controller.extraArgs | object | `{}` | Additional command line arguments to pass to nginx-ingress-controller E.g. to specify the default SSL certificate you can use |
|
||||
| controller.extraArgs | object | `{}` | Additional command line arguments to pass to Ingress-Nginx Controller E.g. to specify the default SSL certificate you can use |
|
||||
| controller.extraContainers | list | `[]` | Additional containers to be added to the controller pod. See https://github.com/lemonldap-ng-controller/lemonldap-ng-controller as example. |
|
||||
| controller.extraEnvs | list | `[]` | Additional environment variables to set |
|
||||
| controller.extraInitContainers | list | `[]` | Containers, which are run before the app containers are started. |
|
||||
| controller.extraModules | list | `[]` | |
|
||||
| controller.extraModules | list | `[]` | Modules, which are mounted into the core nginx image. See values.yaml for a sample to add opentelemetry module |
|
||||
| controller.extraVolumeMounts | list | `[]` | Additional volumeMounts to the controller main container. |
|
||||
| controller.extraVolumes | list | `[]` | Additional volumes to the controller pod. |
|
||||
| controller.healthCheckHost | string | `""` | Address to bind the health check endpoint. It is better to set this option to the internal node address if the ingress nginx controller is running in the `hostNetwork: true` mode. |
|
||||
| controller.healthCheckHost | string | `""` | Address to bind the health check endpoint. It is better to set this option to the internal node address if the Ingress-Nginx Controller is running in the `hostNetwork: true` mode. |
|
||||
| controller.healthCheckPath | string | `"/healthz"` | Path of the health check endpoint. All requests received on the port defined by the healthz-port parameter are forwarded internally to this path. |
|
||||
| controller.hostAliases | list | `[]` | Optionally customize the pod hostAliases. |
|
||||
| controller.hostNetwork | bool | `false` | Required for use with CNI based kubernetes installations (such as ones set up by kubeadm), since CNI and hostport don't mix yet. Can be deprecated once https://github.com/kubernetes/kubernetes/issues/23920 is merged |
|
||||
| controller.hostPort.enabled | bool | `false` | Enable 'hostPort' or not |
|
||||
| controller.hostPort.ports.http | int | `80` | 'hostPort' http port |
|
||||
| controller.hostPort.ports.https | int | `443` | 'hostPort' https port |
|
||||
| controller.hostname | object | `{}` | Optionally customize the pod hostname. |
|
||||
| controller.image.allowPrivilegeEscalation | bool | `true` | |
|
||||
| controller.image.digest | string | `"sha256:31f47c1e202b39fadecf822a9b76370bd4baed199a005b3e7d4d1455f4fd3fe2"` | |
|
||||
| controller.image.chroot | bool | `false` | |
|
||||
| controller.image.digest | string | `"sha256:5b161f051d017e55d358435f295f5e9a297e66158f136321d9b04520ec6c48a3"` | |
|
||||
| controller.image.digestChroot | string | `"sha256:5976b1067cfbca8a21d0ba53d71f83543a73316a61ea7f7e436d6cf84ddf9b26"` | |
|
||||
| controller.image.image | string | `"ingress-nginx/controller"` | |
|
||||
| controller.image.pullPolicy | string | `"IfNotPresent"` | |
|
||||
| controller.image.registry | string | `"k8s.gcr.io"` | |
|
||||
| controller.image.registry | string | `"registry.k8s.io"` | |
|
||||
| controller.image.runAsUser | int | `101` | |
|
||||
| controller.image.tag | string | `"v1.1.3"` | |
|
||||
| controller.image.tag | string | `"v1.9.4"` | |
|
||||
| controller.ingressClass | string | `"nginx"` | For backwards compatibility with ingress.class annotation, use ingressClass. Algorithm is as follows, first ingressClassName is considered, if not present, controller looks for ingress.class annotation |
|
||||
| controller.ingressClassByName | bool | `false` | Process IngressClass per name (additionally as per spec.controller). |
|
||||
| controller.ingressClassResource.controllerValue | string | `"k8s.io/ingress-nginx"` | Controller-value of the controller that is processing this ingressClass |
|
||||
@@ -330,8 +339,8 @@ Kubernetes: `>=1.19.0-0`
|
||||
| controller.keda.scaledObject.annotations | object | `{}` | |
|
||||
| controller.keda.triggers | list | `[]` | |
|
||||
| controller.kind | string | `"Deployment"` | Use a `DaemonSet` or `Deployment` |
|
||||
| controller.labels | object | `{}` | Labels to be added to the controller Deployment or DaemonSet and other resources that do not have option to specify labels |
|
||||
| controller.lifecycle | object | `{"preStop":{"exec":{"command":["/wait-shutdown"]}}}` | Improve connection draining when ingress controller pod is deleted using a lifecycle hook: With this new hook, we increased the default terminationGracePeriodSeconds from 30 seconds to 300, allowing the draining of connections up to five minutes. If the active connections end before that, the pod will terminate gracefully at that time. To effectively take advantage of this feature, the Configmap feature worker-shutdown-timeout new value is 240s instead of 10s. |
|
||||
| controller.labels | object | `{}` | Labels to be added to the controller Deployment or DaemonSet and other resources that do not have option to specify labels # |
|
||||
| controller.lifecycle | object | `{"preStop":{"exec":{"command":["/wait-shutdown"]}}}` | Improve connection draining when ingress controller pod is deleted using a lifecycle hook: With this new hook, we increased the default terminationGracePeriodSeconds from 30 seconds to 300, allowing the draining of connections up to five minutes. If the active connections end before that, the pod will terminate gracefully at that time. To effectively take advantage of this feature, the Configmap feature worker-shutdown-timeout new value is 240s instead of 10s. # |
|
||||
| controller.livenessProbe.failureThreshold | int | `5` | |
|
||||
| controller.livenessProbe.httpGet.path | string | `"/healthz"` | |
|
||||
| controller.livenessProbe.httpGet.port | int | `10254` | |
|
||||
@@ -340,14 +349,16 @@ Kubernetes: `>=1.19.0-0`
|
||||
| controller.livenessProbe.periodSeconds | int | `10` | |
|
||||
| controller.livenessProbe.successThreshold | int | `1` | |
|
||||
| controller.livenessProbe.timeoutSeconds | int | `1` | |
|
||||
| controller.maxmindLicenseKey | string | `""` | Maxmind license key to download GeoLite2 Databases. |
|
||||
| controller.maxmindLicenseKey | string | `""` | Maxmind license key to download GeoLite2 Databases. # https://blog.maxmind.com/2019/12/18/significant-changes-to-accessing-and-using-geolite2-databases |
|
||||
| controller.metrics.enabled | bool | `false` | |
|
||||
| controller.metrics.port | int | `10254` | |
|
||||
| controller.metrics.portName | string | `"metrics"` | |
|
||||
| controller.metrics.prometheusRule.additionalLabels | object | `{}` | |
|
||||
| controller.metrics.prometheusRule.enabled | bool | `false` | |
|
||||
| controller.metrics.prometheusRule.rules | list | `[]` | |
|
||||
| controller.metrics.service.annotations | object | `{}` | |
|
||||
| controller.metrics.service.externalIPs | list | `[]` | List of IP addresses at which the stats-exporter service is available |
|
||||
| controller.metrics.service.externalIPs | list | `[]` | List of IP addresses at which the stats-exporter service is available # Ref: https://kubernetes.io/docs/concepts/services-networking/service/#external-ips # |
|
||||
| controller.metrics.service.labels | object | `{}` | Labels to be added to the metrics service resource |
|
||||
| controller.metrics.service.loadBalancerSourceRanges | list | `[]` | |
|
||||
| controller.metrics.service.servicePort | int | `10254` | |
|
||||
| controller.metrics.service.type | string | `"ClusterIP"` | |
|
||||
@@ -359,11 +370,16 @@ Kubernetes: `>=1.19.0-0`
|
||||
| controller.metrics.serviceMonitor.relabelings | list | `[]` | |
|
||||
| controller.metrics.serviceMonitor.scrapeInterval | string | `"30s"` | |
|
||||
| controller.metrics.serviceMonitor.targetLabels | list | `[]` | |
|
||||
| controller.minAvailable | int | `1` | |
|
||||
| controller.minReadySeconds | int | `0` | `minReadySeconds` to avoid killing pods before we are ready |
|
||||
| controller.minAvailable | int | `1` | Minimum available pods set in PodDisruptionBudget. Define either 'minAvailable' or 'maxUnavailable', never both. |
|
||||
| controller.minReadySeconds | int | `0` | `minReadySeconds` to avoid killing pods before we are ready # |
|
||||
| controller.name | string | `"controller"` | |
|
||||
| controller.nodeSelector | object | `{"kubernetes.io/os":"linux"}` | Node labels for controller pod assignment |
|
||||
| controller.podAnnotations | object | `{}` | Annotations to be added to controller pods |
|
||||
| controller.networkPolicy.enabled | bool | `false` | Enable 'networkPolicy' or not |
|
||||
| controller.nodeSelector | object | `{"kubernetes.io/os":"linux"}` | Node labels for controller pod assignment # Ref: https://kubernetes.io/docs/concepts/scheduling-eviction/assign-pod-node/ # |
|
||||
| controller.opentelemetry.containerSecurityContext.allowPrivilegeEscalation | bool | `false` | |
|
||||
| controller.opentelemetry.enabled | bool | `false` | |
|
||||
| controller.opentelemetry.image | string | `"registry.k8s.io/ingress-nginx/opentelemetry:v20230721-3e2062ee5@sha256:13bee3f5223883d3ca62fee7309ad02d22ec00ff0d7033e3e9aca7a9f60fd472"` | |
|
||||
| controller.opentelemetry.resources | object | `{}` | |
|
||||
| controller.podAnnotations | object | `{}` | Annotations to be added to controller pods # |
|
||||
| controller.podLabels | object | `{}` | Labels to add to the pod container metadata |
|
||||
| controller.podSecurityContext | object | `{}` | Security Context policies for controller pods |
|
||||
| controller.priorityClassName | string | `""` | |
|
||||
@@ -380,25 +396,30 @@ Kubernetes: `>=1.19.0-0`
|
||||
| controller.readinessProbe.successThreshold | int | `1` | |
|
||||
| controller.readinessProbe.timeoutSeconds | int | `1` | |
|
||||
| controller.replicaCount | int | `1` | |
|
||||
| controller.reportNodeInternalIp | bool | `false` | Bare-metal considerations via the host network https://kubernetes.github.io/ingress-nginx/deploy/baremetal/#via-the-host-network Ingress status was blank because there is no Service exposing the NGINX Ingress controller in a configuration using the host network, the default --publish-service flag used in standard cloud setups does not apply |
|
||||
| controller.reportNodeInternalIp | bool | `false` | Bare-metal considerations via the host network https://kubernetes.github.io/ingress-nginx/deploy/baremetal/#via-the-host-network Ingress status was blank because there is no Service exposing the Ingress-Nginx Controller in a configuration using the host network, the default --publish-service flag used in standard cloud setups does not apply |
|
||||
| controller.resources.requests.cpu | string | `"100m"` | |
|
||||
| controller.resources.requests.memory | string | `"90Mi"` | |
|
||||
| controller.scope.enabled | bool | `false` | Enable 'scope' or not |
|
||||
| controller.scope.namespace | string | `""` | Namespace to limit the controller to; defaults to $(POD_NAMESPACE) |
|
||||
| controller.scope.namespaceSelector | string | `""` | When scope.enabled == false, instead of watching all namespaces, we watching namespaces whose labels only match with namespaceSelector. Format like foo=bar. Defaults to empty, means watching all namespaces. |
|
||||
| controller.service.annotations | object | `{}` | |
|
||||
| controller.service.appProtocol | bool | `true` | If enabled is adding an appProtocol option for Kubernetes service. An appProtocol field replacing annotations that were using for setting a backend protocol. Here is an example for AWS: service.beta.kubernetes.io/aws-load-balancer-backend-protocol: http It allows choosing the protocol for each backend specified in the Kubernetes service. See the following GitHub issue for more details about the purpose: https://github.com/kubernetes/kubernetes/issues/40244 Will be ignored for Kubernetes versions older than 1.20 |
|
||||
| controller.service.annotations | object | `{}` | Annotations are mandatory for the load balancer to come up. Varies with the cloud service. Values passed through helm tpl engine. |
|
||||
| controller.service.appProtocol | bool | `true` | If enabled is adding an appProtocol option for Kubernetes service. An appProtocol field replacing annotations that were using for setting a backend protocol. Here is an example for AWS: service.beta.kubernetes.io/aws-load-balancer-backend-protocol: http It allows choosing the protocol for each backend specified in the Kubernetes service. See the following GitHub issue for more details about the purpose: https://github.com/kubernetes/kubernetes/issues/40244 Will be ignored for Kubernetes versions older than 1.20 # |
|
||||
| controller.service.enableHttp | bool | `true` | |
|
||||
| controller.service.enableHttps | bool | `true` | |
|
||||
| controller.service.enabled | bool | `true` | |
|
||||
| controller.service.external.enabled | bool | `true` | |
|
||||
| controller.service.externalIPs | list | `[]` | List of IP addresses at which the controller services are available |
|
||||
| controller.service.internal.annotations | object | `{}` | Annotations are mandatory for the load balancer to come up. Varies with the cloud service. |
|
||||
| controller.service.externalIPs | list | `[]` | List of IP addresses at which the controller services are available # Ref: https://kubernetes.io/docs/concepts/services-networking/service/#external-ips # |
|
||||
| controller.service.internal.annotations | object | `{}` | Annotations are mandatory for the load balancer to come up. Varies with the cloud service. Values passed through helm tpl engine. |
|
||||
| controller.service.internal.enabled | bool | `false` | Enables an additional internal load balancer (besides the external one). |
|
||||
| controller.service.internal.loadBalancerIP | string | `""` | Used by cloud providers to connect the resulting internal LoadBalancer to a pre-existing static IP. Make sure to add to the service the needed annotation to specify the subnet which the static IP belongs to. For instance, `networking.gke.io/internal-load-balancer-subnet` for GCP and `service.beta.kubernetes.io/aws-load-balancer-subnets` for AWS. |
|
||||
| controller.service.internal.loadBalancerSourceRanges | list | `[]` | Restrict access For LoadBalancer service. Defaults to 0.0.0.0/0. |
|
||||
| controller.service.ipFamilies | list | `["IPv4"]` | List of IP families (e.g. IPv4, IPv6) assigned to the service. This field is usually assigned automatically based on cluster configuration and the ipFamilyPolicy field. |
|
||||
| controller.service.ipFamilyPolicy | string | `"SingleStack"` | Represents the dual-stack-ness requested or required by this Service. Possible values are SingleStack, PreferDualStack or RequireDualStack. The ipFamilies and clusterIPs fields depend on the value of this field. |
|
||||
| controller.service.internal.ports | object | `{}` | Custom port mapping for internal service |
|
||||
| controller.service.internal.targetPorts | object | `{}` | Custom target port mapping for internal service |
|
||||
| controller.service.ipFamilies | list | `["IPv4"]` | List of IP families (e.g. IPv4, IPv6) assigned to the service. This field is usually assigned automatically based on cluster configuration and the ipFamilyPolicy field. # Ref: https://kubernetes.io/docs/concepts/services-networking/dual-stack/ |
|
||||
| controller.service.ipFamilyPolicy | string | `"SingleStack"` | Represents the dual-stack-ness requested or required by this Service. Possible values are SingleStack, PreferDualStack or RequireDualStack. The ipFamilies and clusterIPs fields depend on the value of this field. # Ref: https://kubernetes.io/docs/concepts/services-networking/dual-stack/ |
|
||||
| controller.service.labels | object | `{}` | |
|
||||
| controller.service.loadBalancerClass | string | `""` | Used by cloud providers to select a load balancer implementation other than the cloud provider default. https://kubernetes.io/docs/concepts/services-networking/service/#load-balancer-class |
|
||||
| controller.service.loadBalancerIP | string | `""` | Used by cloud providers to connect the resulting `LoadBalancer` to a pre-existing static IP according to https://kubernetes.io/docs/concepts/services-networking/service/#loadbalancer |
|
||||
| controller.service.loadBalancerSourceRanges | list | `[]` | |
|
||||
| controller.service.nodePorts.http | string | `""` | |
|
||||
| controller.service.nodePorts.https | string | `""` | |
|
||||
@@ -409,16 +430,16 @@ Kubernetes: `>=1.19.0-0`
|
||||
| controller.service.targetPorts.http | string | `"http"` | |
|
||||
| controller.service.targetPorts.https | string | `"https"` | |
|
||||
| controller.service.type | string | `"LoadBalancer"` | |
|
||||
| controller.shareProcessNamespace | bool | `false` | This can be used for example to signal log rotation using `kill -USR1` from a sidecar. |
|
||||
| controller.shareProcessNamespace | bool | `false` | |
|
||||
| controller.sysctls | object | `{}` | See https://kubernetes.io/docs/tasks/administer-cluster/sysctl-cluster/ for notes on enabling and using sysctls |
|
||||
| controller.tcp.annotations | object | `{}` | Annotations to be added to the tcp config configmap |
|
||||
| controller.tcp.configMapNamespace | string | `""` | Allows customization of the tcp-services-configmap; defaults to $(POD_NAMESPACE) |
|
||||
| controller.terminationGracePeriodSeconds | int | `300` | `terminationGracePeriodSeconds` to avoid killing pods before we are ready |
|
||||
| controller.tolerations | list | `[]` | Node tolerations for server scheduling to nodes with taints |
|
||||
| controller.topologySpreadConstraints | list | `[]` | Topology spread constraints rely on node labels to identify the topology domain(s) that each Node is in. |
|
||||
| controller.terminationGracePeriodSeconds | int | `300` | `terminationGracePeriodSeconds` to avoid killing pods before we are ready # wait up to five minutes for the drain of connections # |
|
||||
| controller.tolerations | list | `[]` | Node tolerations for server scheduling to nodes with taints # Ref: https://kubernetes.io/docs/concepts/configuration/assign-pod-node/ # |
|
||||
| controller.topologySpreadConstraints | list | `[]` | Topology spread constraints rely on node labels to identify the topology domain(s) that each Node is in. # Ref: https://kubernetes.io/docs/concepts/workloads/pods/pod-topology-spread-constraints/ # |
|
||||
| controller.udp.annotations | object | `{}` | Annotations to be added to the udp config configmap |
|
||||
| controller.udp.configMapNamespace | string | `""` | Allows customization of the udp-services-configmap; defaults to $(POD_NAMESPACE) |
|
||||
| controller.updateStrategy | object | `{}` | The update strategy to apply to the Deployment or DaemonSet |
|
||||
| controller.updateStrategy | object | `{}` | The update strategy to apply to the Deployment or DaemonSet # |
|
||||
| controller.watchIngressWithoutClass | bool | `false` | Process Ingress objects without ingressClass annotation/ingressClassName field Overrides value for --watch-ingress-without-class flag of the controller binary Defaults to false |
|
||||
| defaultBackend.affinity | object | `{}` | |
|
||||
| defaultBackend.autoscaling.annotations | object | `{}` | |
|
||||
@@ -427,7 +448,7 @@ Kubernetes: `>=1.19.0-0`
|
||||
| defaultBackend.autoscaling.minReplicas | int | `1` | |
|
||||
| defaultBackend.autoscaling.targetCPUUtilizationPercentage | int | `50` | |
|
||||
| defaultBackend.autoscaling.targetMemoryUtilizationPercentage | int | `50` | |
|
||||
| defaultBackend.containerSecurityContext | object | `{}` | Security Context policies for controller main container. See https://kubernetes.io/docs/tasks/administer-cluster/sysctl-cluster/ for notes on enabling and using sysctls |
|
||||
| defaultBackend.containerSecurityContext | object | `{}` | Security Context policies for controller main container. See https://kubernetes.io/docs/tasks/administer-cluster/sysctl-cluster/ for notes on enabling and using sysctls # |
|
||||
| defaultBackend.enabled | bool | `false` | |
|
||||
| defaultBackend.existingPsp | string | `""` | Use an existing PSP instead of creating one |
|
||||
| defaultBackend.extraArgs | object | `{}` | |
|
||||
@@ -438,7 +459,7 @@ Kubernetes: `>=1.19.0-0`
|
||||
| defaultBackend.image.image | string | `"defaultbackend-amd64"` | |
|
||||
| defaultBackend.image.pullPolicy | string | `"IfNotPresent"` | |
|
||||
| defaultBackend.image.readOnlyRootFilesystem | bool | `true` | |
|
||||
| defaultBackend.image.registry | string | `"k8s.gcr.io"` | |
|
||||
| defaultBackend.image.registry | string | `"registry.k8s.io"` | |
|
||||
| defaultBackend.image.runAsNonRoot | bool | `true` | |
|
||||
| defaultBackend.image.runAsUser | int | `65534` | |
|
||||
| defaultBackend.image.tag | string | `"1.5"` | |
|
||||
@@ -449,11 +470,13 @@ Kubernetes: `>=1.19.0-0`
|
||||
| defaultBackend.livenessProbe.successThreshold | int | `1` | |
|
||||
| defaultBackend.livenessProbe.timeoutSeconds | int | `5` | |
|
||||
| defaultBackend.minAvailable | int | `1` | |
|
||||
| defaultBackend.minReadySeconds | int | `0` | `minReadySeconds` to avoid killing pods before we are ready # |
|
||||
| defaultBackend.name | string | `"defaultbackend"` | |
|
||||
| defaultBackend.nodeSelector | object | `{"kubernetes.io/os":"linux"}` | Node labels for default backend pod assignment |
|
||||
| defaultBackend.podAnnotations | object | `{}` | Annotations to be added to default backend pods |
|
||||
| defaultBackend.networkPolicy.enabled | bool | `false` | Enable 'networkPolicy' or not |
|
||||
| defaultBackend.nodeSelector | object | `{"kubernetes.io/os":"linux"}` | Node labels for default backend pod assignment # Ref: https://kubernetes.io/docs/concepts/scheduling-eviction/assign-pod-node/ # |
|
||||
| defaultBackend.podAnnotations | object | `{}` | Annotations to be added to default backend pods # |
|
||||
| defaultBackend.podLabels | object | `{}` | Labels to add to the pod container metadata |
|
||||
| defaultBackend.podSecurityContext | object | `{}` | Security Context policies for controller pods See https://kubernetes.io/docs/tasks/administer-cluster/sysctl-cluster/ for notes on enabling and using sysctls |
|
||||
| defaultBackend.podSecurityContext | object | `{}` | Security Context policies for controller pods See https://kubernetes.io/docs/tasks/administer-cluster/sysctl-cluster/ for notes on enabling and using sysctls # |
|
||||
| defaultBackend.port | int | `8080` | |
|
||||
| defaultBackend.priorityClassName | string | `""` | |
|
||||
| defaultBackend.readinessProbe.failureThreshold | int | `6` | |
|
||||
@@ -464,24 +487,26 @@ Kubernetes: `>=1.19.0-0`
|
||||
| defaultBackend.replicaCount | int | `1` | |
|
||||
| defaultBackend.resources | object | `{}` | |
|
||||
| defaultBackend.service.annotations | object | `{}` | |
|
||||
| defaultBackend.service.externalIPs | list | `[]` | List of IP addresses at which the default backend service is available |
|
||||
| defaultBackend.service.externalIPs | list | `[]` | List of IP addresses at which the default backend service is available # Ref: https://kubernetes.io/docs/concepts/services-networking/service/#external-ips # |
|
||||
| defaultBackend.service.loadBalancerSourceRanges | list | `[]` | |
|
||||
| defaultBackend.service.servicePort | int | `80` | |
|
||||
| defaultBackend.service.type | string | `"ClusterIP"` | |
|
||||
| defaultBackend.serviceAccount.automountServiceAccountToken | bool | `true` | |
|
||||
| defaultBackend.serviceAccount.create | bool | `true` | |
|
||||
| defaultBackend.serviceAccount.name | string | `""` | |
|
||||
| defaultBackend.tolerations | list | `[]` | Node tolerations for server scheduling to nodes with taints |
|
||||
| dhParam | string | `nil` | A base64-encoded Diffie-Hellman parameter. This can be generated with: `openssl dhparam 4096 2> /dev/null | base64` |
|
||||
| imagePullSecrets | list | `[]` | Optional array of imagePullSecrets containing private registry credentials |
|
||||
| defaultBackend.tolerations | list | `[]` | Node tolerations for server scheduling to nodes with taints # Ref: https://kubernetes.io/docs/concepts/configuration/assign-pod-node/ # |
|
||||
| defaultBackend.updateStrategy | object | `{}` | The update strategy to apply to the Deployment or DaemonSet # |
|
||||
| dhParam | string | `""` | A base64-encoded Diffie-Hellman parameter. This can be generated with: `openssl dhparam 4096 2> /dev/null | base64` # Ref: https://github.com/kubernetes/ingress-nginx/tree/main/docs/examples/customization/ssl-dh-param |
|
||||
| imagePullSecrets | list | `[]` | Optional array of imagePullSecrets containing private registry credentials # Ref: https://kubernetes.io/docs/tasks/configure-pod-container/pull-image-private-registry/ |
|
||||
| namespaceOverride | string | `""` | Override the deployment namespace; defaults to .Release.Namespace |
|
||||
| podSecurityPolicy.enabled | bool | `false` | |
|
||||
| portNamePrefix | string | `""` | Prefix for TCP and UDP ports names in ingress controller service # Some cloud providers, like Yandex Cloud may have a requirements for a port name regex to support cloud load balancer integration |
|
||||
| rbac.create | bool | `true` | |
|
||||
| rbac.scope | bool | `false` | |
|
||||
| revisionHistoryLimit | int | `10` | Rollback limit |
|
||||
| revisionHistoryLimit | int | `10` | Rollback limit # |
|
||||
| serviceAccount.annotations | object | `{}` | Annotations for the controller service account |
|
||||
| serviceAccount.automountServiceAccountToken | bool | `true` | |
|
||||
| serviceAccount.create | bool | `true` | |
|
||||
| serviceAccount.name | string | `""` | |
|
||||
| tcp | object | `{}` | TCP service key:value pairs |
|
||||
| udp | object | `{}` | UDP service key:value pairs |
|
||||
|
||||
| tcp | object | `{}` | TCP service key-value pairs # Ref: https://github.com/kubernetes/ingress-nginx/blob/main/docs/user-guide/exposing-tcp-udp-services.md # |
|
||||
| udp | object | `{}` | UDP service key-value pairs # Ref: https://github.com/kubernetes/ingress-nginx/blob/main/docs/user-guide/exposing-tcp-udp-services.md # |
|
||||
|
||||
@@ -7,10 +7,7 @@ To use, add `ingressClassName: nginx` spec field or the `kubernetes.io/ingress.c
|
||||
|
||||
This chart bootstraps an ingress-nginx deployment on a [Kubernetes](http://kubernetes.io) cluster using the [Helm](https://helm.sh) package manager.
|
||||
|
||||
## Prerequisites
|
||||
|
||||
- Chart version 3.x.x: Kubernetes v1.16+
|
||||
- Chart version 4.x.x and above: Kubernetes v1.19+
|
||||
{{ template "chart.requirementsSection" . }}
|
||||
|
||||
## Get Repo Info
|
||||
|
||||
@@ -51,10 +48,6 @@ helm upgrade [RELEASE_NAME] [CHART] --install
|
||||
|
||||
_See [helm upgrade](https://helm.sh/docs/helm/helm_upgrade/) for command documentation._
|
||||
|
||||
### Upgrading With Zero Downtime in Production
|
||||
|
||||
By default the ingress-nginx controller has service interruptions whenever it's pods are restarted or redeployed. In order to fix that, see the excellent blog post by Lindsay Landry from Codecademy: [Kubernetes: Nginx and Zero Downtime in Production](https://medium.com/codecademy-engineering/kubernetes-nginx-and-zero-downtime-in-production-2c910c6a5ed8).
|
||||
|
||||
### Migrating from stable/nginx-ingress
|
||||
|
||||
There are two main ways to migrate a release from `stable/nginx-ingress` to `ingress-nginx/ingress-nginx` chart:
|
||||
@@ -65,7 +58,6 @@ There are two main ways to migrate a release from `stable/nginx-ingress` to `ing
|
||||
1. Redirect your DNS traffic from the old controller to the new controller
|
||||
1. Log traffic from both controllers during this changeover
|
||||
1. [Uninstall](#uninstall-chart) the old controller once traffic has fully drained from it
|
||||
1. For details on all of these steps see [Upgrading With Zero Downtime in Production](#upgrading-with-zero-downtime-in-production)
|
||||
|
||||
Note that there are some different and upgraded configurations between the two charts, described by Rimas Mocevicius from JFrog in the "Upgrading to ingress-nginx Helm chart" section of [Migrating from Helm chart nginx-ingress to ingress-nginx](https://rimusz.net/migrating-to-ingress-nginx). As the `ingress-nginx/ingress-nginx` chart continues to update, you will want to check current differences by running [helm configuration](#configuration) commands on both charts.
|
||||
|
||||
@@ -84,14 +76,14 @@ else it would make it impossible to evacuate a node. See [gh issue #7127](https:
|
||||
|
||||
### Prometheus Metrics
|
||||
|
||||
The Nginx ingress controller can export Prometheus metrics, by setting `controller.metrics.enabled` to `true`.
|
||||
The Ingress-Nginx Controller can export Prometheus metrics, by setting `controller.metrics.enabled` to `true`.
|
||||
|
||||
You can add Prometheus annotations to the metrics service using `controller.metrics.service.annotations`.
|
||||
Alternatively, if you use the Prometheus Operator, you can enable ServiceMonitor creation using `controller.metrics.serviceMonitor.enabled`. And set `controller.metrics.serviceMonitor.additionalLabels.release="prometheus"`. "release=prometheus" should match the label configured in the prometheus servicemonitor ( see `kubectl get servicemonitor prometheus-kube-prom-prometheus -oyaml -n prometheus`)
|
||||
|
||||
### ingress-nginx nginx\_status page/stats server
|
||||
|
||||
Previous versions of this chart had a `controller.stats.*` configuration block, which is now obsolete due to the following changes in nginx ingress controller:
|
||||
Previous versions of this chart had a `controller.stats.*` configuration block, which is now obsolete due to the following changes in Ingress-Nginx Controller:
|
||||
|
||||
- In [0.16.1](https://github.com/kubernetes/ingress-nginx/blob/main/Changelog.md#0161), the vts (virtual host traffic status) dashboard was removed
|
||||
- In [0.23.0](https://github.com/kubernetes/ingress-nginx/blob/main/Changelog.md#0230), the status page at port 18080 is now a unix socket webserver only available at localhost.
|
||||
@@ -99,7 +91,7 @@ Previous versions of this chart had a `controller.stats.*` configuration block,
|
||||
|
||||
### ExternalDNS Service Configuration
|
||||
|
||||
Add an [ExternalDNS](https://github.com/kubernetes-incubator/external-dns) annotation to the LoadBalancer service:
|
||||
Add an [ExternalDNS](https://github.com/kubernetes-sigs/external-dns) annotation to the LoadBalancer service:
|
||||
|
||||
```yaml
|
||||
controller:
|
||||
@@ -110,7 +102,7 @@ controller:
|
||||
|
||||
### AWS L7 ELB with SSL Termination
|
||||
|
||||
Annotate the controller as shown in the [nginx-ingress l7 patch](https://github.com/kubernetes/ingress-nginx/blob/main/deploy/aws/l7/service-l7.yaml):
|
||||
Annotate the controller as shown in the [nginx-ingress l7 patch](https://github.com/kubernetes/ingress-nginx/blob/ab3a789caae65eec4ad6e3b46b19750b481b6bce/deploy/aws/l7/service-l7.yaml):
|
||||
|
||||
```yaml
|
||||
controller:
|
||||
@@ -125,19 +117,6 @@ controller:
|
||||
service.beta.kubernetes.io/aws-load-balancer-connection-idle-timeout: '3600'
|
||||
```
|
||||
|
||||
### AWS route53-mapper
|
||||
|
||||
To configure the LoadBalancer service with the [route53-mapper addon](https://github.com/kubernetes/kops/tree/master/addons/route53-mapper), add the `domainName` annotation and `dns` label:
|
||||
|
||||
```yaml
|
||||
controller:
|
||||
service:
|
||||
labels:
|
||||
dns: "route53"
|
||||
annotations:
|
||||
domainName: "kubernetes-example.com"
|
||||
```
|
||||
|
||||
### Additional Internal Load Balancer
|
||||
|
||||
This setup is useful when you need both external and internal load balancers but don't want to have multiple ingress controllers and multiple ingress objects per application.
|
||||
@@ -161,8 +140,10 @@ controller:
|
||||
internal:
|
||||
enabled: true
|
||||
annotations:
|
||||
# Create internal ELB
|
||||
service.beta.kubernetes.io/aws-load-balancer-internal: "true"
|
||||
# Create internal NLB
|
||||
service.beta.kubernetes.io/aws-load-balancer-scheme: "internal"
|
||||
# Create internal ELB(Deprecated)
|
||||
# service.beta.kubernetes.io/aws-load-balancer-internal: "true"
|
||||
# Any other annotation can be declared here.
|
||||
```
|
||||
|
||||
@@ -174,7 +155,7 @@ controller:
|
||||
internal:
|
||||
enabled: true
|
||||
annotations:
|
||||
# Create internal LB. More informations: https://cloud.google.com/kubernetes-engine/docs/how-to/internal-load-balancing
|
||||
# Create internal LB. More information: https://cloud.google.com/kubernetes-engine/docs/how-to/internal-load-balancing
|
||||
# For GKE versions 1.17 and later
|
||||
networking.gke.io/load-balancer-type: "Internal"
|
||||
# For earlier versions
|
||||
@@ -205,17 +186,34 @@ controller:
|
||||
# Any other annotation can be declared here.
|
||||
```
|
||||
|
||||
The load balancer annotations of more cloud service providers can be found: [Internal load balancer](https://kubernetes.io/docs/concepts/services-networking/service/#internal-load-balancer).
|
||||
|
||||
An use case for this scenario is having a split-view DNS setup where the public zone CNAME records point to the external balancer URL while the private zone CNAME records point to the internal balancer URL. This way, you only need one ingress kubernetes object.
|
||||
|
||||
Optionally you can set `controller.service.loadBalancerIP` if you need a static IP for the resulting `LoadBalancer`.
|
||||
|
||||
### Ingress Admission Webhooks
|
||||
|
||||
With nginx-ingress-controller version 0.25+, the nginx ingress controller pod exposes an endpoint that will integrate with the `validatingwebhookconfiguration` Kubernetes feature to prevent bad ingress from being added to the cluster.
|
||||
With nginx-ingress-controller version 0.25+, the Ingress-Nginx Controller pod exposes an endpoint that will integrate with the `validatingwebhookconfiguration` Kubernetes feature to prevent bad ingress from being added to the cluster.
|
||||
**This feature is enabled by default since 0.31.0.**
|
||||
|
||||
With nginx-ingress-controller in 0.25.* work only with kubernetes 1.14+, 0.26 fix [this issue](https://github.com/kubernetes/ingress-nginx/pull/4521)
|
||||
|
||||
#### How the Chart Configures the Hooks
|
||||
A validating and configuration requires the endpoint to which the request is sent to use TLS. It is possible to set up custom certificates to do this, but in most cases, a self-signed certificate is enough. The setup of this component requires some more complex orchestration when using helm. The steps are created to be idempotent and to allow turning the feature on and off without running into helm quirks.
|
||||
|
||||
1. A pre-install hook provisions a certificate into the same namespace using a format compatible with provisioning using end user certificates. If the certificate already exists, the hook exits.
|
||||
2. The Ingress-Nginx Controller pod is configured to use a TLS proxy container, which will load that certificate.
|
||||
3. Validating and Mutating webhook configurations are created in the cluster.
|
||||
4. A post-install hook reads the CA from the secret created by step 1 and patches the Validating and Mutating webhook configurations. This process will allow a custom CA provisioned by some other process to also be patched into the webhook configurations. The chosen failure policy is also patched into the webhook configurations
|
||||
|
||||
#### Alternatives
|
||||
It should be possible to use [cert-manager/cert-manager](https://github.com/cert-manager/cert-manager) if a more complete solution is required.
|
||||
|
||||
You can enable automatic self-signed TLS certificate provisioning via cert-manager by setting the `controller.admissionWebhooks.certManager.enabled` value to true.
|
||||
|
||||
Please ensure that cert-manager is correctly installed and configured.
|
||||
|
||||
### Helm Error When Upgrading: spec.clusterIP: Invalid value: ""
|
||||
|
||||
If you are upgrading this chart from a version between 0.31.0 and 1.2.2 then you may get an error like this:
|
||||
@@ -228,8 +226,4 @@ Detail of how and why are in [this issue](https://github.com/helm/charts/pull/13
|
||||
|
||||
As of version `1.26.0` of this chart, by simply not providing any clusterIP value, `invalid: spec.clusterIP: Invalid value: "": field is immutable` will no longer occur since `clusterIP: ""` will not be rendered.
|
||||
|
||||
{{ template "chart.requirementsSection" . }}
|
||||
|
||||
{{ template "chart.valuesSection" . }}
|
||||
|
||||
{{ template "helm-docs.versionFooter" . }}
|
||||
|
||||
@@ -0,0 +1,9 @@
|
||||
# Changelog
|
||||
|
||||
This file documents all notable changes to [ingress-nginx](https://github.com/kubernetes/ingress-nginx) Helm Chart. The release numbering uses [semantic versioning](http://semver.org).
|
||||
|
||||
### {{ .NewHelmChartVersion }}
|
||||
{{ with .HelmUpdates }}
|
||||
{{ range . }}* {{ . }}
|
||||
{{ end }}{{ end }}
|
||||
**Full Changelog**: https://github.com/kubernetes/ingress-nginx/compare/helm-chart-{{ .PreviousHelmChartVersion }}...helm-chart-{{ .NewHelmChartVersion }}
|
||||
@@ -0,0 +1,13 @@
|
||||
# Changelog
|
||||
|
||||
This file documents all notable changes to [ingress-nginx](https://github.com/kubernetes/ingress-nginx) Helm Chart. The release numbering uses [semantic versioning](http://semver.org).
|
||||
|
||||
### 4.5.2
|
||||
|
||||
* add lint on chart before release (#9570)
|
||||
* ci: remove setup-helm step (#9404)
|
||||
* feat(helm): Optionally use cert-manager instead admission patch (#9279)
|
||||
* run helm release on main only and when the chart/value changes only (#9290)
|
||||
* Update Ingress-Nginx version controller-v1.6.4
|
||||
|
||||
**Full Changelog**: https://github.com/kubernetes/ingress-nginx/compare/helm-chart-4.4.3...helm-chart-4.5.2
|
||||
@@ -0,0 +1,24 @@
|
||||
# Changelog
|
||||
|
||||
This file documents all notable changes to [ingress-nginx](https://github.com/kubernetes/ingress-nginx) Helm Chart. The release numbering uses [semantic versioning](http://semver.org).
|
||||
|
||||
### 4.5.3
|
||||
|
||||
* docs(helm): fix value key in readme for enabling certManager (#9640)
|
||||
* Upgrade alpine 3.17.2
|
||||
* Upgrade golang 1.20
|
||||
* Drop testing/support for Kubernetes 1.23
|
||||
* docs(helm): fix value key in readme for enabling certManager (#9640)
|
||||
* Update Ingress-Nginx version controller-v1.7.0
|
||||
* feat: OpenTelemetry module integration (#9062)
|
||||
* canary-weight-total annotation ignored in rule backends (#9729)
|
||||
* fix controller psp's volume config (#9740)
|
||||
* Fix several Helm YAML issues with extraModules and extraInitContainers (#9709)
|
||||
* Chart: Drop `controller.headers`, rework DH param secret. (#9659)
|
||||
* Deployment/DaemonSet: Label pods using `ingress-nginx.labels`. (#9732)
|
||||
* HPA: autoscaling/v2beta1 deprecated, bump apiVersion to v2 for defaultBackend (#9731)
|
||||
* Fix incorrect annotation name in upstream hashing configuration (#9617)
|
||||
|
||||
* Update Ingress-Nginx version controller-v1.7.0
|
||||
|
||||
**Full Changelog**: https://github.com/kubernetes/ingress-nginx/compare/helm-chart-4.5.2...helm-chart-4.6.0
|
||||
@@ -0,0 +1,11 @@
|
||||
# Changelog
|
||||
|
||||
This file documents all notable changes to [ingress-nginx](https://github.com/kubernetes/ingress-nginx) Helm Chart. The release numbering uses [semantic versioning](http://semver.org).
|
||||
|
||||
### 4.6.1
|
||||
|
||||
* [helm] Support custom port configuration for internal service (#9846)
|
||||
* Adding resource type to default HPA configuration to resolve issues with Terraform helm chart usage (#9803)
|
||||
* Update Ingress-Nginx version controller-v1.7.1
|
||||
|
||||
**Full Changelog**: https://github.com/kubernetes/ingress-nginx/compare/helm-chart-4.6.0...helm-chart-4.6.1
|
||||
@@ -0,0 +1,14 @@
|
||||
# Changelog
|
||||
|
||||
This file documents all notable changes to [ingress-nginx](https://github.com/kubernetes/ingress-nginx) Helm Chart. The release numbering uses [semantic versioning](http://semver.org).
|
||||
|
||||
### 4.7.0
|
||||
|
||||
* helm: Fix opentelemetry module installation for daemonset (#9792)
|
||||
* Update charts/* to keep project name display aligned (#9931)
|
||||
* HPA: Use capabilites & align manifests. (#9521)
|
||||
* PodDisruptionBudget spec logic update (#9904)
|
||||
* add option for annotations in PodDisruptionBudget (#9843)
|
||||
* Update Ingress-Nginx version controller-v1.8.0
|
||||
|
||||
**Full Changelog**: https://github.com/kubernetes/ingress-nginx/compare/helm-chart-4.6.1...helm-chart-4.7.0
|
||||
@@ -0,0 +1,12 @@
|
||||
# Changelog
|
||||
|
||||
This file documents all notable changes to [ingress-nginx](https://github.com/kubernetes/ingress-nginx) Helm Chart. The release numbering uses [semantic versioning](http://semver.org).
|
||||
|
||||
### 4.7.1
|
||||
|
||||
* Added a doc line to the missing helm value service.internal.loadBalancerIP (#9406)
|
||||
* feat(helm): Add loadBalancerClass (#9562)
|
||||
* added helmshowvalues example (#10019)
|
||||
* Update Ingress-Nginx version controller-v1.8.1
|
||||
|
||||
**Full Changelog**: https://github.com/kubernetes/ingress-nginx/compare/helm-chart-4.7.0...helm-chart-4.7.1
|
||||
@@ -0,0 +1,9 @@
|
||||
# Changelog
|
||||
|
||||
This file documents all notable changes to [ingress-nginx](https://github.com/kubernetes/ingress-nginx) Helm Chart. The release numbering uses [semantic versioning](http://semver.org).
|
||||
|
||||
### 4.7.2
|
||||
|
||||
* Update Ingress-Nginx version controller-v1.8.2
|
||||
|
||||
**Full Changelog**: https://github.com/kubernetes/ingress-nginx/compare/helm-chart-4.7.1...helm-chart-4.7.2
|
||||
@@ -0,0 +1,13 @@
|
||||
# Changelog
|
||||
|
||||
This file documents all notable changes to [ingress-nginx](https://github.com/kubernetes/ingress-nginx) Helm Chart. The release numbering uses [semantic versioning](http://semver.org).
|
||||
|
||||
### 4.8.0-beta.0
|
||||
|
||||
* ci(helm): fix Helm Chart release action 422 error (#10237)
|
||||
* helm: Use .Release.Namespace as default for ServiceMonitor namespace (#10249)
|
||||
* [helm] configure allow to configure hostAliases (#10180)
|
||||
* [helm] pass service annotations through helm tpl engine (#10084)
|
||||
* Update Ingress-Nginx version controller-v1.9.0-beta.0
|
||||
|
||||
**Full Changelog**: https://github.com/kubernetes/ingress-nginx/compare/helm-chart-4.7.2...helm-chart-4.8.0-beta.0
|
||||
@@ -0,0 +1,13 @@
|
||||
# Changelog
|
||||
|
||||
This file documents all notable changes to [ingress-nginx](https://github.com/kubernetes/ingress-nginx) Helm Chart. The release numbering uses [semantic versioning](http://semver.org).
|
||||
|
||||
### 4.8.0
|
||||
|
||||
* ci(helm): fix Helm Chart release action 422 error (#10237)
|
||||
* helm: Use .Release.Namespace as default for ServiceMonitor namespace (#10249)
|
||||
* [helm] configure allow to configure hostAliases (#10180)
|
||||
* [helm] pass service annotations through helm tpl engine (#10084)
|
||||
* Update Ingress-Nginx version controller-v1.9.0
|
||||
|
||||
**Full Changelog**: https://github.com/kubernetes/ingress-nginx/compare/helm-chart-4.7.2...helm-chart-4.8.0
|
||||
@@ -0,0 +1,9 @@
|
||||
# Changelog
|
||||
|
||||
This file documents all notable changes to [ingress-nginx](https://github.com/kubernetes/ingress-nginx) Helm Chart. The release numbering uses [semantic versioning](http://semver.org).
|
||||
|
||||
### 4.8.1
|
||||
|
||||
* Update Ingress-Nginx version controller-v1.9.1
|
||||
|
||||
**Full Changelog**: https://github.com/kubernetes/ingress-nginx/compare/helm-chart-4.8.0...helm-chart-4.8.1
|
||||
@@ -0,0 +1,10 @@
|
||||
# Changelog
|
||||
|
||||
This file documents all notable changes to [ingress-nginx](https://github.com/kubernetes/ingress-nginx) Helm Chart. The release numbering uses [semantic versioning](http://semver.org).
|
||||
|
||||
### 4.8.2
|
||||
|
||||
* - "update nginx base, httpbun, e2e, helm webhook cert gen (#10506)"
|
||||
* - "Update Ingress-Nginx version controller-v1.9.3"
|
||||
|
||||
**Full Changelog**: https://github.com/kubernetes/ingress-nginx/compare/helm-chart-4.8.1...helm-chart-4.8.2
|
||||
@@ -0,0 +1,8 @@
|
||||
# Changelog
|
||||
|
||||
This file documents all notable changes to [ingress-nginx](https://github.com/kubernetes/ingress-nginx) Helm Chart. The release numbering uses [semantic versioning](http://semver.org).
|
||||
|
||||
### 4.8.3
|
||||
* Update Ingress-Nginx version controller-v1.9.4
|
||||
|
||||
**Full Changelog**: https://github.com/kubernetes/ingress-nginx/compare/helm-chart-4.8.2...helm-chart-4.8.3
|
||||
@@ -0,0 +1,6 @@
|
||||
controller:
|
||||
admissionWebhooks:
|
||||
certManager:
|
||||
enabled: true
|
||||
service:
|
||||
type: ClusterIP
|
||||
@@ -0,0 +1,8 @@
|
||||
controller:
|
||||
service:
|
||||
type: ClusterIP
|
||||
containerSecurityContext:
|
||||
allowPrivilegeEscalation: false
|
||||
extraModules:
|
||||
- name: opentelemetry
|
||||
image: busybox
|
||||
@@ -0,0 +1,8 @@
|
||||
controller:
|
||||
service:
|
||||
type: ClusterIP
|
||||
extraModules:
|
||||
- name: opentelemetry
|
||||
image: busybox
|
||||
containerSecurityContext:
|
||||
allowPrivilegeEscalation: false
|
||||
@@ -7,3 +7,9 @@ controller:
|
||||
enabled: true
|
||||
annotations:
|
||||
service.beta.kubernetes.io/aws-load-balancer-internal: "true"
|
||||
ports:
|
||||
http: 443
|
||||
https: 80
|
||||
targetPorts:
|
||||
http: 443
|
||||
https: 80
|
||||
|
||||
@@ -0,0 +1,12 @@
|
||||
controller:
|
||||
service:
|
||||
type: ClusterIP
|
||||
admissionWebhooks:
|
||||
enabled: true
|
||||
extraEnvs:
|
||||
- name: FOO
|
||||
value: foo
|
||||
- name: TEST
|
||||
value: test
|
||||
patch:
|
||||
enabled: true
|
||||
@@ -109,7 +109,7 @@ spec:
|
||||
configmap:
|
||||
type: array
|
||||
items:
|
||||
type: string
|
||||
type: string
|
||||
openapi-schema-validation:
|
||||
type: object
|
||||
properties:
|
||||
|
||||
@@ -1,40 +1,40 @@
|
||||
apiVersion: apiextensions.k8s.io/v1
|
||||
kind: CustomResourceDefinition
|
||||
metadata :
|
||||
name : sourcesidentifiers.openappsec.io
|
||||
|
||||
spec:
|
||||
group: openappsec.io
|
||||
versions:
|
||||
- name: v1beta1
|
||||
served: true
|
||||
storage: true
|
||||
schema:
|
||||
openAPIV3Schema:
|
||||
type: object
|
||||
properties:
|
||||
spec:
|
||||
type: array
|
||||
items:
|
||||
type: object
|
||||
properties:
|
||||
sourceIdentifier:
|
||||
type: string
|
||||
enum:
|
||||
- headerkey
|
||||
- JWTKey
|
||||
- cookie
|
||||
- sourceip
|
||||
- x-forwarded-for
|
||||
value:
|
||||
type: array
|
||||
items:
|
||||
type: string
|
||||
|
||||
scope: Cluster
|
||||
names:
|
||||
plural: sourcesidentifiers
|
||||
singular: sourcesidentifier
|
||||
kind: SourcesIdentifier
|
||||
shortNames:
|
||||
- sourcesidentifier
|
||||
apiVersion: apiextensions.k8s.io/v1
|
||||
kind: CustomResourceDefinition
|
||||
metadata :
|
||||
name : sourcesidentifiers.openappsec.io
|
||||
|
||||
spec:
|
||||
group: openappsec.io
|
||||
versions:
|
||||
- name: v1beta1
|
||||
served: true
|
||||
storage: true
|
||||
schema:
|
||||
openAPIV3Schema:
|
||||
type: object
|
||||
properties:
|
||||
spec:
|
||||
type: array
|
||||
items:
|
||||
type: object
|
||||
properties:
|
||||
sourceIdentifier:
|
||||
type: string
|
||||
enum:
|
||||
- headerkey
|
||||
- JWTKey
|
||||
- cookie
|
||||
- sourceip
|
||||
- x-forwarded-for
|
||||
value:
|
||||
type: array
|
||||
items:
|
||||
type: string
|
||||
|
||||
scope: Cluster
|
||||
names:
|
||||
plural: sourcesidentifiers
|
||||
singular: sourcesidentifier
|
||||
kind: SourcesIdentifier
|
||||
shortNames:
|
||||
- sourcesidentifier
|
||||
|
||||
@@ -1,32 +1,32 @@
|
||||
apiVersion: apiextensions.k8s.io/v1
|
||||
kind: CustomResourceDefinition
|
||||
metadata :
|
||||
name : trustedsources.openappsec.io
|
||||
|
||||
spec:
|
||||
group: openappsec.io
|
||||
versions:
|
||||
- name: v1beta1
|
||||
served: true
|
||||
storage: true
|
||||
schema:
|
||||
openAPIV3Schema:
|
||||
type: object
|
||||
properties:
|
||||
spec:
|
||||
type: object
|
||||
properties:
|
||||
minNumOfSources:
|
||||
type: integer
|
||||
sourcesIdentifiers:
|
||||
type: array
|
||||
items:
|
||||
type: string
|
||||
|
||||
scope: Cluster
|
||||
names:
|
||||
plural: trustedsources
|
||||
singular: trustedsource
|
||||
kind: TrustedSource
|
||||
shortNames:
|
||||
- trustedsource
|
||||
apiVersion: apiextensions.k8s.io/v1
|
||||
kind: CustomResourceDefinition
|
||||
metadata :
|
||||
name : trustedsources.openappsec.io
|
||||
|
||||
spec:
|
||||
group: openappsec.io
|
||||
versions:
|
||||
- name: v1beta1
|
||||
served: true
|
||||
storage: true
|
||||
schema:
|
||||
openAPIV3Schema:
|
||||
type: object
|
||||
properties:
|
||||
spec:
|
||||
type: object
|
||||
properties:
|
||||
minNumOfSources:
|
||||
type: integer
|
||||
sourcesIdentifiers:
|
||||
type: array
|
||||
items:
|
||||
type: string
|
||||
|
||||
scope: Cluster
|
||||
names:
|
||||
plural: trustedsources
|
||||
singular: trustedsource
|
||||
kind: TrustedSource
|
||||
shortNames:
|
||||
- trustedsource
|
||||
|
||||
@@ -30,6 +30,17 @@ We truncate at 63 chars because some Kubernetes name fields are limited to this
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Allow the release namespace to be overridden for multi-namespace deployments in combined charts
|
||||
*/}}
|
||||
{{- define "ingress-nginx.namespace" -}}
|
||||
{{- if .Values.namespaceOverride -}}
|
||||
{{- .Values.namespaceOverride | trunc 63 | trimSuffix "-" -}}
|
||||
{{- else -}}
|
||||
{{- .Release.Namespace -}}
|
||||
{{- end -}}
|
||||
{{- end -}}
|
||||
|
||||
|
||||
{{/*
|
||||
Container SecurityContext.
|
||||
@@ -85,6 +96,16 @@ We truncate at 63 chars because some Kubernetes name fields are limited to this
|
||||
{{- printf "%s-%s" (include "ingress-nginx.fullname" .) .Values.controller.name | trunc 63 | trimSuffix "-" -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Construct a unique electionID.
|
||||
Users can provide an override for an explicit electionID if they want via `.Values.controller.electionID`
|
||||
*/}}
|
||||
{{- define "ingress-nginx.controller.electionID" -}}
|
||||
{{- $defElectionID := printf "%s-leader" (include "ingress-nginx.fullname" .) -}}
|
||||
{{- $electionID := default $defElectionID .Values.controller.electionID -}}
|
||||
{{- print $electionID -}}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Construct the path for the publish-service.
|
||||
|
||||
@@ -183,3 +204,25 @@ IngressClass parameters.
|
||||
{{ toYaml .Values.controller.ingressClassResource.parameters | indent 4}}
|
||||
{{ end }}
|
||||
{{- end -}}
|
||||
|
||||
{{/*
|
||||
Extra modules.
|
||||
*/}}
|
||||
{{- define "extraModules" -}}
|
||||
- name: {{ .name }}
|
||||
image: {{ .image }}
|
||||
{{- if .distroless | default false }}
|
||||
command: ['/init_module']
|
||||
{{- else }}
|
||||
command: ['sh', '-c', '/usr/local/bin/init_module.sh']
|
||||
{{- end }}
|
||||
{{- if .containerSecurityContext }}
|
||||
securityContext: {{ .containerSecurityContext | toYaml | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- if .resources }}
|
||||
resources: {{ .resources | toYaml | nindent 4 }}
|
||||
{{- end }}
|
||||
volumeMounts:
|
||||
- name: {{ toYaml "modules"}}
|
||||
mountPath: {{ toYaml "/modules_mount"}}
|
||||
{{- end -}}
|
||||
|
||||
@@ -1,5 +1,8 @@
|
||||
{{- define "ingress-nginx.params" -}}
|
||||
- /nginx-ingress-controller
|
||||
{{- if .Values.controller.enableAnnotationValidations }}
|
||||
- --enable-annotation-validation=true
|
||||
{{- end }}
|
||||
{{- if .Values.defaultBackend.enabled }}
|
||||
- --default-backend-service=$(POD_NAMESPACE)/{{ include "ingress-nginx.defaultBackend.fullname" . }}
|
||||
{{- end }}
|
||||
@@ -10,7 +13,7 @@
|
||||
- --publish-service={{ template "ingress-nginx.controller.publishServicePath" . }}-internal
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
- --election-id={{ .Values.controller.electionID }}
|
||||
- --election-id={{ include "ingress-nginx.controller.electionID" . }}
|
||||
- --controller-class={{ .Values.controller.ingressClassResource.controllerValue }}
|
||||
{{- if .Values.controller.ingressClass }}
|
||||
- --ingress-class={{ .Values.controller.ingressClass }}
|
||||
@@ -51,6 +54,9 @@
|
||||
{{- if .Values.controller.watchIngressWithoutClass }}
|
||||
- --watch-ingress-without-class=true
|
||||
{{- end }}
|
||||
{{- if .Values.controller.enableTopologyAwareRouting }}
|
||||
- --enable-topology-aware-routing=true
|
||||
{{- end }}
|
||||
{{- range $key, $value := .Values.controller.extraArgs }}
|
||||
{{- /* Accept keys without values or with false as value */}}
|
||||
{{- if eq ($value | quote | len) 2 }}
|
||||
|
||||
@@ -0,0 +1,63 @@
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.certManager.enabled -}}
|
||||
{{- if not .Values.controller.admissionWebhooks.certManager.issuerRef -}}
|
||||
# Create a selfsigned Issuer, in order to create a root CA certificate for
|
||||
# signing webhook serving certificates
|
||||
apiVersion: cert-manager.io/v1
|
||||
kind: Issuer
|
||||
metadata:
|
||||
name: {{ include "ingress-nginx.fullname" . }}-self-signed-issuer
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
spec:
|
||||
selfSigned: {}
|
||||
---
|
||||
# Generate a CA Certificate used to sign certificates for the webhook
|
||||
apiVersion: cert-manager.io/v1
|
||||
kind: Certificate
|
||||
metadata:
|
||||
name: {{ include "ingress-nginx.fullname" . }}-root-cert
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
spec:
|
||||
secretName: {{ include "ingress-nginx.fullname" . }}-root-cert
|
||||
duration: {{ .Values.controller.admissionWebhooks.certManager.rootCert.duration | default "43800h0m0s" | quote }}
|
||||
issuerRef:
|
||||
name: {{ include "ingress-nginx.fullname" . }}-self-signed-issuer
|
||||
commonName: "ca.webhook.ingress-nginx"
|
||||
isCA: true
|
||||
subject:
|
||||
organizations:
|
||||
- ingress-nginx
|
||||
---
|
||||
# Create an Issuer that uses the above generated CA certificate to issue certs
|
||||
apiVersion: cert-manager.io/v1
|
||||
kind: Issuer
|
||||
metadata:
|
||||
name: {{ include "ingress-nginx.fullname" . }}-root-issuer
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
spec:
|
||||
ca:
|
||||
secretName: {{ include "ingress-nginx.fullname" . }}-root-cert
|
||||
{{- end }}
|
||||
---
|
||||
# generate a server certificate for the apiservices to use
|
||||
apiVersion: cert-manager.io/v1
|
||||
kind: Certificate
|
||||
metadata:
|
||||
name: {{ include "ingress-nginx.fullname" . }}-admission
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
spec:
|
||||
secretName: {{ include "ingress-nginx.fullname" . }}-admission
|
||||
duration: {{ .Values.controller.admissionWebhooks.certManager.admissionCert.duration | default "8760h0m0s" | quote }}
|
||||
issuerRef:
|
||||
{{- if .Values.controller.admissionWebhooks.certManager.issuerRef }}
|
||||
{{- toYaml .Values.controller.admissionWebhooks.certManager.issuerRef | nindent 4 }}
|
||||
{{- else }}
|
||||
name: {{ include "ingress-nginx.fullname" . }}-root-issuer
|
||||
{{- end }}
|
||||
dnsNames:
|
||||
- {{ include "ingress-nginx.controller.fullname" . }}-admission
|
||||
- {{ include "ingress-nginx.controller.fullname" . }}-admission.{{ include "ingress-nginx.namespace" . }}
|
||||
- {{ include "ingress-nginx.controller.fullname" . }}-admission.{{ include "ingress-nginx.namespace" . }}.svc
|
||||
subject:
|
||||
organizations:
|
||||
- ingress-nginx-admission
|
||||
{{- end -}}
|
||||
@@ -1,4 +1,4 @@
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled -}}
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled (not .Values.controller.admissionWebhooks.certManager.enabled) -}}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: ClusterRole
|
||||
metadata:
|
||||
|
||||
@@ -1,8 +1,8 @@
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled -}}
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled (not .Values.controller.admissionWebhooks.certManager.enabled) -}}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: ClusterRoleBinding
|
||||
metadata:
|
||||
name: {{ include "ingress-nginx.fullname" . }}-admission
|
||||
name: {{ include "ingress-nginx.fullname" . }}-admission
|
||||
annotations:
|
||||
"helm.sh/hook": pre-install,pre-upgrade,post-install,post-upgrade
|
||||
"helm.sh/hook-delete-policy": before-hook-creation,hook-succeeded
|
||||
@@ -19,5 +19,5 @@ roleRef:
|
||||
subjects:
|
||||
- kind: ServiceAccount
|
||||
name: {{ include "ingress-nginx.fullname" . }}-admission
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
namespace: {{ (include "ingress-nginx.namespace" .) | quote }}
|
||||
{{- end }}
|
||||
|
||||
@@ -1,9 +1,9 @@
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled -}}
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled (not .Values.controller.admissionWebhooks.certManager.enabled) -}}
|
||||
apiVersion: batch/v1
|
||||
kind: Job
|
||||
metadata:
|
||||
name: {{ include "ingress-nginx.fullname" . }}-admission-create
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
annotations:
|
||||
"helm.sh/hook": pre-install,pre-upgrade
|
||||
"helm.sh/hook-delete-policy": before-hook-creation,hook-succeeded
|
||||
@@ -56,8 +56,12 @@ spec:
|
||||
valueFrom:
|
||||
fieldRef:
|
||||
fieldPath: metadata.namespace
|
||||
securityContext:
|
||||
allowPrivilegeEscalation: false
|
||||
{{- if .Values.controller.admissionWebhooks.extraEnvs }}
|
||||
{{- toYaml .Values.controller.admissionWebhooks.extraEnvs | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.admissionWebhooks.createSecretJob.securityContext }}
|
||||
securityContext: {{ toYaml .Values.controller.admissionWebhooks.createSecretJob.securityContext | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.admissionWebhooks.createSecretJob.resources }}
|
||||
resources: {{ toYaml .Values.controller.admissionWebhooks.createSecretJob.resources | nindent 12 }}
|
||||
{{- end }}
|
||||
@@ -69,8 +73,8 @@ spec:
|
||||
{{- if .Values.controller.admissionWebhooks.patch.tolerations }}
|
||||
tolerations: {{ toYaml .Values.controller.admissionWebhooks.patch.tolerations | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.admissionWebhooks.patch.securityContext }}
|
||||
securityContext:
|
||||
runAsNonRoot: true
|
||||
runAsUser: {{ .Values.controller.admissionWebhooks.patch.runAsUser }}
|
||||
fsGroup: {{ .Values.controller.admissionWebhooks.patch.fsGroup }}
|
||||
{{- toYaml .Values.controller.admissionWebhooks.patch.securityContext | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
@@ -1,9 +1,9 @@
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled -}}
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled (not .Values.controller.admissionWebhooks.certManager.enabled) -}}
|
||||
apiVersion: batch/v1
|
||||
kind: Job
|
||||
metadata:
|
||||
name: {{ include "ingress-nginx.fullname" . }}-admission-patch
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
annotations:
|
||||
"helm.sh/hook": post-install,post-upgrade
|
||||
"helm.sh/hook-delete-policy": before-hook-creation,hook-succeeded
|
||||
@@ -58,8 +58,12 @@ spec:
|
||||
valueFrom:
|
||||
fieldRef:
|
||||
fieldPath: metadata.namespace
|
||||
securityContext:
|
||||
allowPrivilegeEscalation: false
|
||||
{{- if .Values.controller.admissionWebhooks.extraEnvs }}
|
||||
{{- toYaml .Values.controller.admissionWebhooks.extraEnvs | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.admissionWebhooks.patchWebhookJob.securityContext }}
|
||||
securityContext: {{ toYaml .Values.controller.admissionWebhooks.patchWebhookJob.securityContext | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.admissionWebhooks.patchWebhookJob.resources }}
|
||||
resources: {{ toYaml .Values.controller.admissionWebhooks.patchWebhookJob.resources | nindent 12 }}
|
||||
{{- end }}
|
||||
@@ -71,8 +75,8 @@ spec:
|
||||
{{- if .Values.controller.admissionWebhooks.patch.tolerations }}
|
||||
tolerations: {{ toYaml .Values.controller.admissionWebhooks.patch.tolerations | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.admissionWebhooks.patch.securityContext }}
|
||||
securityContext:
|
||||
runAsNonRoot: true
|
||||
runAsUser: {{ .Values.controller.admissionWebhooks.patch.runAsUser }}
|
||||
fsGroup: {{ .Values.controller.admissionWebhooks.patch.fsGroup }}
|
||||
{{- toYaml .Values.controller.admissionWebhooks.patch.securityContext | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
@@ -0,0 +1,26 @@
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled (not .Values.controller.admissionWebhooks.certManager.enabled) -}}
|
||||
apiVersion: networking.k8s.io/v1
|
||||
kind: NetworkPolicy
|
||||
metadata:
|
||||
name: {{ include "ingress-nginx.fullname" . }}-admission
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
annotations:
|
||||
"helm.sh/hook": pre-install,pre-upgrade,post-install,post-upgrade
|
||||
"helm.sh/hook-delete-policy": before-hook-creation,hook-succeeded
|
||||
labels:
|
||||
{{- include "ingress-nginx.labels" . | nindent 4 }}
|
||||
app.kubernetes.io/component: admission-webhook
|
||||
{{- with .Values.controller.admissionWebhooks.patch.labels }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
podSelector:
|
||||
matchLabels:
|
||||
{{- include "ingress-nginx.selectorLabels" . | nindent 6 }}
|
||||
app.kubernetes.io/component: admission-webhook
|
||||
policyTypes:
|
||||
- Ingress
|
||||
- Egress
|
||||
egress:
|
||||
- {}
|
||||
{{- end }}
|
||||
@@ -1,3 +1,4 @@
|
||||
{{- if (semverCompare "<1.25.0-0" .Capabilities.KubeVersion.Version) }}
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled .Values.podSecurityPolicy.enabled (empty .Values.controller.admissionWebhooks.existingPsp) -}}
|
||||
apiVersion: policy/v1beta1
|
||||
kind: PodSecurityPolicy
|
||||
@@ -37,3 +38,4 @@ spec:
|
||||
- secret
|
||||
- downwardAPI
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
@@ -1,9 +1,9 @@
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled -}}
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled (not .Values.controller.admissionWebhooks.certManager.enabled) -}}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: Role
|
||||
metadata:
|
||||
name: {{ include "ingress-nginx.fullname" . }}-admission
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
annotations:
|
||||
"helm.sh/hook": pre-install,pre-upgrade,post-install,post-upgrade
|
||||
"helm.sh/hook-delete-policy": before-hook-creation,hook-succeeded
|
||||
|
||||
@@ -1,9 +1,9 @@
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled -}}
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled (not .Values.controller.admissionWebhooks.certManager.enabled) -}}
|
||||
apiVersion: rbac.authorization.k8s.io/v1
|
||||
kind: RoleBinding
|
||||
metadata:
|
||||
name: {{ include "ingress-nginx.fullname" . }}-admission
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
annotations:
|
||||
"helm.sh/hook": pre-install,pre-upgrade,post-install,post-upgrade
|
||||
"helm.sh/hook-delete-policy": before-hook-creation,hook-succeeded
|
||||
@@ -20,5 +20,5 @@ roleRef:
|
||||
subjects:
|
||||
- kind: ServiceAccount
|
||||
name: {{ include "ingress-nginx.fullname" . }}-admission
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
namespace: {{ (include "ingress-nginx.namespace" .) | quote }}
|
||||
{{- end }}
|
||||
|
||||
@@ -1,9 +1,9 @@
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled -}}
|
||||
{{- if and .Values.controller.admissionWebhooks.enabled .Values.controller.admissionWebhooks.patch.enabled (not .Values.controller.admissionWebhooks.certManager.enabled) -}}
|
||||
apiVersion: v1
|
||||
kind: ServiceAccount
|
||||
metadata:
|
||||
name: {{ include "ingress-nginx.fullname" . }}-admission
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
annotations:
|
||||
"helm.sh/hook": pre-install,pre-upgrade,post-install,post-upgrade
|
||||
"helm.sh/hook-delete-policy": before-hook-creation,hook-succeeded
|
||||
|
||||
@@ -4,8 +4,13 @@
|
||||
apiVersion: admissionregistration.k8s.io/v1
|
||||
kind: ValidatingWebhookConfiguration
|
||||
metadata:
|
||||
annotations:
|
||||
{{- if .Values.controller.admissionWebhooks.certManager.enabled }}
|
||||
certmanager.k8s.io/inject-ca-from: {{ printf "%s/%s-admission" .Release.Namespace (include "ingress-nginx.fullname" .) | quote }}
|
||||
cert-manager.io/inject-ca-from: {{ printf "%s/%s-admission" .Release.Namespace (include "ingress-nginx.fullname" .) | quote }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.admissionWebhooks.annotations }}
|
||||
annotations: {{ toYaml .Values.controller.admissionWebhooks.annotations | nindent 4 }}
|
||||
{{- toYaml .Values.controller.admissionWebhooks.annotations | nindent 4 }}
|
||||
{{- end }}
|
||||
labels:
|
||||
{{- include "ingress-nginx.labels" . | nindent 4 }}
|
||||
@@ -33,7 +38,7 @@ webhooks:
|
||||
- v1
|
||||
clientConfig:
|
||||
service:
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
namespace: {{ (include "ingress-nginx.namespace" .) | quote }}
|
||||
name: {{ include "ingress-nginx.controller.fullname" . }}-admission
|
||||
path: /networking/v1/ingresses
|
||||
{{- if .Values.controller.admissionWebhooks.timeoutSeconds }}
|
||||
|
||||
@@ -1,4 +1,5 @@
|
||||
{{- if and (eq "stand-alone" .Values.appsec.mode) (eq .Values.appsec.persistence.enabled true) -}}
|
||||
{{- if not (eq .Values.kind "Vanilla") -}}
|
||||
{{- if and (eq "standalone" .Values.appsec.mode) (eq .Values.appsec.persistence.enabled true) -}}
|
||||
kind: PersistentVolumeClaim
|
||||
apiVersion: v1
|
||||
metadata:
|
||||
@@ -17,4 +18,5 @@ spec:
|
||||
{{- else }}
|
||||
storageClassName: {{ required "A storage class for learning data is required" .Values.appsec.persistence.learning.storageClass.name }}
|
||||
{{- end -}}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
@@ -1,4 +1,4 @@
|
||||
{{- if (eq .Values.controller.kind "Deployment") -}}
|
||||
{{- if (and (eq .Values.kind "AppSec") .Values.appsec.persistence.enabled) }}
|
||||
kind: PersistentVolumeClaim
|
||||
apiVersion: v1
|
||||
metadata:
|
||||
|
||||
@@ -0,0 +1,32 @@
|
||||
{{- if not (eq .Values.kind "Vanilla") -}}
|
||||
{{- if .Values.appsec.configMapContent }}
|
||||
apiVersion: v1
|
||||
kind: ConfigMap
|
||||
metadata:
|
||||
name: {{ .Values.appsec.configMapName | default "appsec-settings-configmap" | quote }}
|
||||
data:
|
||||
{{- if .Values.appsec.configMapContent.crowdsec }}
|
||||
CROWDSEC_ENABLED: {{ .Values.appsec.configMapContent.crowdsec.enabled | default "false" | quote }}
|
||||
{{- if .Values.appsec.configMapContent.crowdsec.api }}
|
||||
CROWDSEC_API_URL: {{ .Values.appsec.configMapContent.crowdsec.api.url | default "http://crowdsec-service:8080/v1/decisions/stream" }}
|
||||
{{- else }}
|
||||
CROWDSEC_API_URL: "http://crowdsec-service:8080/v1/decisions/stream"
|
||||
{{- end }}
|
||||
{{- if .Values.appsec.configMapContent.crowdsec.auth }}
|
||||
CROWDSEC_AUTH_METHOD: {{ .Values.appsec.configMapContent.crowdsec.auth.method | default "apikey" }}
|
||||
{{- else }}
|
||||
CROWDSEC_AUTH_METHOD: "apikey"
|
||||
{{- end }}
|
||||
{{- if .Values.appsec.configMapContent.crowdsec.mode }}
|
||||
CROWDSEC_MODE: {{ .Values.appsec.configMapContent.crowdsec.mode | default "prevent" }}
|
||||
{{- else }}
|
||||
CROWDSEC_MODE: "prevent"
|
||||
{{- end }}
|
||||
{{- if .Values.appsec.configMapContent.crowdsec.logging }}
|
||||
CROWDSEC_LOGGING: {{ .Values.appsec.configMapContent.crowdsec.logging | default "enabled" }}
|
||||
{{- else }}
|
||||
CROWDSEC_LOGGING: "enabled"
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
@@ -0,0 +1,12 @@
|
||||
{{- if not (eq .Values.kind "Vanilla") -}}
|
||||
{{ if .Values.appsec.secretContent }}
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: {{ .Values.appsec.secretName | default "appsec-settings-secret" | quote }}
|
||||
data:
|
||||
{{- if and .Values.appsec.secretContent.crowdsec .Values.appsec.secretContent.crowdsec.auth }}
|
||||
CROWDSEC_AUTH_DATA: {{ .Values.appsec.secretContent.crowdsec.auth.data | b64enc }}
|
||||
{{- end }}
|
||||
{{ end }}
|
||||
{{ end }}
|
||||
@@ -1,6 +1,15 @@
|
||||
{{- if or (eq .Values.controller.kind "StatefulSet") (eq .Values.controller.kind "Both") -}}
|
||||
{{- if (not (eq .Values.kind "Vanilla")) }}
|
||||
{{- include "isControllerTagValid" . -}}
|
||||
apiVersion: apps/v1
|
||||
{{- if (eq .Values.kind "AppSec") }}
|
||||
{{- if (eq .Values.controller.kind "DaemonSet") }}
|
||||
kind: DaemonSet
|
||||
{{- else }}
|
||||
kind: Deployment
|
||||
{{- end }}
|
||||
{{- else if eq .Values.kind "AppSecStateful" }}
|
||||
kind: StatefulSet
|
||||
{{- end }}
|
||||
metadata:
|
||||
labels:
|
||||
{{- include "ingress-nginx.labels" . | nindent 4 }}
|
||||
@@ -9,7 +18,7 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.controller.fullname" . }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
{{- if .Values.controller.annotations }}
|
||||
annotations: {{ toYaml .Values.controller.annotations | nindent 4 }}
|
||||
{{- end }}
|
||||
@@ -18,16 +27,25 @@ spec:
|
||||
matchLabels:
|
||||
{{- include "ingress-nginx.selectorLabels" . | nindent 6 }}
|
||||
app.kubernetes.io/component: controller
|
||||
{{- if not .Values.controller.autoscaling.enabled }}
|
||||
{{- if not (or .Values.controller.autoscaling.enabled .Values.controller.keda.enabled) }}
|
||||
{{- if eq .Values.kind "AppSecStateful" }}
|
||||
serviceName: "open-appsec-stateful-set"
|
||||
{{- end }}
|
||||
{{- if or (not (eq .Values.controller.kind "DaemonSet")) (and (eq .Values.kind "AppSecStateful") (eq .Values.controller.kind "DaemonSet")) }}
|
||||
replicas: {{ .Values.controller.replicaCount }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
revisionHistoryLimit: {{ .Values.revisionHistoryLimit }}
|
||||
{{- if .Values.controller.updateStrategy }}
|
||||
strategy:
|
||||
{{ toYaml .Values.controller.updateStrategy | nindent 4 }}
|
||||
{{- if (and (not (eq .Values.kind "AppSecStateful")) (eq .Values.controller.kind "DaemonSet")) }}
|
||||
updateStrategy: {{ toYaml .Values.controller.updateStrategy | nindent 4 }}:
|
||||
{{- else }}
|
||||
strategy: {{ toYaml .Values.controller.updateStrategy | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if (eq .Values.kind "AppSec") }}
|
||||
minReadySeconds: {{ .Values.controller.minReadySeconds }}
|
||||
{{- end }}
|
||||
#minReadySeconds: {{ .Values.controller.minReadySeconds }}
|
||||
template:
|
||||
metadata:
|
||||
{{- if .Values.controller.podAnnotations }}
|
||||
@@ -37,7 +55,7 @@ spec:
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
labels:
|
||||
{{- include "ingress-nginx.selectorLabels" . | nindent 8 }}
|
||||
{{- include "ingress-nginx.labels" . | nindent 8 }}
|
||||
app.kubernetes.io/component: controller
|
||||
{{- with .Values.controller.labels }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
@@ -49,6 +67,9 @@ spec:
|
||||
{{- if .Values.controller.dnsConfig }}
|
||||
dnsConfig: {{ toYaml .Values.controller.dnsConfig | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.hostAliases }}
|
||||
hostAliases: {{ tpl (toYaml .Values.controller.hostAliases) $ | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.hostname }}
|
||||
hostname: {{ toYaml .Values.controller.hostname | nindent 8 }}
|
||||
{{- end }}
|
||||
@@ -79,14 +100,18 @@ spec:
|
||||
- name: {{ .Values.appsec.name }}
|
||||
securityContext:
|
||||
{{ toYaml .Values.appsec.securityContext | nindent 12 }}
|
||||
{{- $tag := .Values.appsec.image.tag }}
|
||||
{{- if .Values.appsec.configMapContent.crowdsec.enabled }}
|
||||
{{- $tag = "crowdsec-1.2314-rc1" }}
|
||||
{{- end }}
|
||||
{{- with .Values.appsec.image }}
|
||||
image: "{{- if .registry }}{{ .registry }}/{{- end }}{{- if .repository }}{{ .repository }}/{{- end }}{{ .image }}{{- if .tag }}:{{ .tag }}{{- end }}{{- if (.digest) -}} @{{.digest}} {{- end }}"
|
||||
{{- end }}
|
||||
command:
|
||||
- {{ .Values.appsec.command }}
|
||||
imagePullPolicy: {{ .Values.appsec.image.pullPolicy }}
|
||||
args:
|
||||
{{- if (eq "stand-alone" .Values.appsec.mode) }}
|
||||
args:
|
||||
{{- if (eq "standalone" .Values.appsec.mode) }}
|
||||
- --hybrid-mode
|
||||
- --token
|
||||
- cp-3fb5c718-5e39-47e6-8d5e-99b4bc5660b74b4b7fc8-5312-451d-a763-aaf7872703c0
|
||||
@@ -101,9 +126,13 @@ spec:
|
||||
{{- if .Values.appsec.proxy }}
|
||||
- --proxy
|
||||
- {{ .Values.appsec.proxy }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
imagePullPolicy: {{ .Values.appsec.image.pullPolicy }}
|
||||
env:
|
||||
- name: user_email
|
||||
value: {{ .Values.appsec.userEmail }}
|
||||
- name: registered_server
|
||||
value: "NGINX Server"
|
||||
{{- if eq .Values.appsec.playground false }}
|
||||
- name: SHARED_STORAGE_HOST
|
||||
value: {{ .Values.appsec.storage.name }}-svc
|
||||
@@ -113,26 +142,35 @@ spec:
|
||||
- name: PLAYGROUND
|
||||
value: "true"
|
||||
{{- end }}
|
||||
envFrom:
|
||||
- configMapRef:
|
||||
name: {{ .Values.appsec.configMapName | default "appsec-settings-configmap" }}
|
||||
- secretRef:
|
||||
name: {{ .Values.appsec.secretName | default "appsec-settings-secret" }}
|
||||
resources:
|
||||
{{ toYaml .Values.resources | nindent 12 }}
|
||||
volumeMounts:
|
||||
- name: advanced-model
|
||||
mountPath: /advanced-model
|
||||
{{- if .Values.appsec.persistence.enabled }}
|
||||
{{- if (eq .Values.appsec.persistence.enabled true) }}
|
||||
- name: appsec-conf
|
||||
mountPath: /etc/cp/conf
|
||||
- name: appsec-data
|
||||
mountPath: /etc/cp/data
|
||||
{{- end }}
|
||||
mountPath: /etc/cp/data
|
||||
{{- end }}
|
||||
- name: {{ .Values.controller.containerName }}
|
||||
{{- with .Values.controller.image }}
|
||||
image: "{{- if .registry }}{{ .registry }}/{{- end }}{{- if .repository }}{{ .repository }}/{{- end }}{{ .image }}{{- if .tag }}:{{ .tag }}{{- end }}{{- if (.digest) -}} @{{.digest}} {{- end }}"
|
||||
{{- $tag := .Values.appsec.nginx.image.tag }}
|
||||
{{- if .Values.appsec.configMapContent.crowdsec.enabled }}
|
||||
{{- $tag = "1.2303.1-rc1-v1.3.0" }}
|
||||
{{- end }}
|
||||
{{- with .Values.appsec.nginx.image }}
|
||||
image: "{{ .repository }}:{{ .tag }}"
|
||||
{{- end }}
|
||||
imagePullPolicy: {{ .Values.controller.image.pullPolicy }}
|
||||
{{- if .Values.controller.lifecycle }}
|
||||
lifecycle: {{ toYaml .Values.controller.lifecycle | nindent 12 }}
|
||||
{{- end }}
|
||||
args:
|
||||
args:
|
||||
{{- include "ingress-nginx.params" . | nindent 12 }}
|
||||
securityContext: {{ include "controller.containerSecurityContext" . | nindent 12 }}
|
||||
env:
|
||||
@@ -150,12 +188,16 @@ spec:
|
||||
{{- end }}
|
||||
{{- if .Values.controller.extraEnvs }}
|
||||
{{- toYaml .Values.controller.extraEnvs | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.startupProbe }}
|
||||
startupProbe: {{ toYaml .Values.controller.startupProbe | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.livenessProbe }}
|
||||
livenessProbe: {{ toYaml .Values.controller.livenessProbe | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.readinessProbe }}
|
||||
readinessProbe: {{ toYaml .Values.controller.readinessProbe | nindent 12 }}
|
||||
{{- end }}
|
||||
ports:
|
||||
{{- range $key, $value := .Values.controller.containerPort }}
|
||||
- name: {{ $key }}
|
||||
@@ -166,7 +208,7 @@ spec:
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.metrics.enabled }}
|
||||
- name: metrics
|
||||
- name: {{ .Values.controller.metrics.portName }}
|
||||
containerPort: {{ .Values.controller.metrics.port }}
|
||||
protocol: TCP
|
||||
{{- end }}
|
||||
@@ -191,11 +233,15 @@ spec:
|
||||
hostPort: {{ $key }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if (or .Values.controller.customTemplate.configMapName .Values.controller.extraVolumeMounts .Values.controller.admissionWebhooks.enabled .Values.controller.extraModules) }}
|
||||
{{- if (or .Values.controller.customTemplate.configMapName .Values.controller.extraVolumeMounts .Values.controller.admissionWebhooks.enabled .Values.controller.extraModules .Values.controller.opentelemetry.enabled) }}
|
||||
volumeMounts:
|
||||
{{- if .Values.controller.extraModules }}
|
||||
{{- if (or .Values.controller.extraModules .Values.controller.opentelemetry.enabled) }}
|
||||
- name: modules
|
||||
{{ if .Values.controller.image.chroot }}
|
||||
mountPath: /chroot/modules_mount
|
||||
{{ else }}
|
||||
mountPath: /modules_mount
|
||||
{{ end }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.customTemplate.configMapName }}
|
||||
- mountPath: /etc/nginx/template
|
||||
@@ -217,21 +263,22 @@ spec:
|
||||
{{- if .Values.controller.extraContainers }}
|
||||
{{ toYaml .Values.controller.extraContainers | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if (or .Values.controller.extraInitContainers .Values.controller.extraModules) }}
|
||||
{{- if (or .Values.controller.extraInitContainers .Values.controller.extraModules .Values.controller.opentelemetry.enabled) }}
|
||||
initContainers:
|
||||
{{- if .Values.controller.extraInitContainers }}
|
||||
{{ toYaml .Values.controller.extraInitContainers | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.extraModules }}
|
||||
{{- range .Values.controller.extraModules }}
|
||||
- name: {{ .name }}
|
||||
image: {{ .image }}
|
||||
command: ['sh', '-c', '/usr/local/bin/init_module.sh']
|
||||
volumeMounts:
|
||||
- name: modules
|
||||
mountPath: /modules_mount
|
||||
{{- $containerSecurityContext := .containerSecurityContext | default $.Values.controller.containerSecurityContext }}
|
||||
{{- include "extraModules" (dict "name" .name "image" .image "containerSecurityContext" $containerSecurityContext) | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.opentelemetry.enabled}}
|
||||
{{- $otelContainerSecurityContext := $.Values.controller.opentelemetry.containerSecurityContext | default $.Values.controller.containerSecurityContext }}
|
||||
{{ $otelResources := $.Values.controller.opentelemetry.resources | default dict }}
|
||||
{{- include "extraModules" (dict "name" "opentelemetry" "image" .Values.controller.opentelemetry.image "containerSecurityContext" $otelContainerSecurityContext "distroless" true "resources" $otelResources) | nindent 8}}
|
||||
{{- end}}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.hostNetwork }}
|
||||
hostNetwork: {{ .Values.controller.hostNetwork }}
|
||||
@@ -246,17 +293,25 @@ spec:
|
||||
affinity: {{ toYaml .Values.controller.affinity | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.topologySpreadConstraints }}
|
||||
topologySpreadConstraints: {{ toYaml .Values.controller.topologySpreadConstraints | nindent 8 }}
|
||||
topologySpreadConstraints: {{ tpl (toYaml .Values.controller.topologySpreadConstraints) $ | nindent 8 }}
|
||||
{{- end }}
|
||||
serviceAccountName: {{ template "ingress-nginx.serviceAccountName" . }}
|
||||
terminationGracePeriodSeconds: {{ .Values.controller.terminationGracePeriodSeconds }}
|
||||
{{- if (or .Values.controller.customTemplate.configMapName .Values.controller.extraVolumeMounts .Values.controller.admissionWebhooks.enabled .Values.controller.extraVolumes .Values.controller.extraModules) }}
|
||||
{{- if (or .Values.controller.customTemplate.configMapName .Values.controller.extraVolumeMounts .Values.controller.admissionWebhooks.enabled .Values.controller.extraVolumes .Values.controller.extraModules .Values.controller.opentelemetry.enabled) }}
|
||||
volumes:
|
||||
- name: advanced-model
|
||||
configMap:
|
||||
name: advanced-model-config
|
||||
optional: true
|
||||
{{- if .Values.controller.extraModules }}
|
||||
{{- if (and (eq .Values.kind "AppSec") .Values.appsec.persistence.enabled) }}
|
||||
- name: appsec-conf
|
||||
persistentVolumeClaim:
|
||||
claimName: {{ .Values.appsec.name }}-conf
|
||||
- name: appsec-data
|
||||
persistentVolumeClaim:
|
||||
claimName: {{ .Values.appsec.name }}-data
|
||||
{{- end }}
|
||||
{{- if (or .Values.controller.extraModules .Values.controller.opentelemetry.enabled)}}
|
||||
- name: modules
|
||||
emptyDir: {}
|
||||
{{- end }}
|
||||
@@ -272,12 +327,19 @@ spec:
|
||||
- name: webhook-cert
|
||||
secret:
|
||||
secretName: {{ include "ingress-nginx.fullname" . }}-admission
|
||||
{{- if .Values.controller.admissionWebhooks.certManager.enabled }}
|
||||
items:
|
||||
- key: tls.crt
|
||||
path: cert
|
||||
- key: tls.key
|
||||
path: key
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.extraVolumes }}
|
||||
{{ toYaml .Values.controller.extraVolumes | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.appsec.persistence.enabled }}
|
||||
{{- if (and (eq .Values.kind "AppSecStateful") .Values.appsec.persistence.enabled) }}
|
||||
volumeClaimTemplates:
|
||||
- metadata:
|
||||
name: appsec-conf
|
||||
@@ -29,6 +29,13 @@ rules:
|
||||
verbs:
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- coordination.k8s.io
|
||||
resources:
|
||||
- leases
|
||||
verbs:
|
||||
- list
|
||||
- watch
|
||||
{{- if and .Values.controller.scope.enabled .Values.controller.scope.namespace }}
|
||||
- apiGroups:
|
||||
- ""
|
||||
@@ -82,6 +89,14 @@ rules:
|
||||
- get
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- discovery.k8s.io
|
||||
resources:
|
||||
- endpointslices
|
||||
verbs:
|
||||
- list
|
||||
- watch
|
||||
- get
|
||||
- apiGroups:
|
||||
- openappsec.io
|
||||
resources:
|
||||
|
||||
@@ -15,5 +15,5 @@ roleRef:
|
||||
subjects:
|
||||
- kind: ServiceAccount
|
||||
name: {{ template "ingress-nginx.serviceAccountName" . }}
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
namespace: {{ (include "ingress-nginx.namespace" .) | quote }}
|
||||
{{- end }}
|
||||
|
||||
@@ -9,6 +9,6 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.fullname" . }}-custom-add-headers
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
data: {{ toYaml .Values.controller.addHeaders | nindent 2 }}
|
||||
{{- end }}
|
||||
|
||||
@@ -1,4 +1,4 @@
|
||||
{{- if or .Values.controller.proxySetHeaders .Values.controller.headers -}}
|
||||
{{- if .Values.controller.proxySetHeaders -}}
|
||||
apiVersion: v1
|
||||
kind: ConfigMap
|
||||
metadata:
|
||||
@@ -9,11 +9,6 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.fullname" . }}-custom-proxy-headers
|
||||
namespace: {{ .Release.Namespace }}
|
||||
data:
|
||||
{{- if .Values.controller.proxySetHeaders }}
|
||||
{{ toYaml .Values.controller.proxySetHeaders | indent 2 }}
|
||||
{{ else if and .Values.controller.headers (not .Values.controller.proxySetHeaders) }}
|
||||
{{ toYaml .Values.controller.headers | indent 2 }}
|
||||
{{- end }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
data: {{ toYaml .Values.controller.proxySetHeaders | nindent 2 }}
|
||||
{{- end }}
|
||||
|
||||
@@ -12,6 +12,6 @@ metadata:
|
||||
annotations: {{ toYaml .Values.controller.tcp.annotations | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.fullname" . }}-tcp
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
data: {{ tpl (toYaml .Values.tcp) . | nindent 2 }}
|
||||
{{- end }}
|
||||
|
||||
@@ -12,6 +12,6 @@ metadata:
|
||||
annotations: {{ toYaml .Values.controller.udp.annotations | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.fullname" . }}-udp
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
data: {{ tpl (toYaml .Values.udp) . | nindent 2 }}
|
||||
{{- end }}
|
||||
|
||||
@@ -11,19 +11,18 @@ metadata:
|
||||
annotations: {{ toYaml .Values.controller.configAnnotations | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.controller.fullname" . }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
data:
|
||||
allow-snippet-annotations: "{{ .Values.controller.allowSnippetAnnotations }}"
|
||||
{{- if .Values.controller.addHeaders }}
|
||||
add-headers: {{ .Release.Namespace }}/{{ include "ingress-nginx.fullname" . }}-custom-add-headers
|
||||
add-headers: {{ include "ingress-nginx.namespace" . }}/{{ include "ingress-nginx.fullname" . }}-custom-add-headers
|
||||
{{- end }}
|
||||
{{- if or .Values.controller.proxySetHeaders .Values.controller.headers }}
|
||||
proxy-set-headers: {{ .Release.Namespace }}/{{ include "ingress-nginx.fullname" . }}-custom-proxy-headers
|
||||
{{- if .Values.controller.proxySetHeaders }}
|
||||
proxy-set-headers: {{ include "ingress-nginx.namespace" . }}/{{ include "ingress-nginx.fullname" . }}-custom-proxy-headers
|
||||
{{- end }}
|
||||
{{- if .Values.dhParam }}
|
||||
ssl-dh-param: {{ printf "%s/%s" .Release.Namespace (include "ingress-nginx.controller.fullname" .) }}
|
||||
ssl-dh-param: {{ include "ingress-nginx.namespace" . }}/{{ include "ingress-nginx.controller.fullname" . }}
|
||||
{{- end }}
|
||||
{{- range $key, $value := .Values.controller.config }}
|
||||
{{- $key | nindent 2 }}: {{ $value | quote }}
|
||||
{{- $key | nindent 2 }}: {{ $value | quote }}
|
||||
{{- end }}
|
||||
|
||||
|
||||
@@ -1,4 +1,4 @@
|
||||
{{- if or (eq .Values.controller.kind "DaemonSet") (eq .Values.controller.kind "Both") -}}
|
||||
{{- if and (eq .Values.kind "Vanilla") (eq .Values.controller.kind "DaemonSet") -}}
|
||||
{{- include "isControllerTagValid" . -}}
|
||||
apiVersion: apps/v1
|
||||
kind: DaemonSet
|
||||
@@ -10,7 +10,7 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.controller.fullname" . }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
{{- if .Values.controller.annotations }}
|
||||
annotations: {{ toYaml .Values.controller.annotations | nindent 4 }}
|
||||
{{- end }}
|
||||
@@ -33,7 +33,7 @@ spec:
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
labels:
|
||||
{{- include "ingress-nginx.selectorLabels" . | nindent 8 }}
|
||||
{{- include "ingress-nginx.labels" . | nindent 8 }}
|
||||
app.kubernetes.io/component: controller
|
||||
{{- with .Values.controller.labels }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
@@ -45,6 +45,9 @@ spec:
|
||||
{{- if .Values.controller.dnsConfig }}
|
||||
dnsConfig: {{ toYaml .Values.controller.dnsConfig | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.hostAliases }}
|
||||
hostAliases: {{ tpl (toYaml .Values.controller.hostAliases) $ | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.hostname }}
|
||||
hostname: {{ toYaml .Values.controller.hostname | nindent 8 }}
|
||||
{{- end }}
|
||||
@@ -53,12 +56,12 @@ spec:
|
||||
imagePullSecrets: {{ toYaml .Values.imagePullSecrets | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.priorityClassName }}
|
||||
priorityClassName: {{ .Values.controller.priorityClassName }}
|
||||
priorityClassName: {{ .Values.controller.priorityClassName | quote }}
|
||||
{{- end }}
|
||||
{{- if or .Values.controller.podSecurityContext .Values.controller.sysctls }}
|
||||
securityContext:
|
||||
{{- end }}
|
||||
{{- if .Values.controller.podSecurityContext }}
|
||||
{{- if .Values.controller.podSecurityContext }}
|
||||
{{- toYaml .Values.controller.podSecurityContext | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.sysctls }}
|
||||
@@ -102,8 +105,12 @@ spec:
|
||||
{{- if .Values.controller.startupProbe }}
|
||||
startupProbe: {{ toYaml .Values.controller.startupProbe | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.livenessProbe }}
|
||||
livenessProbe: {{ toYaml .Values.controller.livenessProbe | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.readinessProbe }}
|
||||
readinessProbe: {{ toYaml .Values.controller.readinessProbe | nindent 12 }}
|
||||
{{- end }}
|
||||
ports:
|
||||
{{- range $key, $value := .Values.controller.containerPort }}
|
||||
- name: {{ $key }}
|
||||
@@ -114,7 +121,7 @@ spec:
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.metrics.enabled }}
|
||||
- name: metrics
|
||||
- name: {{ .Values.controller.metrics.portName }}
|
||||
containerPort: {{ .Values.controller.metrics.port }}
|
||||
protocol: TCP
|
||||
{{- end }}
|
||||
@@ -139,11 +146,15 @@ spec:
|
||||
hostPort: {{ $key }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if (or .Values.controller.customTemplate.configMapName .Values.controller.extraVolumeMounts .Values.controller.admissionWebhooks.enabled .Values.controller.extraModules) }}
|
||||
{{- if (or .Values.controller.customTemplate.configMapName .Values.controller.extraVolumeMounts .Values.controller.admissionWebhooks.enabled .Values.controller.extraModules .Values.controller.opentelemetry.enabled) }}
|
||||
volumeMounts:
|
||||
{{- if .Values.controller.extraModules }}
|
||||
{{- if (or .Values.controller.extraModules .Values.controller.opentelemetry.enabled) }}
|
||||
- name: modules
|
||||
{{ if .Values.controller.image.chroot }}
|
||||
mountPath: /chroot/modules_mount
|
||||
{{ else }}
|
||||
mountPath: /modules_mount
|
||||
{{ end }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.customTemplate.configMapName }}
|
||||
- mountPath: /etc/nginx/template
|
||||
@@ -165,20 +176,22 @@ spec:
|
||||
{{- if .Values.controller.extraContainers }}
|
||||
{{ toYaml .Values.controller.extraContainers | nindent 8 }}
|
||||
{{- end }}
|
||||
|
||||
|
||||
{{- if (or .Values.controller.extraInitContainers .Values.controller.extraModules) }}
|
||||
{{- if (or .Values.controller.extraInitContainers .Values.controller.extraModules .Values.controller.opentelemetry.enabled) }}
|
||||
initContainers:
|
||||
{{- if .Values.controller.extraInitContainers }}
|
||||
{{ toYaml .Values.controller.extraInitContainers | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.extraModules }}
|
||||
{{- range .Values.controller.extraModules }}
|
||||
- name: {{ .Name }}
|
||||
image: {{ .Image }}
|
||||
command: ['sh', '-c', '/usr/local/bin/init_module.sh']
|
||||
{{- $containerSecurityContext := .containerSecurityContext | default $.Values.controller.containerSecurityContext }}
|
||||
{{- include "extraModules" (dict "name" .name "image" .image "containerSecurityContext" $containerSecurityContext) | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.opentelemetry.enabled}}
|
||||
{{- $otelContainerSecurityContext := $.Values.controller.opentelemetry.containerSecurityContext | default $.Values.controller.containerSecurityContext }}
|
||||
{{ $otelResources := $.Values.controller.opentelemetry.resources | default dict }}
|
||||
{{- include "extraModules" (dict "name" "opentelemetry" "image" .Values.controller.opentelemetry.image "containerSecurityContext" $otelContainerSecurityContext "distroless" true "resources" $otelResources) | nindent 8}}
|
||||
{{- end}}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.hostNetwork }}
|
||||
hostNetwork: {{ .Values.controller.hostNetwork }}
|
||||
@@ -193,13 +206,13 @@ spec:
|
||||
affinity: {{ toYaml .Values.controller.affinity | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.topologySpreadConstraints }}
|
||||
topologySpreadConstraints: {{ toYaml .Values.controller.topologySpreadConstraints | nindent 8 }}
|
||||
topologySpreadConstraints: {{ tpl (toYaml .Values.controller.topologySpreadConstraints) $ | nindent 8 }}
|
||||
{{- end }}
|
||||
serviceAccountName: {{ template "ingress-nginx.serviceAccountName" . }}
|
||||
terminationGracePeriodSeconds: {{ .Values.controller.terminationGracePeriodSeconds }}
|
||||
{{- if (or .Values.controller.customTemplate.configMapName .Values.controller.extraVolumeMounts .Values.controller.admissionWebhooks.enabled .Values.controller.extraVolumes .Values.controller.extraModules) }}
|
||||
{{- if (or .Values.controller.customTemplate.configMapName .Values.controller.extraVolumeMounts .Values.controller.admissionWebhooks.enabled .Values.controller.extraVolumes .Values.controller.extraModules .Values.controller.opentelemetry.enabled) }}
|
||||
volumes:
|
||||
{{- if .Values.controller.extraModules }}
|
||||
{{- if (or .Values.controller.extraModules .Values.controller.opentelemetry.enabled)}}
|
||||
- name: modules
|
||||
emptyDir: {}
|
||||
{{- end }}
|
||||
@@ -215,6 +228,13 @@ spec:
|
||||
- name: webhook-cert
|
||||
secret:
|
||||
secretName: {{ include "ingress-nginx.fullname" . }}-admission
|
||||
{{- if .Values.controller.admissionWebhooks.certManager.enabled }}
|
||||
items:
|
||||
- key: tls.crt
|
||||
path: cert
|
||||
- key: tls.key
|
||||
path: key
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.extraVolumes }}
|
||||
{{ toYaml .Values.controller.extraVolumes | nindent 8 }}
|
||||
|
||||
@@ -1,4 +1,4 @@
|
||||
{{- if or (eq .Values.controller.kind "Deployment") (eq .Values.controller.kind "Both") -}}
|
||||
{{- if and (eq .Values.kind "Vanilla") (eq .Values.controller.kind "Deployment") -}}
|
||||
{{- include "isControllerTagValid" . -}}
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
@@ -10,7 +10,7 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.controller.fullname" . }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
{{- if .Values.controller.annotations }}
|
||||
annotations: {{ toYaml .Values.controller.annotations | nindent 4 }}
|
||||
{{- end }}
|
||||
@@ -19,13 +19,12 @@ spec:
|
||||
matchLabels:
|
||||
{{- include "ingress-nginx.selectorLabels" . | nindent 6 }}
|
||||
app.kubernetes.io/component: controller
|
||||
{{- if not .Values.controller.autoscaling.enabled }}
|
||||
{{- if not (or .Values.controller.autoscaling.enabled .Values.controller.keda.enabled) }}
|
||||
replicas: {{ .Values.controller.replicaCount }}
|
||||
{{- end }}
|
||||
revisionHistoryLimit: {{ .Values.revisionHistoryLimit }}
|
||||
{{- if .Values.controller.updateStrategy }}
|
||||
strategy:
|
||||
{{ toYaml .Values.controller.updateStrategy | nindent 4 }}
|
||||
strategy: {{ toYaml .Values.controller.updateStrategy | nindent 4 }}
|
||||
{{- end }}
|
||||
minReadySeconds: {{ .Values.controller.minReadySeconds }}
|
||||
template:
|
||||
@@ -37,7 +36,7 @@ spec:
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
labels:
|
||||
{{- include "ingress-nginx.selectorLabels" . | nindent 8 }}
|
||||
{{- include "ingress-nginx.labels" . | nindent 8 }}
|
||||
app.kubernetes.io/component: controller
|
||||
{{- with .Values.controller.labels }}
|
||||
{{- toYaml . | nindent 8 }}
|
||||
@@ -49,6 +48,9 @@ spec:
|
||||
{{- if .Values.controller.dnsConfig }}
|
||||
dnsConfig: {{ toYaml .Values.controller.dnsConfig | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.hostAliases }}
|
||||
hostAliases: {{ tpl (toYaml .Values.controller.hostAliases) $ | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.hostname }}
|
||||
hostname: {{ toYaml .Values.controller.hostname | nindent 8 }}
|
||||
{{- end }}
|
||||
@@ -78,7 +80,7 @@ spec:
|
||||
containers:
|
||||
- name: {{ .Values.controller.containerName }}
|
||||
{{- with .Values.controller.image }}
|
||||
image: "{{- if .repository -}}{{ .repository }}{{ else }}{{ .registry }}/{{ .image }}{{- end -}}{{- if .tag }}:{{ .tag }}{{- end -}}{{- if (.digest) -}} @{{.digest}} {{- end -}}"
|
||||
image: "{{- if .repository -}}{{ .repository }}{{ else }}{{ .registry }}/{{ include "ingress-nginx.image" . }}{{- end -}}:{{ .tag }}{{ include "ingress-nginx.imageDigest" . }}"
|
||||
{{- end }}
|
||||
imagePullPolicy: {{ .Values.controller.image.pullPolicy }}
|
||||
{{- if .Values.controller.lifecycle }}
|
||||
@@ -106,8 +108,12 @@ spec:
|
||||
{{- if .Values.controller.startupProbe }}
|
||||
startupProbe: {{ toYaml .Values.controller.startupProbe | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.livenessProbe }}
|
||||
livenessProbe: {{ toYaml .Values.controller.livenessProbe | nindent 12 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.readinessProbe }}
|
||||
readinessProbe: {{ toYaml .Values.controller.readinessProbe | nindent 12 }}
|
||||
{{- end }}
|
||||
ports:
|
||||
{{- range $key, $value := .Values.controller.containerPort }}
|
||||
- name: {{ $key }}
|
||||
@@ -118,7 +124,7 @@ spec:
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.metrics.enabled }}
|
||||
- name: metrics
|
||||
- name: {{ .Values.controller.metrics.portName }}
|
||||
containerPort: {{ .Values.controller.metrics.port }}
|
||||
protocol: TCP
|
||||
{{- end }}
|
||||
@@ -143,11 +149,15 @@ spec:
|
||||
hostPort: {{ $key }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if (or .Values.controller.customTemplate.configMapName .Values.controller.extraVolumeMounts .Values.controller.admissionWebhooks.enabled .Values.controller.extraModules) }}
|
||||
{{- if (or .Values.controller.customTemplate.configMapName .Values.controller.extraVolumeMounts .Values.controller.admissionWebhooks.enabled .Values.controller.extraModules .Values.controller.opentelemetry.enabled) }}
|
||||
volumeMounts:
|
||||
{{- if .Values.controller.extraModules }}
|
||||
{{- if (or .Values.controller.extraModules .Values.controller.opentelemetry.enabled) }}
|
||||
- name: modules
|
||||
{{ if .Values.controller.image.chroot }}
|
||||
mountPath: /chroot/modules_mount
|
||||
{{ else }}
|
||||
mountPath: /modules_mount
|
||||
{{ end }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.customTemplate.configMapName }}
|
||||
- mountPath: /etc/nginx/template
|
||||
@@ -166,51 +176,25 @@ spec:
|
||||
{{- if .Values.controller.resources }}
|
||||
resources: {{ toYaml .Values.controller.resources | nindent 12 }}
|
||||
{{- end }}
|
||||
- name: {{ .Values.appsec.name }}
|
||||
securityContext:
|
||||
{{ toYaml .Values.appsec.securityContext | nindent 12 }}
|
||||
{{- with .Values.appsec.image }}
|
||||
image: "{{- if .registry }}{{ .registry }}/{{- end }}{{- if .repository }}{{ .repository }}/{{- end }}{{ .image }}{{- if .tag }}:{{ .tag }}{{- end }}{{- if (.digest) -}} @{{.digest}} {{- end }}"
|
||||
{{- end }}
|
||||
args:
|
||||
- --token
|
||||
- {{ .Values.appsec.agentToken }}
|
||||
{{- if .Values.appsec.customFog.enabled }}
|
||||
- --fog
|
||||
- {{ .Values.appsec.customFog.fogAddress }}
|
||||
{{- end }}
|
||||
{{- if .Values.appsec.proxy }}
|
||||
- --proxy
|
||||
- {{ .Values.appsec.proxy }}
|
||||
{{- end }}
|
||||
command:
|
||||
- {{ .Values.appsec.command }}
|
||||
imagePullPolicy: {{ .Values.appsec.image.pullPolicy }}
|
||||
resources:
|
||||
{{ toYaml .Values.resources | nindent 12 }}
|
||||
volumeMounts:
|
||||
- name: appsec-conf
|
||||
mountPath: /etc/cp/conf
|
||||
- name: appsec-data
|
||||
mountPath: /etc/cp/data
|
||||
{{- if .Values.controller.extraContainers }}
|
||||
{{ toYaml .Values.controller.extraContainers | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if (or .Values.controller.extraInitContainers .Values.controller.extraModules) }}
|
||||
{{- if (or .Values.controller.extraInitContainers .Values.controller.extraModules .Values.controller.opentelemetry.enabled) }}
|
||||
initContainers:
|
||||
{{- if .Values.controller.extraInitContainers }}
|
||||
{{ toYaml .Values.controller.extraInitContainers | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.extraModules }}
|
||||
{{- range .Values.controller.extraModules }}
|
||||
- name: {{ .name }}
|
||||
image: {{ .image }}
|
||||
command: ['sh', '-c', '/usr/local/bin/init_module.sh']
|
||||
volumeMounts:
|
||||
- name: modules
|
||||
mountPath: /modules_mount
|
||||
{{- $containerSecurityContext := .containerSecurityContext | default $.Values.controller.containerSecurityContext }}
|
||||
{{- include "extraModules" (dict "name" .name "image" .image "containerSecurityContext" $containerSecurityContext) | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.opentelemetry.enabled}}
|
||||
{{- $otelContainerSecurityContext := $.Values.controller.opentelemetry.containerSecurityContext | default $.Values.controller.containerSecurityContext }}
|
||||
{{ $otelResources := $.Values.controller.opentelemetry.resources | default dict }}
|
||||
{{- include "extraModules" (dict "name" "opentelemetry" "image" .Values.controller.opentelemetry.image "containerSecurityContext" $otelContainerSecurityContext "distroless" true "resources" $otelResources) | nindent 8}}
|
||||
{{- end}}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.hostNetwork }}
|
||||
hostNetwork: {{ .Values.controller.hostNetwork }}
|
||||
@@ -225,19 +209,13 @@ spec:
|
||||
affinity: {{ toYaml .Values.controller.affinity | nindent 8 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.topologySpreadConstraints }}
|
||||
topologySpreadConstraints: {{ toYaml .Values.controller.topologySpreadConstraints | nindent 8 }}
|
||||
topologySpreadConstraints: {{ tpl (toYaml .Values.controller.topologySpreadConstraints) $ | nindent 8 }}
|
||||
{{- end }}
|
||||
serviceAccountName: {{ template "ingress-nginx.serviceAccountName" . }}
|
||||
terminationGracePeriodSeconds: {{ .Values.controller.terminationGracePeriodSeconds }}
|
||||
{{- if (or .Values.controller.customTemplate.configMapName .Values.controller.extraVolumeMounts .Values.controller.admissionWebhooks.enabled .Values.controller.extraVolumes .Values.controller.extraModules .Values.controller.opentelemetry.enabled) }}
|
||||
volumes:
|
||||
- name: appsec-conf
|
||||
persistentVolumeClaim:
|
||||
claimName: {{ .Values.appsec.name }}-conf
|
||||
- name: appsec-data
|
||||
persistentVolumeClaim:
|
||||
claimName: {{ .Values.appsec.name }}-data
|
||||
{{- if (or .Values.controller.customTemplate.configMapName .Values.controller.extraVolumeMounts .Values.controller.admissionWebhooks.enabled .Values.controller.extraVolumes .Values.controller.extraModules) }}
|
||||
{{- if .Values.controller.extraModules }}
|
||||
{{- if (or .Values.controller.extraModules .Values.controller.opentelemetry.enabled)}}
|
||||
- name: modules
|
||||
emptyDir: {}
|
||||
{{- end }}
|
||||
@@ -253,6 +231,13 @@ spec:
|
||||
- name: webhook-cert
|
||||
secret:
|
||||
secretName: {{ include "ingress-nginx.fullname" . }}-admission
|
||||
{{- if .Values.controller.admissionWebhooks.certManager.enabled }}
|
||||
items:
|
||||
- key: tls.crt
|
||||
path: cert
|
||||
- key: tls.key
|
||||
path: key
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.extraVolumes }}
|
||||
{{ toYaml .Values.controller.extraVolumes | nindent 8 }}
|
||||
|
||||
@@ -1,12 +1,9 @@
|
||||
{{- if and .Values.controller.autoscaling.enabled (or (eq .Values.controller.kind "Deployment") (eq .Values.controller.kind "Both")) -}}
|
||||
{{- if not .Values.controller.keda.enabled }}
|
||||
|
||||
apiVersion: autoscaling/v2beta2
|
||||
{{- if and (eq .Values.controller.kind "Deployment") .Values.controller.autoscaling.enabled (not .Values.controller.keda.enabled) -}}
|
||||
apiVersion: {{ ternary "autoscaling/v2" "autoscaling/v2beta2" (.Capabilities.APIVersions.Has "autoscaling/v2") }}
|
||||
kind: HorizontalPodAutoscaler
|
||||
metadata:
|
||||
annotations:
|
||||
{{- with .Values.controller.autoscaling.annotations }}
|
||||
{{- toYaml . | trimSuffix "\n" | nindent 4 }}
|
||||
annotations: {{ toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
labels:
|
||||
{{- include "ingress-nginx.labels" . | nindent 4 }}
|
||||
@@ -15,7 +12,7 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.controller.fullname" . }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
spec:
|
||||
scaleTargetRef:
|
||||
apiVersion: apps/v1
|
||||
@@ -48,5 +45,3 @@ spec:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
|
||||
@@ -1,4 +1,4 @@
|
||||
{{- if and .Values.controller.keda.enabled (or (eq .Values.controller.kind "Deployment") (eq .Values.controller.kind "Both")) -}}
|
||||
{{- if and .Values.controller.keda.enabled (eq .Values.controller.kind "Deployment") -}}
|
||||
# https://keda.sh/docs/
|
||||
|
||||
apiVersion: {{ .Values.controller.keda.apiVersion }}
|
||||
@@ -25,6 +25,11 @@ spec:
|
||||
cooldownPeriod: {{ .Values.controller.keda.cooldownPeriod }}
|
||||
minReplicaCount: {{ .Values.controller.keda.minReplicas }}
|
||||
maxReplicaCount: {{ .Values.controller.keda.maxReplicas }}
|
||||
{{- with .Values.controller.keda.fallback }}
|
||||
fallback:
|
||||
failureThreshold: {{ .failureThreshold | default 3 }}
|
||||
replicas: {{ .replicas | default $.Values.controller.keda.maxReplicas }}
|
||||
{{- end }}
|
||||
triggers:
|
||||
{{- with .Values.controller.keda.triggers }}
|
||||
{{ toYaml . | indent 2 }}
|
||||
|
||||
@@ -0,0 +1,45 @@
|
||||
{{- if .Values.controller.networkPolicy.enabled }}
|
||||
apiVersion: networking.k8s.io/v1
|
||||
kind: NetworkPolicy
|
||||
metadata:
|
||||
labels:
|
||||
{{- include "ingress-nginx.labels" . | nindent 4 }}
|
||||
app.kubernetes.io/component: controller
|
||||
{{- with .Values.controller.labels }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.controller.fullname" . }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
spec:
|
||||
podSelector:
|
||||
matchLabels:
|
||||
{{- include "ingress-nginx.selectorLabels" . | nindent 6 }}
|
||||
app.kubernetes.io/component: controller
|
||||
policyTypes:
|
||||
- Ingress
|
||||
- Egress
|
||||
ingress:
|
||||
- ports:
|
||||
{{- range $key, $value := .Values.controller.containerPort }}
|
||||
- protocol: TCP
|
||||
port: {{ $value }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.metrics.enabled }}
|
||||
- protocol: TCP
|
||||
port: {{ .Values.controller.metrics.port }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.admissionWebhooks.enabled }}
|
||||
- protocol: TCP
|
||||
port: {{ .Values.controller.admissionWebhooks.port }}
|
||||
{{- end }}
|
||||
{{- range $key, $value := .Values.tcp }}
|
||||
- protocol: TCP
|
||||
port: {{ $key }}
|
||||
{{- end }}
|
||||
{{- range $key, $value := .Values.udp }}
|
||||
- protocol: UDP
|
||||
port: {{ $key }}
|
||||
{{- end }}
|
||||
egress:
|
||||
- {}
|
||||
{{- end }}
|
||||
@@ -9,11 +9,18 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.controller.fullname" . }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
{{- if .Values.controller.annotations }}
|
||||
annotations: {{ toYaml .Values.controller.annotations | nindent 4 }}
|
||||
{{- end }}
|
||||
spec:
|
||||
selector:
|
||||
matchLabels:
|
||||
{{- include "ingress-nginx.selectorLabels" . | nindent 6 }}
|
||||
app.kubernetes.io/component: controller
|
||||
{{- if and .Values.controller.minAvailable (not (hasKey .Values.controller "maxUnavailable")) }}
|
||||
minAvailable: {{ .Values.controller.minAvailable }}
|
||||
{{- else if .Values.controller.maxUnavailable }}
|
||||
maxUnavailable: {{ .Values.controller.maxUnavailable }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
@@ -1,4 +1,4 @@
|
||||
{{- if and .Values.controller.metrics.enabled .Values.controller.metrics.prometheusRule.enabled -}}
|
||||
{{- if and ( .Values.controller.metrics.enabled ) ( .Values.controller.metrics.prometheusRule.enabled ) ( .Capabilities.APIVersions.Has "monitoring.coreos.com/v1" ) -}}
|
||||
apiVersion: monitoring.coreos.com/v1
|
||||
kind: PrometheusRule
|
||||
metadata:
|
||||
|
||||
@@ -1,3 +1,4 @@
|
||||
{{- if (semverCompare "<1.25.0-0" .Capabilities.KubeVersion.Version) }}
|
||||
{{- if and .Values.podSecurityPolicy.enabled (empty .Values.controller.existingPsp) -}}
|
||||
apiVersion: policy/v1beta1
|
||||
kind: PodSecurityPolicy
|
||||
@@ -27,9 +28,9 @@ spec:
|
||||
volumes:
|
||||
- 'configMap'
|
||||
- 'emptyDir'
|
||||
#- 'projected'
|
||||
- 'projected'
|
||||
- 'secret'
|
||||
#- 'downwardAPI'
|
||||
- 'downwardAPI'
|
||||
{{- if .Values.controller.hostNetwork }}
|
||||
hostNetwork: {{ .Values.controller.hostNetwork }}
|
||||
{{- end }}
|
||||
@@ -90,3 +91,4 @@ spec:
|
||||
seLinux:
|
||||
rule: 'RunAsAny'
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
@@ -9,7 +9,7 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.fullname" . }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
rules:
|
||||
- apiGroups:
|
||||
- ""
|
||||
@@ -59,18 +59,18 @@ rules:
|
||||
- list
|
||||
- watch
|
||||
- apiGroups:
|
||||
- ""
|
||||
- coordination.k8s.io
|
||||
resources:
|
||||
- configmaps
|
||||
- leases
|
||||
resourceNames:
|
||||
- {{ .Values.controller.electionID }}
|
||||
- {{ include "ingress-nginx.controller.electionID" . }}
|
||||
verbs:
|
||||
- get
|
||||
- update
|
||||
- apiGroups:
|
||||
- ""
|
||||
- coordination.k8s.io
|
||||
resources:
|
||||
- configmaps
|
||||
- leases
|
||||
verbs:
|
||||
- create
|
||||
- apiGroups:
|
||||
@@ -80,6 +80,14 @@ rules:
|
||||
verbs:
|
||||
- create
|
||||
- patch
|
||||
- apiGroups:
|
||||
- discovery.k8s.io
|
||||
resources:
|
||||
- endpointslices
|
||||
verbs:
|
||||
- list
|
||||
- watch
|
||||
- get
|
||||
- apiGroups:
|
||||
- openappsec.io
|
||||
resources:
|
||||
|
||||
@@ -9,7 +9,7 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.fullname" . }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
roleRef:
|
||||
apiGroup: rbac.authorization.k8s.io
|
||||
kind: Role
|
||||
@@ -17,5 +17,5 @@ roleRef:
|
||||
subjects:
|
||||
- kind: ServiceAccount
|
||||
name: {{ template "ingress-nginx.serviceAccountName" . }}
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
namespace: {{ (include "ingress-nginx.namespace" .) | quote }}
|
||||
{{- end }}
|
||||
|
||||
@@ -0,0 +1,15 @@
|
||||
{{- if .Values.dhParam -}}
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
labels:
|
||||
{{- include "ingress-nginx.labels" . | nindent 4 }}
|
||||
app.kubernetes.io/component: controller
|
||||
{{- with .Values.controller.labels }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.controller.fullname" . }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
data:
|
||||
dhparam.pem: {{ .Values.dhParam }}
|
||||
{{- end }}
|
||||
@@ -4,7 +4,7 @@ kind: Service
|
||||
metadata:
|
||||
annotations:
|
||||
{{- range $key, $value := .Values.controller.service.internal.annotations }}
|
||||
{{ $key }}: {{ $value | quote }}
|
||||
{{ $key }}: {{ tpl ($value | toString) $ | quote }}
|
||||
{{- end }}
|
||||
labels:
|
||||
{{- include "ingress-nginx.labels" . | nindent 4 }}
|
||||
@@ -13,7 +13,7 @@ metadata:
|
||||
{{- toYaml .Values.controller.service.labels | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.controller.fullname" . }}-internal
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
spec:
|
||||
type: "{{ .Values.controller.service.type }}"
|
||||
{{- if .Values.controller.service.internal.loadBalancerIP }}
|
||||
@@ -29,9 +29,9 @@ spec:
|
||||
{{- $setNodePorts := (or (eq .Values.controller.service.type "NodePort") (eq .Values.controller.service.type "LoadBalancer")) }}
|
||||
{{- if .Values.controller.service.enableHttp }}
|
||||
- name: http
|
||||
port: {{ .Values.controller.service.ports.http }}
|
||||
port: {{ .Values.controller.service.internal.ports.http | default .Values.controller.service.ports.http }}
|
||||
protocol: TCP
|
||||
targetPort: {{ .Values.controller.service.targetPorts.http }}
|
||||
targetPort: {{ .Values.controller.service.internal.targetPorts.http | default .Values.controller.service.targetPorts.http }}
|
||||
{{- if semverCompare ">=1.20" .Capabilities.KubeVersion.Version }}
|
||||
appProtocol: http
|
||||
{{- end }}
|
||||
@@ -41,9 +41,9 @@ spec:
|
||||
{{- end }}
|
||||
{{- if .Values.controller.service.enableHttps }}
|
||||
- name: https
|
||||
port: {{ .Values.controller.service.ports.https }}
|
||||
port: {{ .Values.controller.service.internal.ports.https | default .Values.controller.service.ports.https }}
|
||||
protocol: TCP
|
||||
targetPort: {{ .Values.controller.service.targetPorts.https }}
|
||||
targetPort: {{ .Values.controller.service.internal.targetPorts.https | default .Values.controller.service.targetPorts.https }}
|
||||
{{- if semverCompare ">=1.20" .Capabilities.KubeVersion.Version }}
|
||||
appProtocol: https
|
||||
{{- end }}
|
||||
|
||||
@@ -12,7 +12,7 @@ metadata:
|
||||
{{- toYaml .Values.controller.metrics.service.labels | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.controller.fullname" . }}-metrics
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
spec:
|
||||
type: {{ .Values.controller.metrics.service.type }}
|
||||
{{- if .Values.controller.metrics.service.clusterIP }}
|
||||
@@ -31,10 +31,10 @@ spec:
|
||||
externalTrafficPolicy: {{ .Values.controller.metrics.service.externalTrafficPolicy }}
|
||||
{{- end }}
|
||||
ports:
|
||||
- name: metrics
|
||||
- name: {{ .Values.controller.metrics.portName }}
|
||||
port: {{ .Values.controller.metrics.service.servicePort }}
|
||||
protocol: TCP
|
||||
targetPort: metrics
|
||||
targetPort: {{ .Values.controller.metrics.portName }}
|
||||
{{- $setNodePorts := (or (eq .Values.controller.metrics.service.type "NodePort") (eq .Values.controller.metrics.service.type "LoadBalancer")) }}
|
||||
{{- if (and $setNodePorts (not (empty .Values.controller.metrics.service.nodePort))) }}
|
||||
nodePort: {{ .Values.controller.metrics.service.nodePort }}
|
||||
|
||||
@@ -12,7 +12,7 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.controller.fullname" . }}-admission
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
spec:
|
||||
type: {{ .Values.controller.admissionWebhooks.service.type }}
|
||||
{{- if .Values.controller.admissionWebhooks.service.clusterIP }}
|
||||
|
||||
@@ -4,7 +4,7 @@ kind: Service
|
||||
metadata:
|
||||
annotations:
|
||||
{{- range $key, $value := .Values.controller.service.annotations }}
|
||||
{{ $key }}: {{ $value | quote }}
|
||||
{{ $key }}: {{ tpl ($value | toString) $ | quote }}
|
||||
{{- end }}
|
||||
labels:
|
||||
{{- include "ingress-nginx.labels" . | nindent 4 }}
|
||||
@@ -13,7 +13,7 @@ metadata:
|
||||
{{- toYaml .Values.controller.service.labels | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.controller.fullname" . }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
spec:
|
||||
type: {{ .Values.controller.service.type }}
|
||||
{{- if .Values.controller.service.clusterIP }}
|
||||
@@ -28,6 +28,9 @@ spec:
|
||||
{{- if .Values.controller.service.loadBalancerSourceRanges }}
|
||||
loadBalancerSourceRanges: {{ toYaml .Values.controller.service.loadBalancerSourceRanges | nindent 4 }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.service.loadBalancerClass }}
|
||||
loadBalancerClass: {{ .Values.controller.service.loadBalancerClass }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.service.externalTrafficPolicy }}
|
||||
externalTrafficPolicy: {{ .Values.controller.service.externalTrafficPolicy }}
|
||||
{{- end }}
|
||||
|
||||
@@ -9,10 +9,9 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ template "ingress-nginx.serviceAccountName" . }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
{{- if .Values.serviceAccount.annotations }}
|
||||
annotations:
|
||||
{{ toYaml .Values.serviceAccount.annotations | indent 4 }}
|
||||
annotations: {{ toYaml .Values.serviceAccount.annotations | nindent 4 }}
|
||||
{{- end }}
|
||||
automountServiceAccountToken: {{ .Values.serviceAccount.automountServiceAccountToken }}
|
||||
{{- end }}
|
||||
|
||||
@@ -5,6 +5,8 @@ metadata:
|
||||
name: {{ include "ingress-nginx.controller.fullname" . }}
|
||||
{{- if .Values.controller.metrics.serviceMonitor.namespace }}
|
||||
namespace: {{ .Values.controller.metrics.serviceMonitor.namespace | quote }}
|
||||
{{- else }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
{{- end }}
|
||||
labels:
|
||||
{{- include "ingress-nginx.labels" . | nindent 4 }}
|
||||
@@ -14,7 +16,7 @@ metadata:
|
||||
{{- end }}
|
||||
spec:
|
||||
endpoints:
|
||||
- port: metrics
|
||||
- port: {{ .Values.controller.metrics.portName }}
|
||||
interval: {{ .Values.controller.metrics.serviceMonitor.scrapeInterval }}
|
||||
{{- if .Values.controller.metrics.serviceMonitor.honorLabels }}
|
||||
honorLabels: true
|
||||
@@ -33,7 +35,7 @@ spec:
|
||||
{{- else }}
|
||||
namespaceSelector:
|
||||
matchNames:
|
||||
- {{ .Release.Namespace }}
|
||||
- {{ include "ingress-nginx.namespace" . }}
|
||||
{{- end }}
|
||||
{{- if .Values.controller.metrics.serviceMonitor.targetLabels }}
|
||||
targetLabels:
|
||||
|
||||
@@ -9,7 +9,7 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.defaultBackend.fullname" . }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
spec:
|
||||
selector:
|
||||
matchLabels:
|
||||
@@ -19,6 +19,11 @@ spec:
|
||||
replicas: {{ .Values.defaultBackend.replicaCount }}
|
||||
{{- end }}
|
||||
revisionHistoryLimit: {{ .Values.revisionHistoryLimit }}
|
||||
{{- if .Values.defaultBackend.updateStrategy }}
|
||||
strategy:
|
||||
{{ toYaml .Values.defaultBackend.updateStrategy | nindent 4 }}
|
||||
{{- end }}
|
||||
minReadySeconds: {{ .Values.defaultBackend.minReadySeconds }}
|
||||
template:
|
||||
metadata:
|
||||
{{- if .Values.defaultBackend.podAnnotations }}
|
||||
|
||||
@@ -1,33 +1,40 @@
|
||||
{{- if and .Values.defaultBackend.enabled .Values.defaultBackend.autoscaling.enabled }}
|
||||
apiVersion: autoscaling/v2beta1
|
||||
apiVersion: {{ ternary "autoscaling/v2" "autoscaling/v2beta2" (.Capabilities.APIVersions.Has "autoscaling/v2") }}
|
||||
kind: HorizontalPodAutoscaler
|
||||
metadata:
|
||||
{{- with .Values.defaultBackend.autoscaling.annotations }}
|
||||
annotations: {{ toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
labels:
|
||||
{{- include "ingress-nginx.labels" . | nindent 4 }}
|
||||
app.kubernetes.io/component: default-backend
|
||||
{{- with .Values.defaultBackend.labels }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ template "ingress-nginx.defaultBackend.fullname" . }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
name: {{ include "ingress-nginx.defaultBackend.fullname" . }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
spec:
|
||||
scaleTargetRef:
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
name: {{ template "ingress-nginx.defaultBackend.fullname" . }}
|
||||
name: {{ include "ingress-nginx.defaultBackend.fullname" . }}
|
||||
minReplicas: {{ .Values.defaultBackend.autoscaling.minReplicas }}
|
||||
maxReplicas: {{ .Values.defaultBackend.autoscaling.maxReplicas }}
|
||||
metrics:
|
||||
{{- with .Values.defaultBackend.autoscaling.targetCPUUtilizationPercentage }}
|
||||
- type: Resource
|
||||
resource:
|
||||
name: cpu
|
||||
targetAverageUtilization: {{ . }}
|
||||
{{- end }}
|
||||
{{- with .Values.defaultBackend.autoscaling.targetMemoryUtilizationPercentage }}
|
||||
- type: Resource
|
||||
resource:
|
||||
name: memory
|
||||
targetAverageUtilization: {{ . }}
|
||||
{{- end }}
|
||||
{{- with .Values.defaultBackend.autoscaling.targetCPUUtilizationPercentage }}
|
||||
- type: Resource
|
||||
resource:
|
||||
name: cpu
|
||||
target:
|
||||
type: Utilization
|
||||
averageUtilization: {{ . }}
|
||||
{{- end }}
|
||||
{{- with .Values.defaultBackend.autoscaling.targetMemoryUtilizationPercentage }}
|
||||
- type: Resource
|
||||
resource:
|
||||
name: memory
|
||||
target:
|
||||
type: Utilization
|
||||
averageUtilization: {{ . }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
@@ -0,0 +1,25 @@
|
||||
{{- if and .Values.defaultBackend.enabled .Values.defaultBackend.networkPolicy.enabled }}
|
||||
apiVersion: networking.k8s.io/v1
|
||||
kind: NetworkPolicy
|
||||
metadata:
|
||||
labels:
|
||||
{{- include "ingress-nginx.labels" . | nindent 4 }}
|
||||
app.kubernetes.io/component: default-backend
|
||||
{{- with .Values.defaultBackend.labels }}
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.defaultBackend.fullname" . }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
spec:
|
||||
podSelector:
|
||||
matchLabels:
|
||||
{{- include "ingress-nginx.selectorLabels" . | nindent 6 }}
|
||||
app.kubernetes.io/component: default-backend
|
||||
policyTypes:
|
||||
- Ingress
|
||||
- Egress
|
||||
ingress:
|
||||
- ports:
|
||||
- protocol: TCP
|
||||
port: {{ .Values.defaultBackend.port }}
|
||||
{{- end }}
|
||||
@@ -10,7 +10,7 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.defaultBackend.fullname" . }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
spec:
|
||||
selector:
|
||||
matchLabels:
|
||||
|
||||
@@ -1,3 +1,4 @@
|
||||
{{- if (semverCompare "<1.25.0-0" .Capabilities.KubeVersion.Version) }}
|
||||
{{- if and .Values.podSecurityPolicy.enabled .Values.defaultBackend.enabled (empty .Values.defaultBackend.existingPsp) -}}
|
||||
apiVersion: policy/v1beta1
|
||||
kind: PodSecurityPolicy
|
||||
@@ -34,3 +35,4 @@ spec:
|
||||
- secret
|
||||
- downwardAPI
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
@@ -9,7 +9,7 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.fullname" . }}-backend
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
rules:
|
||||
- apiGroups: [{{ template "podSecurityPolicy.apiGroup" . }}]
|
||||
resources: ['podsecuritypolicies']
|
||||
|
||||
@@ -9,7 +9,7 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.fullname" . }}-backend
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
roleRef:
|
||||
apiGroup: rbac.authorization.k8s.io
|
||||
kind: Role
|
||||
@@ -17,5 +17,5 @@ roleRef:
|
||||
subjects:
|
||||
- kind: ServiceAccount
|
||||
name: {{ template "ingress-nginx.defaultBackend.serviceAccountName" . }}
|
||||
namespace: {{ .Release.Namespace | quote }}
|
||||
namespace: {{ (include "ingress-nginx.namespace" .) | quote }}
|
||||
{{- end }}
|
||||
|
||||
@@ -12,7 +12,7 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ include "ingress-nginx.defaultBackend.fullname" . }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
spec:
|
||||
type: {{ .Values.defaultBackend.service.type }}
|
||||
{{- if .Values.defaultBackend.service.clusterIP }}
|
||||
|
||||
@@ -9,6 +9,6 @@ metadata:
|
||||
{{- toYaml . | nindent 4 }}
|
||||
{{- end }}
|
||||
name: {{ template "ingress-nginx.defaultBackend.serviceAccountName" . }}
|
||||
namespace: {{ .Release.Namespace }}
|
||||
namespace: {{ include "ingress-nginx.namespace" . }}
|
||||
automountServiceAccountToken: {{ .Values.defaultBackend.serviceAccount.automountServiceAccountToken }}
|
||||
{{- end }}
|
||||
|
||||
@@ -1,10 +0,0 @@
|
||||
{{- with .Values.dhParam -}}
|
||||
apiVersion: v1
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: {{ include "ingress-nginx.controller.fullname" $ }}
|
||||
labels:
|
||||
{{- include "ingress-nginx.labels" $ | nindent 4 }}
|
||||
data:
|
||||
dhparam.pem: {{ . }}
|
||||
{{- end }}
|
||||
@@ -1,4 +1,5 @@
|
||||
{{- if and (eq "stand-alone" .Values.appsec.mode) (eq .Values.appsec.playground false) }}
|
||||
{{- if not (eq .Values.kind "Vanilla") -}}
|
||||
{{- if and (eq "standalone" .Values.appsec.mode) (eq .Values.appsec.playground false) }}
|
||||
apiVersion: apps/v1
|
||||
kind: Deployment
|
||||
metadata:
|
||||
@@ -53,7 +54,7 @@ spec:
|
||||
timeoutSeconds: 10
|
||||
env:
|
||||
- name: APPSEC_MODE
|
||||
value: {{ .Values.appsec.mode }}
|
||||
value: stand-alone
|
||||
- name: RP_BASEURL
|
||||
value: http://{{ .Values.appsec.storage.name }}-svc/api
|
||||
- name: K8S_NAMESPACE
|
||||
@@ -137,3 +138,4 @@ spec:
|
||||
claimName: {{ .Values.appsec.name }}-storage
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
@@ -1,4 +1,5 @@
|
||||
{{- if and (eq "stand-alone" .Values.appsec.mode) (eq .Values.appsec.playground false) }}
|
||||
{{- if not (eq .Values.kind "Vanilla") -}}
|
||||
{{- if and (eq "standalone" .Values.appsec.mode) (eq .Values.appsec.playground false) }}
|
||||
apiVersion: v1
|
||||
kind: Service
|
||||
metadata:
|
||||
@@ -31,3 +32,4 @@ spec:
|
||||
selector:
|
||||
app: {{ .Values.appsec.storage.name }}-lbl
|
||||
{{- end }}
|
||||
{{- end }}
|
||||
|
||||
File diff suppressed because it is too large
Load Diff
@@ -1,8 +1,341 @@
|
||||
# Changelog
|
||||
|
||||
## Unreleased
|
||||
|
||||
Nothing yet.
|
||||
|
||||
## 2.32.0
|
||||
|
||||
### Improvements
|
||||
|
||||
* Add new `deployment.hostname` value to make identifying instances in
|
||||
controlplane/dataplane configurations easier.
|
||||
[#943](https://github.com/Kong/charts/pull/943)
|
||||
|
||||
## 2.31.0
|
||||
|
||||
### Improvements
|
||||
|
||||
* Added controller's RBAC rules for `KongUpstreamPolicy` CRD.
|
||||
[#917](https://github.com/Kong/charts/pull/917)
|
||||
* Added services resource to admission webhook config for KIC >= 3.0.0.
|
||||
[#919](https://github.com/Kong/charts/pull/919)
|
||||
* Update default ingress controller version to v3.0
|
||||
[#929](https://github.com/Kong/charts/pull/929)
|
||||
[#930](https://github.com/Kong/charts/pull/930)
|
||||
|
||||
### Fixed
|
||||
|
||||
* The target port for cmetrics should only be applied if the ingress controller is enabled.
|
||||
[#926](https://github.com/Kong/charts/pull/926)
|
||||
* Fix RBAC for Gateway API v1.
|
||||
[#928](https://github.com/Kong/charts/pull/928)
|
||||
* Enable Admission webhook for Gateway API v1 resources.
|
||||
[#928](https://github.com/Kong/charts/pull/928)
|
||||
|
||||
## 2.30.0
|
||||
|
||||
### Improvements
|
||||
|
||||
* Prevent installing PodDisruptionBudget for `replicaCount: 1` or `autoscaling.minReplicas: 1`.
|
||||
[#896](https://github.com/Kong/charts/pull/896)
|
||||
* The admission webhook now will be triggered on Secrets creation for KIC 2.12.1+.
|
||||
[#907](https://github.com/Kong/charts/pull/907)
|
||||
* Container security context defaults now comply with the restricted pod
|
||||
security standard. This includes an enforced run as user ID set to 1000. UID
|
||||
1000 is used for official Kong images other than Alpine images (which use UID
|
||||
100) and for KIC images 3.0.0+ (older images use UID 65532). Images that do
|
||||
not use UID 1000 can still run with this user, as static image files are
|
||||
world-accessible and runtime-created files are created in temporary
|
||||
directories created for the run as user.
|
||||
[#911](https://github.com/Kong/charts/pull/911)
|
||||
* Allow using templates (via `tpl`) when specifying `proxy.nameOverride`.
|
||||
[#914](https://github.com/Kong/charts/pull/914)
|
||||
|
||||
## 2.29.0
|
||||
|
||||
### Improvements
|
||||
* Make it possible to set the admission webhook's `timeoutSeconds`.
|
||||
[#894](https://github.com/Kong/charts/pull/894)
|
||||
|
||||
## 2.28.1
|
||||
|
||||
### Fixed
|
||||
|
||||
* The admission webhook now includes Gateway API resources and Ingress
|
||||
resources for controller versions 2.12+. This version introduces new
|
||||
validations for Kong's regex path implementation.
|
||||
[#892](https://github.com/Kong/charts/pull/892)
|
||||
|
||||
## 2.28.0
|
||||
|
||||
### Improvements
|
||||
|
||||
* Bump default `kong` image tag to 3.4.
|
||||
[#883](https://github.com/Kong/charts/pull/883)
|
||||
* Bump default ingress controller image tag to 2.12.
|
||||
* Added validation rule for `latency` upstream load balancing algorithm to
|
||||
CRDs. [Upgrade your CRDs](https://github.com/Kong/charts/blob/main/charts/kong/UPGRADE.md#updates-to-crds)
|
||||
when installing this release.
|
||||
|
||||
## 2.27.0
|
||||
|
||||
### Improvements
|
||||
|
||||
* Listens now all support `.address` configuration. This was an existing
|
||||
setting that was not applied properly for some listens.
|
||||
[#881](https://github.com/Kong/charts/pull/881)
|
||||
|
||||
## 2.26.5
|
||||
|
||||
### Fixed
|
||||
|
||||
* Kuma ServiceAccount Token hints and volumes are also available in migrations
|
||||
Pods.
|
||||
[#877](https://github.com/Kong/charts/pull/877)
|
||||
|
||||
## 2.26.4
|
||||
|
||||
### Fixed
|
||||
|
||||
* updated `admin_api_uri` to `admin_gui_api_url` as per [kong documentation](https://docs.konghq.com/gateway/3.4.x/reference/configuration/#admin_api_uri).
|
||||
|
||||
## 2.26.3
|
||||
|
||||
### Fixed
|
||||
|
||||
* Enabled Service and Ingress in Kong Manager for non enterprise users.
|
||||
|
||||
## 2.26.2
|
||||
|
||||
### Fixed
|
||||
|
||||
* Add missing CRD KongConsumerGroup and extend status subresource for CRDs
|
||||
|
||||
## 2.26.1
|
||||
|
||||
### Fixed
|
||||
|
||||
* Fix parsing enterprise tags (like e.g. `3.4.0.0`)
|
||||
[#857](https://github.com/Kong/charts/pull/857)
|
||||
|
||||
## 2.26.0
|
||||
|
||||
### Breaking changes
|
||||
|
||||
2.26 changes the default proxy readiness endpoint for newer Kong versions. This
|
||||
causes an issue in a narrow edge case. If all of the following are true:
|
||||
|
||||
* You use Kong 3.3 or newer.
|
||||
* You use controller 2.10 or older.
|
||||
* You run the controller and proxy in separate Deployments.
|
||||
|
||||
you are affected and should review [the 2.26 upgrade instructions](https://github.com/Kong/charts/blob/main/charts/kong/UPGRADE.md#2260).
|
||||
|
||||
### Improvements
|
||||
|
||||
* Use the Kong 3.3 `/status/ready` endpoint for readiness probes by default if
|
||||
available. If not available, use the old `/status` default.
|
||||
[#844](https://github.com/Kong/charts/pull/844)
|
||||
* Add ArgoCD `Sync` and `BeforeHookCreation` [hook policies](https://argo-cd.readthedocs.io/en/stable/user-guide/resource_hooks/)
|
||||
to the the init and pre-upgrade migrations Jobs.
|
||||
* Add controller's RBAC rules for `KongConsumerGroups` CRD.
|
||||
[#850](https://github.com/Kong/charts/pull/850)
|
||||
* Updated controller version to 2.11.
|
||||
|
||||
## 2.25.0
|
||||
|
||||
- Generate the `adminApiService.name` value from `.Release.Name` rather than
|
||||
hardcoding to `kong`
|
||||
[#839](https://github.com/Kong/charts/pull/839)
|
||||
|
||||
## 2.24.0
|
||||
|
||||
### Improvements
|
||||
|
||||
* Running `tpl` against user-supplied labels and annotations used in Deployment
|
||||
[#814](https://github.com/Kong/charts/pull/814)
|
||||
|
||||
Example:
|
||||
```yaml
|
||||
podLabels:
|
||||
version: "{{ .Values.image.tag }}" # Will render dynamically when overridden downstream
|
||||
```
|
||||
|
||||
* Fail to render templates when PodSecurityPolicy was requested but cluster doesn't
|
||||
serve its API.
|
||||
[#823](https://github.com/Kong/charts/pull/823)
|
||||
* Add support for multiple hosts and tls configurations for Kong proxy `Ingress`.
|
||||
[#813](https://github.com/Kong/charts/pull/813)
|
||||
* Bump postgres default tag to `13.11.0-debian-11-r20` which includes arm64 images.
|
||||
[#834](https://github.com/Kong/charts/pull/834)
|
||||
|
||||
### Fixed
|
||||
|
||||
* Fix Ingress and HPA API versions during capabilities checking
|
||||
[#827](https://github.com/Kong/charts/pull/827)
|
||||
|
||||
## 2.23.0
|
||||
|
||||
### Improvements
|
||||
|
||||
* Add custom label configuration option for Kong proxy `Ingress`.
|
||||
[#812](https://github.com/Kong/charts/pull/812)
|
||||
* Bump default `kong/kubernetes-ingress-controller` image tag to 2.10.
|
||||
Bump default `kong` image tag to 3.3.
|
||||
[#815](https://github.com/Kong/charts/pull/815)
|
||||
|
||||
## 2.22.0
|
||||
|
||||
### Improvements
|
||||
|
||||
* Removed redundant RBAC permissions for non-existing subresources `secrets/status`
|
||||
and `endpoints/status`.
|
||||
[#798](https://github.com/Kong/charts/pull/798)
|
||||
* For Kong Ingress Controller in version >= 2.10, RBAC permissions for `Endpoints`
|
||||
are not configured anymore (because it uses `EndpointSlices`).
|
||||
[#798](https://github.com/Kong/charts/pull/798)
|
||||
* Added support for setting `certificates.cluster.commonName`. This allows a custom
|
||||
certificate `CommonName` to be provided when deploying Kong Gateway in hybrid
|
||||
mode using Cert Manager [#804](https://github.com/Kong/charts/pull/804)
|
||||
|
||||
## 2.21.0
|
||||
|
||||
### Improvements
|
||||
|
||||
* Added support for `startupProbe` on Kong pods. This can be configured via
|
||||
`.Values.startupProbe`. To maintain backward compatibility, it is disabled by default.
|
||||
[#792](https://github.com/Kong/charts/pull/792)
|
||||
* Customize Admission Webhook namespaceSelectors and compose them from values.
|
||||
[#794](https://github.com/Kong/charts/pull/794)
|
||||
* Added `CustomResourceDefinition` `list` and `watch` permissions to controller's ClusterRole.
|
||||
[#796](https://github.com/Kong/charts/pull/796)
|
||||
|
||||
## 2.20.2
|
||||
|
||||
### Fixed
|
||||
|
||||
* Automatic license provisioning for Gateways managed by Ingress Controllers in Konnect mode
|
||||
is disabled by default.
|
||||
To enable it, set `.Values.ingressController.konnect.license.enabled=true`.
|
||||
[#793](https://github.com/Kong/charts/pull/793)
|
||||
|
||||
## 2.20.1
|
||||
|
||||
### Fixed
|
||||
|
||||
* Fix correct timestamp format and remove `isCA` in certificates
|
||||
[#791](https://github.com/Kong/charts/pull/791)
|
||||
|
||||
## 2.20.0
|
||||
|
||||
### Improvements
|
||||
|
||||
* Added support for automatic license provisioning for Gateways managed by
|
||||
Ingress Controllers in Konnect mode (`.Values.ingressController.konnect.enabled=true`).
|
||||
[#787](https://github.com/Kong/charts/pull/787)
|
||||
|
||||
## 2.19.1
|
||||
|
||||
### Fixed
|
||||
|
||||
* Fix `webhook-cert` being mounted regardless if `.Values.ingressController.enabled`
|
||||
is set.
|
||||
[#779](https://github.com/Kong/charts/pull/779)
|
||||
|
||||
## 2.19.0
|
||||
|
||||
### Improvements
|
||||
|
||||
* Security context enforces read-only root filesystem by default. This is not
|
||||
expected to affect most configurations, but [will affect custom plugins that
|
||||
write to the container filesystem](https://github.com/Kong/charts/blob/main/charts/kong/UPGRADE.md#2170).
|
||||
[#770](https://github.com/Kong/charts/pull/770)
|
||||
|
||||
## 2.18.0
|
||||
|
||||
### Improvements
|
||||
|
||||
* Added support for the Admin API service TLS client verification.
|
||||
[#780](https://github.com/Kong/charts/pull/780
|
||||
|
||||
## 2.17.1
|
||||
|
||||
### Fixed
|
||||
|
||||
* The `-redhat` suffix on official KIC images is no longer considered part of
|
||||
the semver string for version checks.
|
||||
[#779](https://github.com/Kong/charts/pull/779)
|
||||
|
||||
## 2.17.0
|
||||
|
||||
### Improvements
|
||||
|
||||
* Added support for controller's gateway discovery.
|
||||
With `ingressController.gatewayDiscovery.enabled` set to `true` Kong Ingress Controller
|
||||
will enable gateway discovery using an Admin API service.
|
||||
For more information on this please see [the corresponding README.md section][kic_gateway_discovery_readme].
|
||||
This feature is only available when deploying chart with Kong Ingress Controller in version 2.9 or higher.
|
||||
[#747](https://github.com/Kong/charts/pull/747)
|
||||
* Added experimental support for the ingress controller's Konnect sync feature via `ingressController.konnect.*` values.
|
||||
This feature is only available when deploying chart with Kong Ingress Controller in version 2.9 or higher and
|
||||
requires `ingressController.gatewayDiscovery.enabled` set to `true`.
|
||||
[#746](https://github.com/Kong/charts/pull/746)
|
||||
* Added support for annotations on the admission webhook ValidatingWebhookConfiguration.
|
||||
[#760](https://github.com/Kong/charts/pull/760)
|
||||
* Added support for `subject` and `privateKey` properties on certificates.
|
||||
[#762](https://github.com/Kong/charts/pull/762)
|
||||
* Added support for loadBalancerClass in LoadBalancer type services.
|
||||
[#767](https://github.com/Kong/charts/pull/767)
|
||||
* Added support for `GRPCRoute`s.
|
||||
[#772](https://github.com/Kong/charts/pull/772)
|
||||
* Default Kong version is bumped to 3.2.
|
||||
[#773](https://github.com/Kong/charts/pull/773)
|
||||
* Added support for admissionhook to include labels.
|
||||
[#768](https://github.com/Kong/charts/pull/768)
|
||||
|
||||
### Under the hood
|
||||
|
||||
* Add kube-linter to the CI pipeline to ensure produced manifests comply
|
||||
with community best practices.
|
||||
[#751](https://github.com/Kong/charts/pull/751)
|
||||
|
||||
[kic_gateway_discovery_readme]: ./README.md#the-gatewaydiscovery-section
|
||||
|
||||
## 2.16.5
|
||||
|
||||
### Fixed
|
||||
|
||||
* Fix autoscaling version detection.
|
||||
[#752](https://github.com/Kong/charts/pull/752)
|
||||
* Don't include a clear-stale-pid initContainer when kong gateway is not
|
||||
enabled in the deployment.
|
||||
[#749](https://github.com/Kong/charts/pull/749)
|
||||
|
||||
## 2.16.4
|
||||
|
||||
### Fixed
|
||||
|
||||
* HorizontalPodAutoscaler's API version is detected properly.
|
||||
[#744](https://github.com/Kong/charts/pull/744)
|
||||
|
||||
## 2.16.3
|
||||
|
||||
### Fixed
|
||||
|
||||
* Fix template issue preventing custom dblessconfig volume from being mounted.
|
||||
[#741](https://github.com/Kong/charts/pull/741)
|
||||
|
||||
## 2.16.2
|
||||
|
||||
### Fixed
|
||||
|
||||
* The admission webhook is disabled when the ingress controller is disabled, as
|
||||
the admission webhook requires a service provided by the ingress controller.
|
||||
|
||||
## 2.16.1
|
||||
|
||||
### Fixed
|
||||
### Fixed
|
||||
|
||||
* serviceAccount projected volume is properly provisioned for GKE clusters >= 1.20.
|
||||
[#735](https://github.com/Kong/charts/pull/735)
|
||||
|
||||
@@ -1,5 +1,5 @@
|
||||
apiVersion: v2
|
||||
appVersion: "3.1"
|
||||
appVersion: 1.1.1
|
||||
dependencies:
|
||||
- condition: postgresql.enabled
|
||||
name: postgresql
|
||||
@@ -9,11 +9,9 @@ description: The Cloud-Native Ingress and API-management
|
||||
home: https://konghq.com/
|
||||
icon: https://s3.amazonaws.com/downloads.kong/universe/assets/icon-kong-inc-large.png
|
||||
maintainers:
|
||||
- email: harry@konghq.com
|
||||
name: hbagdi
|
||||
- email: traines@konghq.com
|
||||
name: rainest
|
||||
- email: team-k8s@konghq.com
|
||||
name: team-k8s-bot
|
||||
name: open-appsec-kong
|
||||
sources:
|
||||
- https://github.com/Kong/charts/tree/main/charts/kong
|
||||
version: 2.16.1
|
||||
version: 2.32.0
|
||||
|
||||
@@ -11,10 +11,10 @@ This chart bootstraps all the components needed to run Kong on a
|
||||
## TL;DR;
|
||||
|
||||
```bash
|
||||
$ helm repo add kong https://charts.konghq.com
|
||||
$ helm repo update
|
||||
helm repo add kong https://charts.konghq.com
|
||||
helm repo update
|
||||
|
||||
$ helm install kong/kong --generate-name
|
||||
helm install kong/kong --generate-name
|
||||
```
|
||||
|
||||
## Table of contents
|
||||
@@ -52,6 +52,7 @@ $ helm install kong/kong --generate-name
|
||||
- [Configuration](#configuration)
|
||||
- [Kong parameters](#kong-parameters)
|
||||
- [Kong Service Parameters](#kong-service-parameters)
|
||||
- [Admin Service mTLS](#admin-service-mtls)
|
||||
- [Stream listens](#stream-listens)
|
||||
- [Ingress Controller Parameters](#ingress-controller-parameters)
|
||||
- [The `env` section](#the-env-section)
|
||||
@@ -70,6 +71,7 @@ $ helm install kong/kong --generate-name
|
||||
- [Sessions](#sessions)
|
||||
- [Email/SMTP](#emailsmtp)
|
||||
- [Prometheus Operator integration](#prometheus-operator-integration)
|
||||
- [Argo CD considerations](#argo-cd-considerations)
|
||||
- [Changelog](https://github.com/Kong/charts/blob/main/charts/kong/CHANGELOG.md)
|
||||
- [Upgrading](https://github.com/Kong/charts/blob/main/charts/kong/UPGRADE.md)
|
||||
- [Seeking help](#seeking-help)
|
||||
@@ -89,10 +91,10 @@ $ helm install kong/kong --generate-name
|
||||
To install Kong:
|
||||
|
||||
```bash
|
||||
$ helm repo add kong https://charts.konghq.com
|
||||
$ helm repo update
|
||||
helm repo add kong https://charts.konghq.com
|
||||
helm repo update
|
||||
|
||||
$ helm install kong/kong --generate-name
|
||||
helm install kong/kong --generate-name
|
||||
```
|
||||
|
||||
## Uninstall
|
||||
@@ -100,7 +102,7 @@ $ helm install kong/kong --generate-name
|
||||
To uninstall/delete a Helm release `my-release`:
|
||||
|
||||
```bash
|
||||
$ helm delete my-release
|
||||
helm delete my-release
|
||||
```
|
||||
|
||||
The command removes all the Kubernetes components associated with the
|
||||
@@ -335,6 +337,9 @@ first and then upgrade the data plane release](https://docs.konghq.com/gateway/l
|
||||
|
||||
#### Certificates
|
||||
|
||||
> This example shows how to use Kong Hybrid mode with `cluster_mtls: shared`.
|
||||
> For an example of `cluster_mtls: pki` see the [hybrid-cert-manager example](https://github.com/Kong/charts/blob/main/charts/kong/example-values/hybrid-cert-manager/)
|
||||
|
||||
Hybrid mode uses TLS to secure the CP/DP node communication channel, and
|
||||
requires certificates for it. You can generate these either using `kong hybrid
|
||||
gen_cert` on a local Kong installation or using OpenSSL:
|
||||
@@ -431,7 +436,7 @@ admin:
|
||||
```yaml
|
||||
env:
|
||||
role: data_plane
|
||||
database: off
|
||||
database: "off"
|
||||
cluster_cert: /etc/secrets/kong-cluster-cert/tls.crt
|
||||
cluster_cert_key: /etc/secrets/kong-cluster-cert/tls.key
|
||||
lua_ssl_trusted_certificate: /etc/secrets/kong-cluster-cert/tls.crt
|
||||
@@ -446,6 +451,11 @@ documentation on Service
|
||||
DNS](https://kubernetes.io/docs/concepts/services-networking/dns-pod-service/)
|
||||
for more detail.
|
||||
|
||||
If you use multiple Helm releases to manage different data plane configurations
|
||||
attached to the same control plane, setting the `deployment.hostname` field
|
||||
will help you keep track of which is which in the `/clustering/data-plane`
|
||||
endpoint.
|
||||
|
||||
### Cert Manager Integration
|
||||
|
||||
By default, Kong will create self-signed certificates on start for its TLS
|
||||
@@ -462,7 +472,7 @@ should, however, migrate to an issuer using a CA your clients trust for actual
|
||||
usage.
|
||||
|
||||
The `proxy`, `admin`, `portal`, and `cluster` subsections under `certificates`
|
||||
let you choose hostnames or override issuers on a per-certificate basis for the
|
||||
let you choose hostnames, override issuers, set `subject` or set `privateKey` on a per-certificate basis for the
|
||||
proxy, admin API and Manager, Portal and Portal API, and hybrid mode mTLS
|
||||
services, respectively.
|
||||
|
||||
@@ -503,9 +513,9 @@ event you need to recover from unintended CRD deletion.
|
||||
|
||||
### InitContainers
|
||||
|
||||
The chart is able to deploy initcontainers along with Kong. This can be very
|
||||
The chart is able to deploy initContainers along with Kong. This can be very
|
||||
useful when there's a requirement for custom initialization. The
|
||||
`deployment.initcontainers` field in values.yaml takes an array of objects that
|
||||
`deployment.initContainers` field in values.yaml takes an array of objects that
|
||||
get appended as-is to the existing `spec.template.initContainers` array in the
|
||||
kong deployment resource.
|
||||
|
||||
@@ -576,7 +586,11 @@ namespaces. Limiting access requires several changes to configuration:
|
||||
Setting `deployment.daemonset: true` deploys Kong using a [DaemonSet
|
||||
controller](https://kubernetes.io/docs/concepts/workloads/controllers/daemonset/)
|
||||
instead of a Deployment controller. This runs a Kong Pod on every kubelet in
|
||||
the Kubernetes cluster.
|
||||
the Kubernetes cluster. For such configuration it may be desirable to configure
|
||||
Pods to use the network of the host they run on instead of a dedicated network
|
||||
namespace. The benefit of this approach is that the Kong can bind ports directly
|
||||
to Kubernetes nodes' network interfaces, without the extra network translation
|
||||
imposed by NodePort Services. It can be achieved by setting `deployment.hostNetwork: true`.
|
||||
|
||||
### Using dnsPolicy and dnsConfig
|
||||
|
||||
@@ -595,7 +609,8 @@ directory.
|
||||
| Parameter | Description | Default |
|
||||
| ---------------------------------- | ------------------------------------------------------------------------------------- | ------------------- |
|
||||
| image.repository | Kong image | `kong` |
|
||||
| image.tag | Kong image version | `2.5` |
|
||||
| image.tag | Kong image version | `3.4` |
|
||||
| image.effectiveSemver | Semantic version to use for version-dependent features (if `tag` is not a semver) | |
|
||||
| image.pullPolicy | Image pull policy | `IfNotPresent` |
|
||||
| image.pullSecrets | Image pull secrets | `null` |
|
||||
| replicaCount | Kong instance count. It has no effect when `autoscaling.enabled` is set to true | `1` |
|
||||
@@ -668,20 +683,34 @@ or `ingress` sections, as it is used only for stream listens.
|
||||
| SVC.tls.parameters | Array of additional listen parameters | `["http2"]` |
|
||||
| SVC.type | k8s service type. Options: NodePort, ClusterIP, LoadBalancer | |
|
||||
| SVC.clusterIP | k8s service clusterIP | |
|
||||
| SVC.loadBalancerClass | loadBalancerClass to use for LoadBalancer provisionning | |
|
||||
| SVC.loadBalancerSourceRanges | Limit service access to CIDRs if set and service type is `LoadBalancer` | `[]` |
|
||||
| SVC.loadBalancerIP | Reuse an existing ingress static IP for the service | |
|
||||
| SVC.externalIPs | IPs for which nodes in the cluster will also accept traffic for the servic | `[]` |
|
||||
| SVC.externalTrafficPolicy | k8s service's externalTrafficPolicy. Options: Cluster, Local | |
|
||||
| SVC.ingress.enabled | Enable ingress resource creation (works with SVC.type=ClusterIP) | `false` |
|
||||
| SVC.ingress.ingressClassName | Set the ingressClassName to associate this Ingress with an IngressClass | |
|
||||
| SVC.ingress.tls | Name of secret resource, containing TLS secret | |
|
||||
| SVC.ingress.hostname | Ingress hostname | `""` |
|
||||
| SVC.ingress.path | Ingress path. | `/` |
|
||||
| SVC.ingress.pathType | Ingress pathType. One of `ImplementationSpecific`, `Exact` or `Prefix` | `ImplementationSpecific` |
|
||||
| SVC.ingress.hosts | Slice of hosts configurations, including `hostname`, `path` and `pathType` keys | `[]` |
|
||||
| SVC.ingress.tls | Name of secret resource or slice of `secretName` and `hosts` keys | |
|
||||
| SVC.ingress.annotations | Ingress annotations. See documentation for your ingress controller for details | `{}` |
|
||||
| SVC.ingress.labels | Ingress labels. Additional custom labels to add to the ingress. | `{}` |
|
||||
| SVC.annotations | Service annotations | `{}` |
|
||||
| SVC.labels | Service labels | `{}` |
|
||||
|
||||
#### Admin Service mTLS
|
||||
|
||||
On top of the common parameters listed above, the `admin` service supports parameters for mTLS client verification.
|
||||
If any of `admin.tls.client.caBundle` or `admin.tls.client.secretName` are set, the admin service will be configured to
|
||||
require mTLS client verification. If both are set, `admin.tls.client.caBundle` will take precedence.
|
||||
|
||||
| Parameter | Description | Default |
|
||||
|-----------------------------|---------------------------------------------------------------------------------------------|---------|
|
||||
| admin.tls.client.caBundle | CA certificate to use for TLS verification of the Admin API client (PEM-encoded). | `""` |
|
||||
| admin.tls.client.secretName | CA certificate secret name - must contain a `tls.crt` key with the PEM-encoded certificate. | `""` |
|
||||
|
||||
#### Stream listens
|
||||
|
||||
The proxy configuration additionally supports creating stream listens. These
|
||||
@@ -701,30 +730,49 @@ are configured using an array of objects under `proxy.stream` and `udpProxy.stre
|
||||
All of the following properties are nested under the `ingressController`
|
||||
section of `values.yaml` file:
|
||||
|
||||
| Parameter | Description | Default |
|
||||
|-----------------------------------------|----------------------------------------------------------------------------------------------------------------------------------------------------------|------------------------------------|
|
||||
| enabled | Deploy the ingress controller, rbac and crd | true |
|
||||
| image.repository | Docker image with the ingress controller | kong/kubernetes-ingress-controller |
|
||||
| image.tag | Version of the ingress controller | 2.0 |
|
||||
| image.effectiveSemver | Version of the ingress controller used for version-specific features when image.tag is not a valid semantic version | |
|
||||
| readinessProbe | Kong ingress controllers readiness probe | |
|
||||
| livenessProbe | Kong ingress controllers liveness probe | |
|
||||
| installCRDs | Legacy toggle for Helm 2-style CRD management. Should not be set [unless necessary due to cluster permissions](#removing-cluster-scoped-permissions). | false |
|
||||
| env | Specify Kong Ingress Controller configuration via environment variables | |
|
||||
| customEnv | Specify custom environment variables (without the CONTROLLER_ prefix) | |
|
||||
| ingressClass | The name of this controller's ingressClass | kong |
|
||||
| ingressClassAnnotations | The ingress-class value for controller | kong |
|
||||
| args | List of ingress-controller cli arguments | [] |
|
||||
| watchNamespaces | List of namespaces to watch. Watches all namespaces if empty | [] |
|
||||
| admissionWebhook.enabled | Whether to enable the validating admission webhook | true |
|
||||
| admissionWebhook.failurePolicy | How unrecognized errors from the admission endpoint are handled (Ignore or Fail) | Ignore |
|
||||
| admissionWebhook.port | The port the ingress controller will listen on for admission webhooks | 8080 |
|
||||
| admissionWebhook.certificate.provided | Use a provided certificate. When set to false, the chart will automatically generate a certificate. | false |
|
||||
| admissionWebhook.certificate.secretName | Name of the TLS secret for the provided webhook certificate | |
|
||||
| admissionWebhook.certificate.caBundle | PEM encoded CA bundle which will be used to validate the provided webhook certificate | |
|
||||
| deployment.userDefinedVolumes | Create volumes. Please go to Kubernetes doc for the spec of the volumes | |
|
||||
| deployment.userDefinedVolumeMounts | Create volumeMounts. Please go to Kubernetes doc for the spec of the volumeMounts | |
|
||||
| terminationGracePeriodSeconds | Sets the [termination grace period](https://kubernetes.io/docs/concepts/containers/container-lifecycle-hooks/#hook-handler-execution) for Deployment pod | 30 |
|
||||
| Parameter | Description | Default |
|
||||
|--------------------------------------------|----------------------------------------------------------------------------------------------------------------------------------------------------------|------------------------------------|
|
||||
| enabled | Deploy the ingress controller, rbac and crd | true |
|
||||
| image.repository | Docker image with the ingress controller | kong/kubernetes-ingress-controller |
|
||||
| image.tag | Version of the ingress controller | `3.0` |
|
||||
| image.effectiveSemver | Version of the ingress controller used for version-specific features when image.tag is not a valid semantic version | |
|
||||
| readinessProbe | Kong ingress controllers readiness probe | |
|
||||
| livenessProbe | Kong ingress controllers liveness probe | |
|
||||
| installCRDs | Legacy toggle for Helm 2-style CRD management. Should not be set [unless necessary due to cluster permissions](#removing-cluster-scoped-permissions). | false |
|
||||
| env | Specify Kong Ingress Controller configuration via environment variables | |
|
||||
| customEnv | Specify custom environment variables (without the CONTROLLER_ prefix) | |
|
||||
| ingressClass | The name of this controller's ingressClass | kong |
|
||||
| ingressClassAnnotations | The ingress-class value for controller | kong |
|
||||
| args | List of ingress-controller cli arguments | [] |
|
||||
| watchNamespaces | List of namespaces to watch. Watches all namespaces if empty | [] |
|
||||
| admissionWebhook.enabled | Whether to enable the validating admission webhook | true |
|
||||
| admissionWebhook.failurePolicy | How unrecognized errors from the admission endpoint are handled (Ignore or Fail) | Ignore |
|
||||
| admissionWebhook.port | The port the ingress controller will listen on for admission webhooks | 8080 |
|
||||
| admissionWebhook.address | The address the ingress controller will listen on for admission webhooks, if not 0.0.0.0 | |
|
||||
| admissionWebhook.annotations | Annotations for the Validation Webhook Configuration | |
|
||||
| admissionWebhook.certificate.provided | Use a provided certificate. When set to false, the chart will automatically generate a certificate. | false |
|
||||
| admissionWebhook.certificate.secretName | Name of the TLS secret for the provided webhook certificate | |
|
||||
| admissionWebhook.certificate.caBundle | PEM encoded CA bundle which will be used to validate the provided webhook certificate | |
|
||||
| admissionWebhook.namespaceSelector | Add namespaceSelector to the webhook. Please go to [Kubernetes doc for the specs](https://kubernetes.io/docs/reference/access-authn-authz/extensible-admission-controllers/#matching-requests-namespaceselector) | |
|
||||
| admissionWebhook.timeoutSeconds | Kubernetes `apiserver`'s timeout when running this webhook. Default: 10 seconds. | |
|
||||
| userDefinedVolumes | Create volumes. Please go to Kubernetes doc for the spec of the volumes | |
|
||||
| userDefinedVolumeMounts | Create volumeMounts. Please go to Kubernetes doc for the spec of the volumeMounts | |
|
||||
| terminationGracePeriodSeconds | Sets the [termination grace period](https://kubernetes.io/docs/concepts/containers/container-lifecycle-hooks/#hook-handler-execution) for Deployment pod | 30 |
|
||||
| gatewayDiscovery.enabled | Enables Kong instance service discovery (for more details see [gatewayDiscovery section][gd_section]) | false |
|
||||
| gatewayDiscovery.generateAdminApiService | Generate the admin API service name based on the release name (for more details see [gatewayDiscovery section][gd_section]) | false |
|
||||
| gatewayDiscovery.adminApiService.namespace | The namespace of the Kong admin API service (for more details see [gatewayDiscovery section][gd_section]) | `.Release.Namespace` |
|
||||
| gatewayDiscovery.adminApiService.name | The name of the Kong admin API service (for more details see [gatewayDiscovery section][gd_section]) | "" |
|
||||
| konnect.enabled | Enable synchronisation of data plane configuration with Konnect Runtime Group | false |
|
||||
| konnect.runtimeGroupID | Konnect Runtime Group's unique identifier. | |
|
||||
| konnect.apiHostname | Konnect API hostname. Defaults to a production US-region. | us.kic.api.konghq.com |
|
||||
| konnect.tlsClientCertSecretName | Name of the secret that contains Konnect Runtime Group's client TLS certificate. | konnect-client-tls |
|
||||
| konnect.license.enabled | Enable automatic license provisioning for Gateways managed by Ingress Controller in Konnect mode. | false |
|
||||
| adminApi.tls.client.enabled | Enable TLS client verification for the Admin API. By default, Helm will generate certificates automatically. | false |
|
||||
| adminApi.tls.client.certProvided | Use user-provided certificates. If set to false, Helm will generate certificates. | false |
|
||||
| adminApi.tls.client.secretName | Client TLS certificate/key pair secret name. Can be also set when `certProvided` is false to enforce a generated secret's name. | "" |
|
||||
| adminApi.tls.client.caSecretName | CA TLS certificate/key pair secret name. Can be also set when `certProvided` is false to enforce a generated secret's name. | "" |
|
||||
|
||||
[gd_section]: #the-gatewayDiscovery-section
|
||||
|
||||
#### The `env` section
|
||||
For a complete list of all configuration values you can set in the
|
||||
@@ -746,6 +794,61 @@ kong:
|
||||
TZ: "Europe/Berlin"
|
||||
```
|
||||
|
||||
#### The `gatewayDiscovery` section
|
||||
|
||||
Kong Ingress Controller v2.9 has introduced gateway discovery which allows
|
||||
the controller to discover Gateway instances that it should configure using
|
||||
an Admin API Kubernetes service.
|
||||
|
||||
Using this feature requires a split release installation of Gateways and Ingress Controller.
|
||||
For exemplar `values.yaml` files which use this feature please see: [examples README.md](./example-values/README.md).
|
||||
or use the [`ingress` chart](../ingress/README.md) which can handle this for you.
|
||||
|
||||
##### Configuration
|
||||
|
||||
You'll be able to configure this feature through configuration section under
|
||||
`ingressController.gatewayDiscovery`:
|
||||
|
||||
- If `ingressController.gatewayDiscovery.enabled` is set to `false`: the ingress controller
|
||||
will control a pre-determined set of Gateway instances based on Admin API URLs
|
||||
(provided under the hood via `CONTROLLER_KONG_ADMIN_URL` environment variable).
|
||||
|
||||
- If `ingressController.gatewayDiscovery.enabled` is set to `true`: the ingress controller
|
||||
will dynamically locate Gateway instances by watching the specified Kubernetes
|
||||
service.
|
||||
(provided under the hood via `CONTROLLER_KONG_ADMIN_SVC` environment variable).
|
||||
|
||||
The following admin API Service flags have to be present in order for gateway
|
||||
discovery to work:
|
||||
|
||||
- `ingressController.gatewayDiscovery.adminApiService.name`
|
||||
- `ingressController.gatewayDiscovery.adminApiService.namespace`
|
||||
|
||||
If you set `ingressController.gatewayDiscovery.generateAdminApiService` to `true`,
|
||||
the chart will generate values for `name` and `namespace` based on the current release name and
|
||||
namespace. This is useful when consuming the `kong` chart as a subchart.
|
||||
|
||||
Additionally, you can control the addresses that are generated for your Gateways
|
||||
via the `--gateway-discovery-dns-strategy` CLI flag that can be set on the Ingress Controller
|
||||
(or an equivalent environment variable: `CONTROLLER_GATEWAY_DISCOVERY_DNS_STRATEGY`).
|
||||
It accepts 3 values which change the way that Gateway addresses are generated:
|
||||
- `service` - for service scoped pod DNS names: `pod-ip-address.service-name.my-namespace.svc.cluster-domain.example`
|
||||
- `pod` - for namespace scope pod DNS names: `pod-ip-address.my-namespace.pod.cluster-domain.example`
|
||||
- `ip` (default, retains behavior introduced in v2.9) - for regular IP addresses
|
||||
|
||||
When using `gatewayDiscovery`, you should consider configuring the Admin service to use mTLS client verification to make
|
||||
this interface secure.
|
||||
Without that, anyone who can access the Admin API from inside the cluster can configure the Gateway instances.
|
||||
|
||||
On the controller release side, that can be achieved by setting `ingressController.adminApi.tls.client.enabled` to `true`.
|
||||
By default, Helm will generate a certificate Secret named `<release name>-admin-api-keypair` and
|
||||
a CA Secret named `<release name>-admin-api-ca-keypair` for you.
|
||||
|
||||
To provide your own cert, set `ingressController.adminApi.tls.client.certProvided` to
|
||||
`true`, `ingressController.adminApi.tls.client.secretName` to the name of the Secret containing your client cert, and `ingressController.adminApi.tls.client.caSecretName` to the name of the Secret containing your CA cert.
|
||||
|
||||
On the Gateway release side, set either `admin.tls.client.secretName` to the name of your CA Secret or set `admin.tls.client.caBundle` to the CA certificate string.
|
||||
|
||||
### General Parameters
|
||||
|
||||
| Parameter | Description | Default |
|
||||
@@ -755,6 +858,7 @@ kong:
|
||||
| deployment.minReadySeconds | Minimum number of seconds for which newly created pods should be ready without any of its container crashing, for it to be considered available. | |
|
||||
| deployment.initContainers | Create initContainers. Please go to Kubernetes doc for the spec of the initContainers | |
|
||||
| deployment.daemonset | Use a DaemonSet instead of a Deployment | `false` |
|
||||
| deployment.hostname | Set the Deployment's `.spec.template.hostname`. Kong reports this as its hostname. | |
|
||||
| deployment.hostNetwork | Enable hostNetwork, which binds to the ports to the host | `false` |
|
||||
| deployment.userDefinedVolumes | Create volumes. Please go to Kubernetes doc for the spec of the volumes | |
|
||||
| deployment.userDefinedVolumeMounts | Create volumeMounts. Please go to Kubernetes doc for the spec of the volumeMounts | |
|
||||
@@ -772,6 +876,7 @@ kong:
|
||||
| updateStrategy | update strategy for deployment | `{}` |
|
||||
| readinessProbe | Kong readiness probe | |
|
||||
| livenessProbe | Kong liveness probe | |
|
||||
| startupProbe | Kong startup probe | |
|
||||
| lifecycle | Proxy container lifecycle hooks | see `values.yaml` |
|
||||
| terminationGracePeriodSeconds | Sets the [termination grace period](https://kubernetes.io/docs/concepts/containers/container-lifecycle-hooks/#hook-handler-execution) for Deployment pods | 30 |
|
||||
| affinity | Node/pod affinities | |
|
||||
@@ -794,7 +899,7 @@ kong:
|
||||
| priorityClassName | Set pod scheduling priority class for Kong pods | `""` |
|
||||
| secretVolumes | Mount given secrets as a volume in Kong container to override default certs and keys. | `[]` |
|
||||
| securityContext | Set the securityContext for Kong Pods | `{}` |
|
||||
| containerSecurityContext | Set the securityContext for Containers | `{}` |
|
||||
| containerSecurityContext | Set the securityContext for Containers | See values.yaml |
|
||||
| serviceMonitor.enabled | Create ServiceMonitor for Prometheus Operator | `false` |
|
||||
| serviceMonitor.interval | Scraping interval | `30s` |
|
||||
| serviceMonitor.namespace | Where to create ServiceMonitor | |
|
||||
@@ -929,7 +1034,7 @@ If you have paid for a license, but you do not have a copy of yours, please
|
||||
contact Kong Support. Once you have it, you will need to store it in a Secret:
|
||||
|
||||
```bash
|
||||
$ kubectl create secret generic kong-enterprise-license --from-file=license=./license.json
|
||||
kubectl create secret generic kong-enterprise-license --from-file=license=./license.json
|
||||
```
|
||||
|
||||
Set the secret name in `values.yaml`, in the `.enterprise.license_secret` key.
|
||||
@@ -947,7 +1052,7 @@ from \<your username\> \> Edit Profile \> API Key. Use this to create registry
|
||||
secrets:
|
||||
|
||||
```bash
|
||||
$ kubectl create secret docker-registry kong-enterprise-edition-docker \
|
||||
kubectl create secret docker-registry kong-enterprise-edition-docker \
|
||||
--docker-server=hub.docker.io \
|
||||
--docker-username=<username-provided-to-you> \
|
||||
--docker-password=<password-provided-to-you>
|
||||
@@ -965,7 +1070,7 @@ must know where other Kong services (namely the admin and files APIs) can be
|
||||
accessed in order to function properly. Kong's default behavior for attempting
|
||||
to locate these absent configuration is unlikely to work in common Kubernetes
|
||||
environments. Because of this, you should set each of `admin_gui_url`,
|
||||
`admin_api_uri`, `proxy_url`, `portal_api_url`, `portal_gui_host`, and
|
||||
`admin_gui_api_url`, `proxy_url`, `portal_api_url`, `portal_gui_host`, and
|
||||
`portal_gui_protocol` under the `.env` key in values.yaml to locations where
|
||||
each of their respective services can be accessed to ensure that Kong services
|
||||
can locate one another and properly set CORS headers. See the
|
||||
@@ -1023,14 +1128,30 @@ whereas this is optional for the Developer Portal on versions 0.36+. Providing
|
||||
Portal session configuration in values.yaml provides the default session
|
||||
configuration, which can be overridden on a per-workspace basis.
|
||||
|
||||
```bash
|
||||
cat admin_gui_session_conf
|
||||
```
|
||||
$ cat admin_gui_session_conf
|
||||
|
||||
```json
|
||||
{"cookie_name":"admin_session","cookie_samesite":"off","secret":"admin-secret-CHANGEME","cookie_secure":true,"storage":"kong"}
|
||||
$ cat portal_session_conf
|
||||
```
|
||||
|
||||
```bash
|
||||
cat portal_session_conf
|
||||
```
|
||||
|
||||
```json
|
||||
{"cookie_name":"portal_session","cookie_samesite":"off","secret":"portal-secret-CHANGEME","cookie_secure":true,"storage":"kong"}
|
||||
$ kubectl create secret generic kong-session-config --from-file=admin_gui_session_conf --from-file=portal_session_conf
|
||||
```
|
||||
|
||||
```bash
|
||||
kubectl create secret generic kong-session-config --from-file=admin_gui_session_conf --from-file=portal_session_conf
|
||||
```
|
||||
|
||||
```bash
|
||||
secret/kong-session-config created
|
||||
```
|
||||
|
||||
The exact plugin settings may vary in your environment. The `secret` should
|
||||
always be changed for both configurations.
|
||||
|
||||
@@ -1081,6 +1202,28 @@ admin:
|
||||
enable-metrics: "true"
|
||||
```
|
||||
|
||||
## Argo CD Considerations
|
||||
|
||||
The built-in database subchart (`postgresql.enabled` in values) is not
|
||||
supported when installing the chart via Argo CD.
|
||||
|
||||
Argo CD does not support the full Helm lifecycle. There is no distinction
|
||||
between the initial install and upgrades. Both operations are a "sync" in Argo
|
||||
terms. This affects when migration Jobs execute in database-backed Kong
|
||||
installs.
|
||||
|
||||
The chart sets the `Sync` and `BeforeHookCreation` deletion
|
||||
[hook policies](https://argo-cd.readthedocs.io/en/stable/user-guide/resource_hooks/)
|
||||
on the `init-migrations` and `pre-upgrade-migrations` Jobs.
|
||||
|
||||
The `pre-upgrade-migrations` Job normally uses Helm's `pre-upgrade` policy. Argo
|
||||
translates this to its `PreSync` policy, which would create the Job before all
|
||||
sync phase resources. Doing this before various sync phase resources (such as
|
||||
the ServiceAccount) are in place would prevent the Job from running
|
||||
successfully. Overriding this with Argo's `Sync` policy starts the Job at the
|
||||
same time as the upgraded Deployment Pods. The new Pods may fail to start
|
||||
temporarily, but will eventually start normally once migrations complete.
|
||||
|
||||
## Seeking help
|
||||
|
||||
If you run into an issue, bug or have a question, please reach out to the Kong
|
||||
|
||||
@@ -17,6 +17,8 @@ upgrading from a previous version.
|
||||
## Table of contents
|
||||
|
||||
- [Upgrade considerations for all versions](#upgrade-considerations-for-all-versions)
|
||||
- [2.26.0](#2260)
|
||||
- [2.19.0](#2190)
|
||||
- [2.13.0](#2130)
|
||||
- [2.8.0](#280)
|
||||
- [2.7.0](#270)
|
||||
@@ -82,6 +84,55 @@ https://raw.githubusercontent.com/Kong/charts/kong-<version>/charts/kong/crds/cu
|
||||
For example, if your release is 2.6.4, you would apply
|
||||
`https://raw.githubusercontent.com/Kong/charts/kong-2.6.4/charts/kong/crds/custom-resource-definitions.yaml`.
|
||||
|
||||
## 2.26.0
|
||||
|
||||
If you are using controller version 2.10 or lower and proxy version 3.3 or
|
||||
higher in separate Deployments (such as when using the `ingress` chart), proxy
|
||||
Pods will not become ready unless you override the default readiness endpoint:
|
||||
|
||||
```
|
||||
readinessProbe:
|
||||
httpGet:
|
||||
path: /status
|
||||
```
|
||||
|
||||
This section goes under the `gateway` section when using the `ingress` chart.
|
||||
|
||||
2.26 changes the default proxy readiness endpoint to the `/status/ready`
|
||||
endpoint introduced in Kong 3.3. This endpoint reports true when Kong has
|
||||
configuration available, whereas the previous `/status` endpoint returned true
|
||||
immediately after start, and could result in proxy instances attempting to
|
||||
serve requests before they had configuration.
|
||||
|
||||
The chart has logic to fall back to the older endpoint if the proxy and
|
||||
controller versions do not work well with the new endpoint. However, the chart
|
||||
detection cannot determine the controller version when the controller is in a
|
||||
separate Deployment, and will always use the new endpoint if the Kong image
|
||||
version is 3.3 or higher.
|
||||
|
||||
Kong recommends Kong 3.3 and higher users update to controller 2.11 at their
|
||||
earliest convenience to take advantage of the improved readiness behavior.
|
||||
|
||||
## 2.19.0
|
||||
|
||||
2.19 sets a default [security context](https://kubernetes.io/docs/tasks/configure-pod-container/security-context/)
|
||||
that declares a read-only root filesystem for Kong containers. The base Kong and KIC
|
||||
images are compatible with this setting. The chart mounts temporary writeable
|
||||
emptyDir filesystems for locations that require writeable files (`/tmp` and
|
||||
`/kong_prefix/`).
|
||||
|
||||
This setting limit attack surface and should be compatible with most
|
||||
installations. However, if you use custom plugins that write to disk, you must
|
||||
either mount a writeable emptyDir for them or override the new defaults by
|
||||
setting:
|
||||
|
||||
```
|
||||
containerSecurityContext:
|
||||
readOnlyRootFilesystem: false
|
||||
```
|
||||
|
||||
in your values.yaml.
|
||||
|
||||
## 2.13.0
|
||||
|
||||
2.13.0 includes updated CRDs. You must [apply these manually](#updates-to-crds)
|
||||
@@ -142,7 +193,7 @@ database](https://www.postgresql.org/docs/current/backup-dump.html) and
|
||||
creating a separate release if you wish to continue using 8.6.8:
|
||||
|
||||
```
|
||||
$ helm install my-release -f values.yaml --version 8.6.8 bitnami/postgresql
|
||||
helm install my-release -f values.yaml --version 8.6.8 bitnami/postgresql
|
||||
```
|
||||
|
||||
Afterwords, you will upgrade your Kong chart release with
|
||||
@@ -182,26 +233,28 @@ upgrade in multiple steps:
|
||||
First, pin the controller version and upgrade to chart 2.4.0:
|
||||
|
||||
```console
|
||||
$ helm upgrade --wait \
|
||||
helm upgrade --wait \
|
||||
--set ingressController.image.tag=<CURRENT_CONTROLLER_VERSION> \
|
||||
--version 2.4.0 \
|
||||
--namespace <YOUR_RELEASE_NAMESPACE> \
|
||||
<YOUR_RELEASE_NAME> kong/kong
|
||||
```
|
||||
|
||||
Second, temporarily disable the ingress controller:
|
||||
|
||||
```console
|
||||
$ helm upgrade --wait \
|
||||
helm upgrade --wait \
|
||||
--set ingressController.enabled=false \
|
||||
--set deployment.serviceaccount.create=true \
|
||||
--version 2.4.0 \
|
||||
--namespace <YOUR_RELEASE_NAMESPACE> \
|
||||
<YOUR_RELEASE_NAME> kong/kong
|
||||
```
|
||||
|
||||
Finally, re-enable the ingress controller at the new version:
|
||||
|
||||
```console
|
||||
$ helm upgrade --wait \
|
||||
helm upgrade --wait \
|
||||
--set ingressController.enabled=true \
|
||||
--set ingressController.image.tag=<NEW_CONTROLLER_VERSION> \
|
||||
--version 2.4.0 \
|
||||
|
||||
@@ -0,0 +1,18 @@
|
||||
admin:
|
||||
enabled: true
|
||||
type: ClusterIP
|
||||
|
||||
# Stub config to make the instance become ready
|
||||
dblessConfig:
|
||||
config: |
|
||||
_format_version: "1.1"
|
||||
services:
|
||||
- name: example.com
|
||||
url: http://example.com
|
||||
routes:
|
||||
- name: example
|
||||
paths:
|
||||
- "/example"
|
||||
|
||||
ingressController:
|
||||
enabled: false
|
||||
@@ -1,6 +1,3 @@
|
||||
|
||||
# install chart with some extra labels
|
||||
|
||||
extraLabels:
|
||||
acme.com/some-key: some-value
|
||||
|
||||
@@ -1,7 +1,4 @@
|
||||
# install chart with default values
|
||||
proxy:
|
||||
type: NodePort
|
||||
|
||||
env:
|
||||
anonymous_reports: "off"
|
||||
ingressController:
|
||||
|
||||
@@ -0,0 +1,15 @@
|
||||
# CI test for empty hostname including tls secret using string
|
||||
proxy:
|
||||
ingress:
|
||||
enabled: true
|
||||
tls: "kong.proxy.example.secret"
|
||||
|
||||
extraObjects:
|
||||
- apiVersion: v1
|
||||
data:
|
||||
tls.crt: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSURoakNDQW00Q0NRQ0tyTDdSS1Y0NTBEQU5CZ2txaGtpRzl3MEJBUXNGQURDQmhERUxNQWtHQTFVRUJoTUMKV0ZneEVqQVFCZ05WQkFnTUNWTjBZWFJsVG1GdFpURVJNQThHQTFVRUJ3d0lRMmwwZVU1aGJXVXhGREFTQmdOVgpCQW9NQzBOdmJYQmhibmxPWVcxbE1Sc3dHUVlEVlFRTERCSkRiMjF3WVc1NVUyVmpkR2x2Yms1aGJXVXhHekFaCkJnTlZCQU1NRW5CeWIzaDVMbXR2Ym1jdVpYaGhiWEJzWlRBZUZ3MHlNekEyTWprd09ERTBNekJhRncwek16QTIKTWpZd09ERTBNekJhTUlHRU1Rc3dDUVlEVlFRR0V3SllXREVTTUJBR0ExVUVDQXdKVTNSaGRHVk9ZVzFsTVJFdwpEd1lEVlFRSERBaERhWFI1VG1GdFpURVVNQklHQTFVRUNnd0xRMjl0Y0dGdWVVNWhiV1V4R3pBWkJnTlZCQXNNCkVrTnZiWEJoYm5sVFpXTjBhVzl1VG1GdFpURWJNQmtHQTFVRUF3d1NjSEp2ZUhrdWEyOXVaeTVsZUdGdGNHeGwKTUlJQklqQU5CZ2txaGtpRzl3MEJBUUVGQUFPQ0FROEFNSUlCQ2dLQ0FRRUE4Wmd4czI1RXdtaXRsRG1HMitWVwpscUZ4R3lkVHU2dWlCVldFZjNoV0h2R3YvUWpYZHBBWXlkc3ZpNS92b1FtcjNUeVJBb3VaR1lCR3RuVEF0cU5rCnFLUmFVaWppVlN3TTNzeUl1cHluMlRjSjk1N2RLUCtUYTRaL0VNUlRwSCtya1psV01LNVYrNUszTmFIL21leDUKVWRRWkl4WUxNM0xIM0t0cmt2OWZRNlhSZ2dkeXo0MEt2YUV6SW1scEVoQnBoS0g5UWJiL3RFRE0vdFFqbC9FUApmbUF5M2Y5WE1uRDNSeFY3TnFrZktpUjNXZ1JDMnFyNWtPbXlJTGp1YWxERk1Zb3lDZUlmSnd1WmVDaEpGb3ZHClFKUFY2WU9xTG5aRWN3MU9BaVBXQnMycXVmWmlsNXplekRDZUFGZDV3eXVrS1dPZ3pTZ3Q2VzZvN2FBRTBDK3YKclFJREFRQUJNQTBHQ1NxR1NJYjNEUUVCQ3dVQUE0SUJBUUNGZHhFOFVsMVorcWxBbW1lTk5BdlAyZVVxSElTbQpHWXZidzdGdW82bXNJY3V3cjZKeENBWjIwako5UkphalMzWS9TS3BteXM2OXZxU21ic25oeUJzc01mL1ZtenFSClBVLzVkUUZiblNybUJqMnFBNWxtRCtENDVLUEtrTjc1V21NeDRQWkZseEw3WHVLYnZhYVZBUjFFUmRNZy90NisKUXpPV3BVWVZrcFJnQmlxTDBTTjhvTStOTjdScGFESFNkZjlTY1FtUmhNVklNNDdVZ1ZXNWhta21mQjBkUTFhQQo5NWdTQ3E0cGVwUFRzY3NsbVBzM0lOck5BTk45KytyMnM1bXRTWnp5VktRU0cwRjQ0Y1puWjdTdkdTVFJORDlUCnRKVzNTcko3elBwS0JqWi9qVDRRVnpBdGtHN3FSV2ZhYnlWTmVrK29wMTgwSVY5Um9IR1JDU0kyCi0tLS0tRU5EIENFUlRJRklDQVRFLS0tLS0K
|
||||
tls.key: LS0tLS1CRUdJTiBQUklWQVRFIEtFWS0tLS0tCk1JSUV2Z0lCQURBTkJna3Foa2lHOXcwQkFRRUZBQVNDQktnd2dnU2tBZ0VBQW9JQkFRRHhtREd6YmtUQ2FLMlUKT1liYjVWYVdvWEViSjFPN3E2SUZWWVIvZUZZZThhLzlDTmQya0JqSjJ5K0xuKytoQ2F2ZFBKRUNpNWtaZ0VhMgpkTUMybzJTb3BGcFNLT0pWTEF6ZXpJaTZuS2ZaTnduM250MG8vNU5yaG44UXhGT2tmNnVSbVZZd3JsWDdrcmMxCm9mK1o3SGxSMUJrakZnc3pjc2ZjcTJ1Uy8xOURwZEdDQjNMUGpRcTlvVE1pYVdrU0VHbUVvZjFCdHYrMFFNeisKMUNPWDhROStZRExkLzFjeWNQZEhGWHMycVI4cUpIZGFCRUxhcXZtUTZiSWd1TzVxVU1VeGlqSUo0aDhuQzVsNApLRWtXaThaQWs5WHBnNm91ZGtSekRVNENJOVlHemFxNTltS1huTjdNTUo0QVYzbkRLNlFwWTZETktDM3BicWp0Cm9BVFFMNit0QWdNQkFBRUNnZ0VCQUs3N1I0d3BJcDRZU1JoaGJoN1loWldHQ3JEYkZCZUtZVWd4djB5LzhNaHEKenNlYlhzdGQ1TVpXL2FISVRqdzZFQU9tT1hVNWZNTHVtTWpQMlVDdktWbkg2QzgzczI1ekFFTmlxdWxXUzIvVgpJRi83N1Qwamx6ZTY2MDlPa3pKQzBoWWJsRVNnRUdDc3pBdUpjT0tnVnVLQWwxQkZTQW1VYWRPWFNNdm9NS3lDCkJlekZaVEhOcGRWQ2xwUHVLNGQrWFJJZ1hHWS84RzNmWlFXRWNjV2tTYmRjQUlLdVYvWktHQ0IyT2dXS1VzSHgKTStscEw1TTZ3aXdYOEFNdUVWVHJsMWNwKzAzTjdOaUYwMFpYdCszZzVZUkJmRitYWjZ1b3hmbENQZ3VHdzh6bgpvN2tFRVNKZ2YycHZyZWYveHBjSVFSM090aHZjSzR5RldOcndPbExHQk9FQ2dZRUErNmJBREF0bDAvRlpzV08zCnVvNlBRNXZTL0tqbS9XaUkzeUo5TUdLNzQxTFZpMlRMUGpVZ092SDdkZUVjNVJjUmoxV1Nna3d1bUdzZWE2WkQKWXRWSTRZTDdMM1NUQ3JyZUNFTDRhOUJPcFB0azcxWWw3TmhxZktEaXhzU1FnNmt4dDJ1TlYvZXNSQ1JPeENoWgp5bk9JTmkvN3lOeFpVek4zcndyVjBCMUFNYVVDZ1lFQTljVDBZNkJWRHZLdFFaV1gvR1REZ2pUUzN6QWlPWmFNCjVFM3NleHh6MXY4eDF0N3JvWDV3aHNaVjlzQ05nNlJaNjIyT3hJejhHQnVvMnU1M2h2WFJabmdDaG1PcHYwRjgKcm5STWFNR0tIeGN2TmNrVUZUMW9TdDJCeEhNT1FNZTM2cERVTnZ0S3pvNGJoakpVUU94Mm14RU9TNERscm4rMApRU3FqVFpyWGwya0NnWUJ1UmIyMkNYQ1BsUjBHbkhtd0tEUWpIaTh3UkJza1JDQm1Gc2pnNFFNUU5BWWJWUW15CnNyankyNEtqUHdmWVkybHdjOEVGazdoL1ZjRTR6dHlNZklXNVBCb3h5MVY3eURMdlQ5bG45Um5oTmNBZkdKTDUKM0VPZFpTcTZpdndBbGEyUmdIR3BjSUJ1UTdLNFJpNUNocW5UaE9kQ056eDFOd0psRTh4cHE4ZXJlUUtCZ1FEeQppV3B3UXRLT0ROa0VCdi9WT1E5am1JT2RjOS9pbXZyeGR5RHZvWFdENzVXY3FhTTVYUkRwUUNPbmZnQnBzREI0CjBFWjdHM0xReThNSVF4czcyYXpMaFpWZ1VFdzlEUUJoSFM0bWx4Q2FmQU8vL1c3UFF5bC84RGJXeW9CL1YxamQKcUExMU1PcHpDdlNJcTNSUUdjczJYaytRSFdVTW5zUWhKMVcvQ1JiSE9RS0JnRTVQZ0hrbW1PY1VXZkJBZUtzTApvb2FNNzBINVN1YUNYN1Y1enBhM3hFMW5WVWMxend5aldOdkdWbTA5WkpEOFFMR1ZDV2U0R1o5R1NvV2tqSUMvCklFKzA0M29kUERuL2JwSDlTMDF2a0s1ZDRJSGc3QUcwWXI5SW1zS0paT0djT1dmdUdKSlZ5em1CRXhaSU9pbnoKVFFuaFdhZWs0NE1hdVJYOC9pRjZyZWorCi0tLS0tRU5EIFBSSVZBVEUgS0VZLS0tLS0K
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: kong.proxy.example.secret
|
||||
type: kubernetes.io/tls
|
||||
@@ -0,0 +1,16 @@
|
||||
# CI test for hostname including tls secret using string
|
||||
proxy:
|
||||
ingress:
|
||||
enabled: true
|
||||
hostname: "proxy.kong.example"
|
||||
tls: "kong.proxy.example.secret"
|
||||
|
||||
extraObjects:
|
||||
- apiVersion: v1
|
||||
data:
|
||||
tls.crt: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSURoakNDQW00Q0NRQ0tyTDdSS1Y0NTBEQU5CZ2txaGtpRzl3MEJBUXNGQURDQmhERUxNQWtHQTFVRUJoTUMKV0ZneEVqQVFCZ05WQkFnTUNWTjBZWFJsVG1GdFpURVJNQThHQTFVRUJ3d0lRMmwwZVU1aGJXVXhGREFTQmdOVgpCQW9NQzBOdmJYQmhibmxPWVcxbE1Sc3dHUVlEVlFRTERCSkRiMjF3WVc1NVUyVmpkR2x2Yms1aGJXVXhHekFaCkJnTlZCQU1NRW5CeWIzaDVMbXR2Ym1jdVpYaGhiWEJzWlRBZUZ3MHlNekEyTWprd09ERTBNekJhRncwek16QTIKTWpZd09ERTBNekJhTUlHRU1Rc3dDUVlEVlFRR0V3SllXREVTTUJBR0ExVUVDQXdKVTNSaGRHVk9ZVzFsTVJFdwpEd1lEVlFRSERBaERhWFI1VG1GdFpURVVNQklHQTFVRUNnd0xRMjl0Y0dGdWVVNWhiV1V4R3pBWkJnTlZCQXNNCkVrTnZiWEJoYm5sVFpXTjBhVzl1VG1GdFpURWJNQmtHQTFVRUF3d1NjSEp2ZUhrdWEyOXVaeTVsZUdGdGNHeGwKTUlJQklqQU5CZ2txaGtpRzl3MEJBUUVGQUFPQ0FROEFNSUlCQ2dLQ0FRRUE4Wmd4czI1RXdtaXRsRG1HMitWVwpscUZ4R3lkVHU2dWlCVldFZjNoV0h2R3YvUWpYZHBBWXlkc3ZpNS92b1FtcjNUeVJBb3VaR1lCR3RuVEF0cU5rCnFLUmFVaWppVlN3TTNzeUl1cHluMlRjSjk1N2RLUCtUYTRaL0VNUlRwSCtya1psV01LNVYrNUszTmFIL21leDUKVWRRWkl4WUxNM0xIM0t0cmt2OWZRNlhSZ2dkeXo0MEt2YUV6SW1scEVoQnBoS0g5UWJiL3RFRE0vdFFqbC9FUApmbUF5M2Y5WE1uRDNSeFY3TnFrZktpUjNXZ1JDMnFyNWtPbXlJTGp1YWxERk1Zb3lDZUlmSnd1WmVDaEpGb3ZHClFKUFY2WU9xTG5aRWN3MU9BaVBXQnMycXVmWmlsNXplekRDZUFGZDV3eXVrS1dPZ3pTZ3Q2VzZvN2FBRTBDK3YKclFJREFRQUJNQTBHQ1NxR1NJYjNEUUVCQ3dVQUE0SUJBUUNGZHhFOFVsMVorcWxBbW1lTk5BdlAyZVVxSElTbQpHWXZidzdGdW82bXNJY3V3cjZKeENBWjIwako5UkphalMzWS9TS3BteXM2OXZxU21ic25oeUJzc01mL1ZtenFSClBVLzVkUUZiblNybUJqMnFBNWxtRCtENDVLUEtrTjc1V21NeDRQWkZseEw3WHVLYnZhYVZBUjFFUmRNZy90NisKUXpPV3BVWVZrcFJnQmlxTDBTTjhvTStOTjdScGFESFNkZjlTY1FtUmhNVklNNDdVZ1ZXNWhta21mQjBkUTFhQQo5NWdTQ3E0cGVwUFRzY3NsbVBzM0lOck5BTk45KytyMnM1bXRTWnp5VktRU0cwRjQ0Y1puWjdTdkdTVFJORDlUCnRKVzNTcko3elBwS0JqWi9qVDRRVnpBdGtHN3FSV2ZhYnlWTmVrK29wMTgwSVY5Um9IR1JDU0kyCi0tLS0tRU5EIENFUlRJRklDQVRFLS0tLS0K
|
||||
tls.key: LS0tLS1CRUdJTiBQUklWQVRFIEtFWS0tLS0tCk1JSUV2Z0lCQURBTkJna3Foa2lHOXcwQkFRRUZBQVNDQktnd2dnU2tBZ0VBQW9JQkFRRHhtREd6YmtUQ2FLMlUKT1liYjVWYVdvWEViSjFPN3E2SUZWWVIvZUZZZThhLzlDTmQya0JqSjJ5K0xuKytoQ2F2ZFBKRUNpNWtaZ0VhMgpkTUMybzJTb3BGcFNLT0pWTEF6ZXpJaTZuS2ZaTnduM250MG8vNU5yaG44UXhGT2tmNnVSbVZZd3JsWDdrcmMxCm9mK1o3SGxSMUJrakZnc3pjc2ZjcTJ1Uy8xOURwZEdDQjNMUGpRcTlvVE1pYVdrU0VHbUVvZjFCdHYrMFFNeisKMUNPWDhROStZRExkLzFjeWNQZEhGWHMycVI4cUpIZGFCRUxhcXZtUTZiSWd1TzVxVU1VeGlqSUo0aDhuQzVsNApLRWtXaThaQWs5WHBnNm91ZGtSekRVNENJOVlHemFxNTltS1huTjdNTUo0QVYzbkRLNlFwWTZETktDM3BicWp0Cm9BVFFMNit0QWdNQkFBRUNnZ0VCQUs3N1I0d3BJcDRZU1JoaGJoN1loWldHQ3JEYkZCZUtZVWd4djB5LzhNaHEKenNlYlhzdGQ1TVpXL2FISVRqdzZFQU9tT1hVNWZNTHVtTWpQMlVDdktWbkg2QzgzczI1ekFFTmlxdWxXUzIvVgpJRi83N1Qwamx6ZTY2MDlPa3pKQzBoWWJsRVNnRUdDc3pBdUpjT0tnVnVLQWwxQkZTQW1VYWRPWFNNdm9NS3lDCkJlekZaVEhOcGRWQ2xwUHVLNGQrWFJJZ1hHWS84RzNmWlFXRWNjV2tTYmRjQUlLdVYvWktHQ0IyT2dXS1VzSHgKTStscEw1TTZ3aXdYOEFNdUVWVHJsMWNwKzAzTjdOaUYwMFpYdCszZzVZUkJmRitYWjZ1b3hmbENQZ3VHdzh6bgpvN2tFRVNKZ2YycHZyZWYveHBjSVFSM090aHZjSzR5RldOcndPbExHQk9FQ2dZRUErNmJBREF0bDAvRlpzV08zCnVvNlBRNXZTL0tqbS9XaUkzeUo5TUdLNzQxTFZpMlRMUGpVZ092SDdkZUVjNVJjUmoxV1Nna3d1bUdzZWE2WkQKWXRWSTRZTDdMM1NUQ3JyZUNFTDRhOUJPcFB0azcxWWw3TmhxZktEaXhzU1FnNmt4dDJ1TlYvZXNSQ1JPeENoWgp5bk9JTmkvN3lOeFpVek4zcndyVjBCMUFNYVVDZ1lFQTljVDBZNkJWRHZLdFFaV1gvR1REZ2pUUzN6QWlPWmFNCjVFM3NleHh6MXY4eDF0N3JvWDV3aHNaVjlzQ05nNlJaNjIyT3hJejhHQnVvMnU1M2h2WFJabmdDaG1PcHYwRjgKcm5STWFNR0tIeGN2TmNrVUZUMW9TdDJCeEhNT1FNZTM2cERVTnZ0S3pvNGJoakpVUU94Mm14RU9TNERscm4rMApRU3FqVFpyWGwya0NnWUJ1UmIyMkNYQ1BsUjBHbkhtd0tEUWpIaTh3UkJza1JDQm1Gc2pnNFFNUU5BWWJWUW15CnNyankyNEtqUHdmWVkybHdjOEVGazdoL1ZjRTR6dHlNZklXNVBCb3h5MVY3eURMdlQ5bG45Um5oTmNBZkdKTDUKM0VPZFpTcTZpdndBbGEyUmdIR3BjSUJ1UTdLNFJpNUNocW5UaE9kQ056eDFOd0psRTh4cHE4ZXJlUUtCZ1FEeQppV3B3UXRLT0ROa0VCdi9WT1E5am1JT2RjOS9pbXZyeGR5RHZvWFdENzVXY3FhTTVYUkRwUUNPbmZnQnBzREI0CjBFWjdHM0xReThNSVF4czcyYXpMaFpWZ1VFdzlEUUJoSFM0bWx4Q2FmQU8vL1c3UFF5bC84RGJXeW9CL1YxamQKcUExMU1PcHpDdlNJcTNSUUdjczJYaytRSFdVTW5zUWhKMVcvQ1JiSE9RS0JnRTVQZ0hrbW1PY1VXZkJBZUtzTApvb2FNNzBINVN1YUNYN1Y1enBhM3hFMW5WVWMxend5aldOdkdWbTA5WkpEOFFMR1ZDV2U0R1o5R1NvV2tqSUMvCklFKzA0M29kUERuL2JwSDlTMDF2a0s1ZDRJSGc3QUcwWXI5SW1zS0paT0djT1dmdUdKSlZ5em1CRXhaSU9pbnoKVFFuaFdhZWs0NE1hdVJYOC9pRjZyZWorCi0tLS0tRU5EIFBSSVZBVEUgS0VZLS0tLS0K
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: kong.proxy.example.secret
|
||||
type: kubernetes.io/tls
|
||||
@@ -0,0 +1,9 @@
|
||||
# CI test for using ingress hosts configuration
|
||||
proxy:
|
||||
ingress:
|
||||
enabled: true
|
||||
hosts:
|
||||
- host: proxy.kong.example
|
||||
paths:
|
||||
- path: /
|
||||
pathType: ImplementationSpecific
|
||||
@@ -0,0 +1,42 @@
|
||||
# CI test for testing combined ingress hostname and hosts configuration including tls configuraion using slice
|
||||
proxy:
|
||||
ingress:
|
||||
enabled: true
|
||||
hostname: "proxy.kong.example"
|
||||
hosts:
|
||||
- host: "proxy2.kong.example"
|
||||
paths:
|
||||
- path: /foo
|
||||
pathType: Prefix
|
||||
- path: /bar
|
||||
pathType: Prefix
|
||||
- host: "proxy3.kong.example"
|
||||
paths:
|
||||
- path: /baz
|
||||
pathType: Prefix
|
||||
tls:
|
||||
- hosts:
|
||||
- "proxy.kong.example"
|
||||
secretName: "proxy.kong.example.secret"
|
||||
- hosts:
|
||||
- "proxy2.kong.example"
|
||||
- "proxy3.kong.example"
|
||||
secretName: "proxy.kong.example.secret2"
|
||||
|
||||
extraObjects:
|
||||
- apiVersion: v1
|
||||
data:
|
||||
tls.crt: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSURoakNDQW00Q0NRQ0tyTDdSS1Y0NTBEQU5CZ2txaGtpRzl3MEJBUXNGQURDQmhERUxNQWtHQTFVRUJoTUMKV0ZneEVqQVFCZ05WQkFnTUNWTjBZWFJsVG1GdFpURVJNQThHQTFVRUJ3d0lRMmwwZVU1aGJXVXhGREFTQmdOVgpCQW9NQzBOdmJYQmhibmxPWVcxbE1Sc3dHUVlEVlFRTERCSkRiMjF3WVc1NVUyVmpkR2x2Yms1aGJXVXhHekFaCkJnTlZCQU1NRW5CeWIzaDVMbXR2Ym1jdVpYaGhiWEJzWlRBZUZ3MHlNekEyTWprd09ERTBNekJhRncwek16QTIKTWpZd09ERTBNekJhTUlHRU1Rc3dDUVlEVlFRR0V3SllXREVTTUJBR0ExVUVDQXdKVTNSaGRHVk9ZVzFsTVJFdwpEd1lEVlFRSERBaERhWFI1VG1GdFpURVVNQklHQTFVRUNnd0xRMjl0Y0dGdWVVNWhiV1V4R3pBWkJnTlZCQXNNCkVrTnZiWEJoYm5sVFpXTjBhVzl1VG1GdFpURWJNQmtHQTFVRUF3d1NjSEp2ZUhrdWEyOXVaeTVsZUdGdGNHeGwKTUlJQklqQU5CZ2txaGtpRzl3MEJBUUVGQUFPQ0FROEFNSUlCQ2dLQ0FRRUE4Wmd4czI1RXdtaXRsRG1HMitWVwpscUZ4R3lkVHU2dWlCVldFZjNoV0h2R3YvUWpYZHBBWXlkc3ZpNS92b1FtcjNUeVJBb3VaR1lCR3RuVEF0cU5rCnFLUmFVaWppVlN3TTNzeUl1cHluMlRjSjk1N2RLUCtUYTRaL0VNUlRwSCtya1psV01LNVYrNUszTmFIL21leDUKVWRRWkl4WUxNM0xIM0t0cmt2OWZRNlhSZ2dkeXo0MEt2YUV6SW1scEVoQnBoS0g5UWJiL3RFRE0vdFFqbC9FUApmbUF5M2Y5WE1uRDNSeFY3TnFrZktpUjNXZ1JDMnFyNWtPbXlJTGp1YWxERk1Zb3lDZUlmSnd1WmVDaEpGb3ZHClFKUFY2WU9xTG5aRWN3MU9BaVBXQnMycXVmWmlsNXplekRDZUFGZDV3eXVrS1dPZ3pTZ3Q2VzZvN2FBRTBDK3YKclFJREFRQUJNQTBHQ1NxR1NJYjNEUUVCQ3dVQUE0SUJBUUNGZHhFOFVsMVorcWxBbW1lTk5BdlAyZVVxSElTbQpHWXZidzdGdW82bXNJY3V3cjZKeENBWjIwako5UkphalMzWS9TS3BteXM2OXZxU21ic25oeUJzc01mL1ZtenFSClBVLzVkUUZiblNybUJqMnFBNWxtRCtENDVLUEtrTjc1V21NeDRQWkZseEw3WHVLYnZhYVZBUjFFUmRNZy90NisKUXpPV3BVWVZrcFJnQmlxTDBTTjhvTStOTjdScGFESFNkZjlTY1FtUmhNVklNNDdVZ1ZXNWhta21mQjBkUTFhQQo5NWdTQ3E0cGVwUFRzY3NsbVBzM0lOck5BTk45KytyMnM1bXRTWnp5VktRU0cwRjQ0Y1puWjdTdkdTVFJORDlUCnRKVzNTcko3elBwS0JqWi9qVDRRVnpBdGtHN3FSV2ZhYnlWTmVrK29wMTgwSVY5Um9IR1JDU0kyCi0tLS0tRU5EIENFUlRJRklDQVRFLS0tLS0K
|
||||
tls.key: LS0tLS1CRUdJTiBQUklWQVRFIEtFWS0tLS0tCk1JSUV2Z0lCQURBTkJna3Foa2lHOXcwQkFRRUZBQVNDQktnd2dnU2tBZ0VBQW9JQkFRRHhtREd6YmtUQ2FLMlUKT1liYjVWYVdvWEViSjFPN3E2SUZWWVIvZUZZZThhLzlDTmQya0JqSjJ5K0xuKytoQ2F2ZFBKRUNpNWtaZ0VhMgpkTUMybzJTb3BGcFNLT0pWTEF6ZXpJaTZuS2ZaTnduM250MG8vNU5yaG44UXhGT2tmNnVSbVZZd3JsWDdrcmMxCm9mK1o3SGxSMUJrakZnc3pjc2ZjcTJ1Uy8xOURwZEdDQjNMUGpRcTlvVE1pYVdrU0VHbUVvZjFCdHYrMFFNeisKMUNPWDhROStZRExkLzFjeWNQZEhGWHMycVI4cUpIZGFCRUxhcXZtUTZiSWd1TzVxVU1VeGlqSUo0aDhuQzVsNApLRWtXaThaQWs5WHBnNm91ZGtSekRVNENJOVlHemFxNTltS1huTjdNTUo0QVYzbkRLNlFwWTZETktDM3BicWp0Cm9BVFFMNit0QWdNQkFBRUNnZ0VCQUs3N1I0d3BJcDRZU1JoaGJoN1loWldHQ3JEYkZCZUtZVWd4djB5LzhNaHEKenNlYlhzdGQ1TVpXL2FISVRqdzZFQU9tT1hVNWZNTHVtTWpQMlVDdktWbkg2QzgzczI1ekFFTmlxdWxXUzIvVgpJRi83N1Qwamx6ZTY2MDlPa3pKQzBoWWJsRVNnRUdDc3pBdUpjT0tnVnVLQWwxQkZTQW1VYWRPWFNNdm9NS3lDCkJlekZaVEhOcGRWQ2xwUHVLNGQrWFJJZ1hHWS84RzNmWlFXRWNjV2tTYmRjQUlLdVYvWktHQ0IyT2dXS1VzSHgKTStscEw1TTZ3aXdYOEFNdUVWVHJsMWNwKzAzTjdOaUYwMFpYdCszZzVZUkJmRitYWjZ1b3hmbENQZ3VHdzh6bgpvN2tFRVNKZ2YycHZyZWYveHBjSVFSM090aHZjSzR5RldOcndPbExHQk9FQ2dZRUErNmJBREF0bDAvRlpzV08zCnVvNlBRNXZTL0tqbS9XaUkzeUo5TUdLNzQxTFZpMlRMUGpVZ092SDdkZUVjNVJjUmoxV1Nna3d1bUdzZWE2WkQKWXRWSTRZTDdMM1NUQ3JyZUNFTDRhOUJPcFB0azcxWWw3TmhxZktEaXhzU1FnNmt4dDJ1TlYvZXNSQ1JPeENoWgp5bk9JTmkvN3lOeFpVek4zcndyVjBCMUFNYVVDZ1lFQTljVDBZNkJWRHZLdFFaV1gvR1REZ2pUUzN6QWlPWmFNCjVFM3NleHh6MXY4eDF0N3JvWDV3aHNaVjlzQ05nNlJaNjIyT3hJejhHQnVvMnU1M2h2WFJabmdDaG1PcHYwRjgKcm5STWFNR0tIeGN2TmNrVUZUMW9TdDJCeEhNT1FNZTM2cERVTnZ0S3pvNGJoakpVUU94Mm14RU9TNERscm4rMApRU3FqVFpyWGwya0NnWUJ1UmIyMkNYQ1BsUjBHbkhtd0tEUWpIaTh3UkJza1JDQm1Gc2pnNFFNUU5BWWJWUW15CnNyankyNEtqUHdmWVkybHdjOEVGazdoL1ZjRTR6dHlNZklXNVBCb3h5MVY3eURMdlQ5bG45Um5oTmNBZkdKTDUKM0VPZFpTcTZpdndBbGEyUmdIR3BjSUJ1UTdLNFJpNUNocW5UaE9kQ056eDFOd0psRTh4cHE4ZXJlUUtCZ1FEeQppV3B3UXRLT0ROa0VCdi9WT1E5am1JT2RjOS9pbXZyeGR5RHZvWFdENzVXY3FhTTVYUkRwUUNPbmZnQnBzREI0CjBFWjdHM0xReThNSVF4czcyYXpMaFpWZ1VFdzlEUUJoSFM0bWx4Q2FmQU8vL1c3UFF5bC84RGJXeW9CL1YxamQKcUExMU1PcHpDdlNJcTNSUUdjczJYaytRSFdVTW5zUWhKMVcvQ1JiSE9RS0JnRTVQZ0hrbW1PY1VXZkJBZUtzTApvb2FNNzBINVN1YUNYN1Y1enBhM3hFMW5WVWMxend5aldOdkdWbTA5WkpEOFFMR1ZDV2U0R1o5R1NvV2tqSUMvCklFKzA0M29kUERuL2JwSDlTMDF2a0s1ZDRJSGc3QUcwWXI5SW1zS0paT0djT1dmdUdKSlZ5em1CRXhaSU9pbnoKVFFuaFdhZWs0NE1hdVJYOC9pRjZyZWorCi0tLS0tRU5EIFBSSVZBVEUgS0VZLS0tLS0K
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: kong.proxy.example.secret
|
||||
type: kubernetes.io/tls
|
||||
- apiVersion: v1
|
||||
data:
|
||||
tls.crt: LS0tLS1CRUdJTiBDRVJUSUZJQ0FURS0tLS0tCk1JSURmakNDQW1ZQ0NRREVtWjF0cnJwaURqQU5CZ2txaGtpRzl3MEJBUXNGQURDQmdERUxNQWtHQTFVRUJoTUMKV0ZneEVqQVFCZ05WQkFnTUNWTjBZWFJsVG1GdFpURVJNQThHQTFVRUJ3d0lRMmwwZVU1aGJXVXhGREFTQmdOVgpCQW9NQzBOdmJYQmhibmxPWVcxbE1Sc3dHUVlEVlFRTERCSkRiMjF3WVc1NVUyVmpkR2x2Yms1aGJXVXhGekFWCkJnTlZCQU1NRGlvdWEyOXVaeTVsZUdGdGNHeGxNQjRYRFRJek1EWXlPVEE0TVRjek4xb1hEVE16TURZeU5qQTQKTVRjek4xb3dnWUF4Q3pBSkJnTlZCQVlUQWxoWU1SSXdFQVlEVlFRSURBbFRkR0YwWlU1aGJXVXhFVEFQQmdOVgpCQWNNQ0VOcGRIbE9ZVzFsTVJRd0VnWURWUVFLREF0RGIyMXdZVzU1VG1GdFpURWJNQmtHQTFVRUN3d1NRMjl0CmNHRnVlVk5sWTNScGIyNU9ZVzFsTVJjd0ZRWURWUVFEREE0cUxtdHZibWN1WlhoaGJYQnNaVENDQVNJd0RRWUoKS29aSWh2Y05BUUVCQlFBRGdnRVBBRENDQVFvQ2dnRUJBTDlSR1g1VytsRW8wcGg2eTJqeHN6TGZOcjMvNlpFOQpPR0pPMGl1WmpwRml2dHBya24ydDlqYTRaNUdYOGh4NUczS1FsRkhrVFBmV01BWmUzdldINTF0alZzYjZwY2UwCjlkMUo4WXNxWkh5RHVlUzBrS3RUbEFmc0F5MnVjL3ZvUUdmOTdZeUI2TlJ4TEJmNHBnSVJ4eHpGM3o0Q1ZOSTgKTzE5Ym1PYVo1Vkk1QWZpbENSMUI1ekxuN2VoeEJHOHhTQmRtQUg0eWFob2t5RXk2a0ZtRzJCaEtJWjdsL1BZYQpqbU1yQ3cwekRVampvblBublZTWTkxL0EwNUJVTVk5OEZsME00QVV5T1V3enBaajhqMXhLMTNqUVlGeXJwUHQwCklHNUdLR044akVCcnRkdGVlcGZIdFZuekFWYnhoT0hkcXZoUWhrSDJDSGVwOStIQkNIL25VL1VDQXdFQUFUQU4KQmdrcWhraUc5dzBCQVFzRkFBT0NBUUVBQkcxVVYyUFRJekhrNEt4cjBHT0NXalhjTTdKUU9hbUJQM3dZSCswRgpyc09YUG9IOHVLV25XYjhSSGE1MDhMenU4MGNzS1lYcnZ4SEhDcmcxdXJjRnl3bnNMaUtMNGhsQklTd2ZMNzFFClVXODhQdGYyWTdjTnJZRzNLc2MvMWVpait1RWd5bVdCbjkraVYzbzE5VERwRjlZZWZwYzNUUDJqMGhNUHcwMlgKa1gzSlh3b250NnBQaDhlQjhXRU1OZkF5NzZmb0lMcytVd0Fjck56QkpjSVZSTERoZWFNMFNFd0xCNUpuaWZ5ZwplRE1aSE56MkhLais0NU1wTzFOSDBtd3ZJRTRLQjNITUNSSlMybmZFbWVMcFdCMWpmZTV6T2o1bWhTeS82M0RVCldDQll1aUhtelFWaGxJS21lQzBlVmd3bGtkMTFrUDRNM1hoWnB6V09aQ1BoaGc9PQotLS0tLUVORCBDRVJUSUZJQ0FURS0tLS0tCg==
|
||||
tls.key: LS0tLS1CRUdJTiBQUklWQVRFIEtFWS0tLS0tCk1JSUV2UUlCQURBTkJna3Foa2lHOXcwQkFRRUZBQVNDQktjd2dnU2pBZ0VBQW9JQkFRQy9VUmwrVnZwUktOS1kKZXN0bzhiTXkzemE5LyttUlBUaGlUdElybVk2UllyN2FhNUo5cmZZMnVHZVJsL0ljZVJ0eWtKUlI1RXozMWpBRwpYdDcxaCtkYlkxYkcrcVhIdFBYZFNmR0xLbVI4Zzdua3RKQ3JVNVFIN0FNdHJuUDc2RUJuL2UyTWdlalVjU3dYCitLWUNFY2NjeGQ4K0FsVFNQRHRmVzVqbW1lVlNPUUg0cFFrZFFlY3k1KzNvY1FSdk1VZ1haZ0IrTW1vYUpNaE0KdXBCWmh0Z1lTaUdlNWZ6MkdvNWpLd3NOTXcxSTQ2Sno1NTFVbVBkZndOT1FWREdQZkJaZERPQUZNamxNTTZXWQovSTljU3RkNDBHQmNxNlQ3ZENCdVJpaGpmSXhBYTdYYlhucVh4N1ZaOHdGVzhZVGgzYXI0VUlaQjlnaDNxZmZoCndRaC81MVAxQWdNQkFBRUNnZ0VCQUlCZ0l3TXJ5ZnY3c0pTd2tSMXlVaFNvdzByckZnZG5WUlppWFpUMERUNXgKVEMrMFR6QVdNMGkwcElxRnN1aDRPM3E4bVVuNkw4dDk1ZXZnYlN2RWJmSmN6alhtcXFjL1BsdW02blcvbEg0WQp4Znc1VFhvcE13Tzkwc1FzYzVkdFdRcHUwWitlN0dUaEsvMUowOXMvb3FRa0FwRFJiNmxDMFhSRE9tNUNoaWFNCi95Z2M2dGUzUHkrRXpzSmRMRm9YWndFQnVQWTB2KzlBclhpNmlUMllaN1ZacE9iZzQxcm1ocHNObTFLNmdJajUKZFZKNGZYa2Z5V0hsSmJBYzVTRDkrVWMrTGFjUEcxSjVJUWx6eTM0WlM0ZG9VQ2lmODZuVHFzSnFVTU1sNXYxcAp3SFFUZFI2MkdnWnRPM1grOU4vdHE3SExqU0tHY0JEd3E4bEM4QXZ0VHdFQ2dZRUErWWpVdzI1em42aWhjaXFpCmo3dDJiQVdLdzdlbng1RXFzU25ZOG1PYzR2TDdNa1YyN2ZhYXp1cW8wUEtOeWJOa1grUlhIMDN4S0NDd0x0N0UKLzRDUlFHMGNkQmhBQ2szMkpadllrQmxESUZ3VmtnMHVnNGk4Snp6VjVCT2hEeWdwZUhJTDVVTkx2eGJDbVh6MAo1bXNYRktPYW1HYkFCbE9KTEZsR1R4WWdzeWtDZ1lFQXhFWWI0dFVmRmhiTmpJTUMyd1hFRXdWZkJYOFJqNzVqCjN6SkwxV3o4YWxUQmxFemZYOTZiNmg3VjFNT1NHcmlabFJ1cGpEaUFsUkhPZytDSXlPbmdISFkwd2xTaHNmemQKSDluL2dOdUZsanFuQkF3OVpaSW9hbE1zUVVER3RLSnVIejhEYzlVNzRFMGM3WldQWk1Ub0pNdFV2Zkl5T0pZSgpQODh1YnYvam4rMENnWUJaNmpzNFhKRmZRNFZCUFNtc2Z4RXg1V0ZXR3RSakxlVGpSNy83djNjbHRBWmQyL2Y1CjBUV0JQNzhxNDJ2QjlWbEMwR1d3U3dhTnZoR2VJZmw4VTVpRFRZM0dLNExQODcyeFdaSFVnclhVY0RuNWtiUmsKQXg1QlNVT05WcUZmYzhwVnMwcWtCdmJCV1hNdm1YNHBsUWNSRWM3QUFhNUoyVW9CWi8zVXU1VjIyUUtCZ0ZnVQpKanQ2N0lKYkpVN2pGQXI1NFcydndWNlVFV3R5UXh0TVZOK29FdlljcHVwSVBRMm10azB3SFVGbnFrODNmQ1IvCnoyeFBodFJlczFCWEdNc2d1U1BNb0F4OU1qclBnT1BrVGxhakxLV29HSDhtaHY3bndoOUV4OTFZbGxORmVTbW8KZTRJbHRNTUpsK3UrYkNVS2dDclMzR3FKSDZScElDbDBiaC85MFVaWkFvR0FaUEsrdldLQ0N6aHNhSnVWak1VSQpiTEJlMi9CM0xxTVBhakFLTjVTNU9GYlpBZm5NeE9BT1lnd25iWmdpZGVkcVk2QkIyLytVVGt4MW1IUjhKcmpGCnRyN20wS2VvRFY4dmQxSENvSkF3b2hqQ1B6SkJhSW9WYWNkRFNsMDNIOVFEck4yd0RFYUxoWFBlVkRoNGZ2NmQKa3d6V3FZWUlETzRKQlp5L21Wa0t4NFU9Ci0tLS0tRU5EIFBSSVZBVEUgS0VZLS0tLS0K
|
||||
kind: Secret
|
||||
metadata:
|
||||
name: kong.proxy.example.secret2
|
||||
type: kubernetes.io/tls
|
||||
@@ -2,9 +2,7 @@
|
||||
# use single image strings instead of repository/tag
|
||||
|
||||
image:
|
||||
unifiedRepoTag: kong:2.6
|
||||
proxy:
|
||||
type: NodePort
|
||||
unifiedRepoTag: kong:3.4.1
|
||||
|
||||
env:
|
||||
anonymous_reports: "off"
|
||||
@@ -12,4 +10,4 @@ ingressController:
|
||||
env:
|
||||
anonymous_reports: "false"
|
||||
image:
|
||||
unifiedRepoTag: kong/kubernetes-ingress-controller:2.0.2
|
||||
unifiedRepoTag: kong/kubernetes-ingress-controller:3.0
|
||||
@@ -0,0 +1,14 @@
|
||||
ingressController:
|
||||
enabled: false
|
||||
|
||||
image:
|
||||
repository: kong/kong-gateway
|
||||
tag: "3.4.0.0"
|
||||
|
||||
readinessProbe:
|
||||
httpGet:
|
||||
path: "/status"
|
||||
port: status
|
||||
scheme: HTTP
|
||||
initialDelaySeconds: 1
|
||||
periodSeconds: 1
|
||||
@@ -28,19 +28,14 @@ ingressController:
|
||||
podLabels:
|
||||
app: kong
|
||||
environment: test
|
||||
# - podSecurityPolicies are enabled
|
||||
podSecurityPolicy:
|
||||
enabled: true
|
||||
# - ingress resources are created with hosts
|
||||
admin:
|
||||
type: NodePort
|
||||
ingress:
|
||||
enabled: true
|
||||
hostname: admin.kong.example
|
||||
annotations: {}
|
||||
path: /
|
||||
proxy:
|
||||
type: NodePort
|
||||
ingress:
|
||||
enabled: true
|
||||
hostname: proxy.kong.example
|
||||
|
||||
@@ -3,8 +3,12 @@
|
||||
# - stream listens work
|
||||
# - a mixture of controller, Kong, and shared volumes successfully mount
|
||||
# - watchNamespaces is set
|
||||
# - the admission webhook is enabled; has the timeout explicitly set
|
||||
ingressController:
|
||||
enabled: true
|
||||
admissionWebhook:
|
||||
enabled: true
|
||||
timeoutSeconds: 5
|
||||
env:
|
||||
anonymous_reports: "false"
|
||||
customEnv:
|
||||
@@ -21,13 +25,11 @@ env:
|
||||
database: "postgres"
|
||||
# - ingress resources are created without hosts
|
||||
admin:
|
||||
type: NodePort
|
||||
ingress:
|
||||
enabled: true
|
||||
hosts: []
|
||||
path: /
|
||||
proxy:
|
||||
type: NodePort
|
||||
ingress:
|
||||
enabled: true
|
||||
hostname: proxy.kong.example
|
||||
@@ -43,9 +45,6 @@ proxy:
|
||||
parameters:
|
||||
- ssl
|
||||
|
||||
# - PDB is enabled
|
||||
podDisruptionBudget:
|
||||
enabled: true
|
||||
# update strategy
|
||||
updateStrategy:
|
||||
type: "RollingUpdate"
|
||||
|
||||
Some files were not shown because too many files have changed in this diff Show More
Reference in New Issue
Block a user